Introduction:
The cyber battlefield is a global one, and effective defense requires shared strategies and unified tactics. Recognizing this reality, the UK’s National Cyber Security Centre (NCSC) made a critical move in August 2023: it became the first national cyber security agency to contribute to the Internet Engineering Task Force (IETF) by publishing an RFC (Request for Comments) on Indicators of Compromise (IoCs)– a crucial tool in the cyber defender’s arsenal.
This RFC, numbered 9424, marked the NCSC’s inaugural contribution to the Internet Engineering Task Force (IETF), a pivotal international standards body. This article delves into the background of the RFC, the importance of standards, and the broader implications for the cyber security landscape.
The World of Standards:
Standards, in this context, refer to mutually agreed-upon documents that delineate how various aspects should be manufactured or define best practices. While standards cover a vast array of subjects, those pertaining to the functioning of the internet hold particular significance. The IETF, as the Internet Engineering Task Force, is the principal international standards body responsible for designing key internet protocols, including IP, TLS, and QUIC.
Anyone can participate in the IETF. Most participants are from industry, but academia, government and not-for-profit groups are all represented too. The IETF publishes standards called RFCs, which can define protocols or provide an informative reference, as our document does.
What is an RFC and why are IoCs crucial?
Think of an RFC as a blueprint for the internet’s infrastructure and protocols. They define the language and standards that devices and networks use to communicate and work together. An RFC on IoCs, like the one published by the NCSC, provides standardized guidelines for identifying and sharing malicious activity across the globe. IoCs can be anything from suspicious IP addresses to malware signatures, acting as red flags for defenders to detect and thwart cyberattacks.
Understanding IoCs:
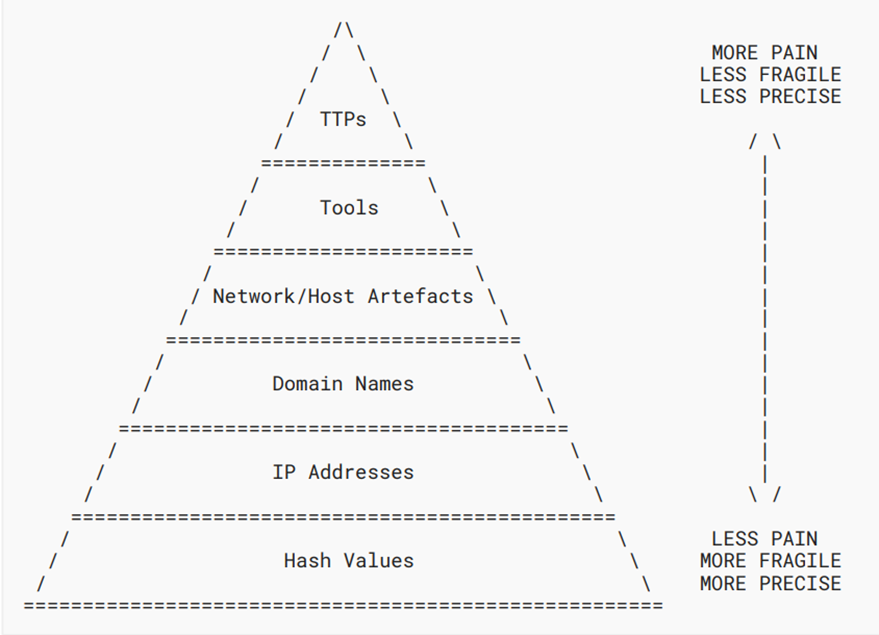
The RFC authored by the NCSC serves as an introduction to Indicators of Compromise, which are observable artifacts associated with cyber attackers. These indicators, such as domain names for phishing sites or IP addresses of malware servers, offer a streamlined method for detecting and attributing malicious activity. The document covers the IoC lifecycle, the ‘pyramid of pain’ illustrating the impact of different IoCs, and real-world examples of IoCs used in response to threats.
The ‘Pyramid of Pain’:
As depicted in ASCII art within RFC9424, the ‘pyramid of pain’ categorizes IoCs based on the level of difficulty for an attacker to change them. This strategic perspective aids in understanding which IoCs are more resilient against evasive tactics by cyber adversaries. The article explores how tactics, techniques, and procedures (TTPs) fit into this pyramid, providing a nuanced understanding of tracking attackers.
The Role of Standards Bodies:
Highlighting the significance of standards bodies, the article emphasizes that these organizations shape the design decisions that define the internet’s future. The IETF, in particular, serves as a platform where industry, academia, government, and non-profit groups converge to create and refine standards.
The IETF is the Internet Engineering Task Force – the international standards body responsible for designing the most important protocols on the internet today. This includes IP (Internet Protocol), TLS (Transport Layer Security), QUIC (which stands for, um, QUIC) and many, many others. Participating in such bodies offers an early glimpse into upcoming technologies and provides an opportunity to contribute expertise to the design process.
NCSC’s Involvement in Standards:
The NCSC has actively participated in the IETF, contributing to various working groups and research endeavors. The article underscores the importance of engaging in standards bodies to grasp the evolving landscape of the internet. Furthermore, it encourages subject matter experts and stakeholders from UK academia and industry to join these forums, bringing real-world attack and defense considerations to enhance cyber resilience.
Why is the NCSC’s contribution so important?
Until now, IoC sharing lacked universal standards, creating communication obstacles and hampering global collaboration. The NCSC’s RFC brings much-needed clarity and structure to this vital process. By establishing a common language and format for sharing IoCs, the NCSC is breaking down barriers and fostering effective cross-border cooperation. This translates to faster detection, quicker response times, and ultimately, a more resilient cyberspace for all.
The ripple effect: Global reach and future impact
The NCSC’s pioneering effort sets a precedent for other national cyber security agencies and industry players to follow. As more entities contribute to the IETF with their expertise, a robust, international framework for IoC sharing will emerge. This will empower defenders worldwide to identify threats sooner, anticipate attack patterns, and share tactics efficiently, creating a united front against cybercrime.
Conclusion:
As the digital landscape continues to evolve, active involvement in standards bodies becomes imperative for shaping a resilient and secure future. The NCSC’s RFC is not just a technical document; it’s a symbol of global cooperation and a commitment to building a safer digital future. By standardizing the way we identify and share threats, the NCSC is taking a critical step towards a more resilient and secure cyberspace for everyone. In the ever-evolving landscape of cyber threats, collaboration is key, and the NCSC’s leadership in setting international standards paves the way for a more secure and interconnected world.
References and Resources also include:
https://www.ncsc.gov.uk/blog-post/rfc-indicators-of-compromise-for-ietf
 International Defense Security & Technology Your trusted Source for News, Research and Analysis
International Defense Security & Technology Your trusted Source for News, Research and Analysis