CERT Insider Threat Center, a research arm of Carnegie Mellon University’s Software Engineering Institute (SEI). They have defined an insider threat as: …the potential for individuals who have or had authorized access to an organization’s assets to use their access, either maliciously or unintentionally, to act in a way that could …
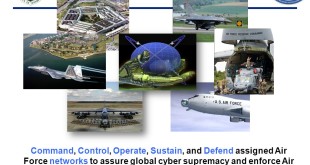
Read More »USAF develops Joint cyber operations platform for the execution of full-spectrum cyberspace operations from the operational through tactical levels of warfare
Developing and delivering air superiority for the highly contested environment in 2030 requires a multi-domain focus on capabilities and capacity, according to the unclassified version of the Air Superiority 2030 Flight Plan. “After 25 years of being the only great power out there, we’re returning to a world of great …
Read More »DARPA MRC developed resilient cloud services that would continue to operate and support military objectives despite being hit by a cyberattack
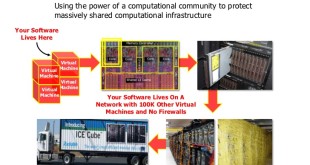
Cloud computing has burst recently into technology and business scene promising great technical and economic advantages, like offering On-demand provisioning of computer services, improved flexibility and scalability as well as reducing costs. Another attractive point of the cloud is its ability to enable a mobile workforce, which brings enhanced flexibility …
Read More »U.S., Britain blame Russia for global cyber attack targeting Network Infrastructure Devices
The United States and Britain in 2018 accused Russia of launching cyber attacks on computer routers, firewalls and other networking equipment used by government agencies, businesses and critical infrastructure operators around the globe. Network infrastructure consists of interconnected devices designed to transport communications needed for data, applications, services, and multi-media. Routers …
Read More »DARPA’s Transparent Computing programme for defeating complex, sophisticated and stealthy long-term Advanced Persistent Threats ( APTs)
Modern computing systems are essentially black boxes that accept inputs and generate outputs, but provide little-to-no visibility of their inner workings, according to DARPA. It can therefore be extremely challenging to detect an intruder, particularly an ‘Advanced Persistent Threat’: a form of attack in which the adversary slowly and deliberately …
Read More »NATO Conducts Locked Shields 2018: World’s Largest International Live-fire Cyber Defense Exercise to train security experts in Cyberwarfare
The urgency behind NATO’s deepening interest in cyber defense is driven by the increasing sophistication of cyberthreats against member states, according to Brig. Gen. Christos Athanasiadis, assistant chief of staff cyber at SHAPE. NATO reported earlier this year that its infrastructure came under threat from 500 cyberattacks monthly in 2016.The …
Read More »DARPA CHESS Program plans for human intellect teamed with autonomous technology for cyber defense
The Department of Defense (DoD) maintains information systems that depend on Commercial off-the-shelf (COTS) software, Government off-the-shelf (GOTS) software, and Free and opensource (FOSS) software. Securing this diverse technology base requires highly skilled hackers who reason about the functionality of software and identify novel vulnerabilities. This process requires hundreds or thousands of hours of …
Read More »Smartphones increasingly vulnerable from hacking and spying through malware attacks, holes in hardware, Geolocation devices and cameras
Today, mobile devices are coming under increasing attack. The number of mobile malware is rapidly on the rise with malicious activities, such as stealing users data, sending premium messages and making phone call to premium numbers that users have no knowledge. Ransomware, banking malware, and other threats aimed at …
Read More »Cyber domain command and control should be resilient, survivable, and reliable supported by Artificial intelligence (AI), automation, and the cloud technologies
NATO ministers have designated cyber as an official operational domain of warfare, along with air, sea, and land. Cyber warfare has developed into a more sophisticated type of combat between countries, where you can destroy communications infrastructure, said Marc Rogers, Head of Security for DefCon, adding that ordinary people become …
Read More »Scientists develop FontCode, that hides information by imperceptibly changing the shapes of fonts in text.
Wikipedia defines Steganography is the practice of concealing a file, message, image, or video within another file, message, image, or video. The word steganography combines the Greek words steganos (στεγανός), meaning “covered, concealed, or protected,” and graphein (γράφειν) meaning “writing”. For example, the hidden message may be in invisible ink …
Read More » International Defense Security & Technology Your trusted Source for News, Research and Analysis
International Defense Security & Technology Your trusted Source for News, Research and Analysis