Bitcoin is a digital currency that allows for the transfer of payment between two parties, without the help of a bank—and without government oversight. On average, more than 250,000 bitcoin transactions occur every day, and with a market capitalization in excess of $66 billion, bitcoin has become the largest cryptocurrency in …
Read More »GPS III and NTS-3 Satellites will provide higher acccuracy, jam resistance, and new navigation warfare (NAVWAR) capabilities to US DOD
The Global Positioning System (GPS), is a global navigation satellite system (GNSS) that provides location and time information in all weather conditions, anywhere on or near the Earth where there is an unobstructed line of sight to four or more GPS satellites. GPS has become ubiquitous technology that provides real-time …
Read More »Cyber Security of Industrial control systems (ICS) and SCADA systems
Industrial control system (ICS) is a collective term used to describe different types of control systems and associated instrumentation, which include the devices, systems, networks, and controls used to operate and/or automate industrial processes. Depending on the industry, each ICS functions differently and are built to electronically manage tasks efficiently. …
Read More »Mobile security
The future of computers and communication lies with mobile devices, such as laptops, tablets and smartphones with desktop-computer capabilities. Their size, operating systems, applications and processing power make them ideal to use from any place with an internet connection. And with the expansion of ruggedized devices, the Internet of Things …
Read More »Cyberbiosecurity threats, vulnerabilites and cyberbiosecurity technologies
The life sciences now interface broadly with information technology (IT) through its industrial applications in health care, agriculture, manufacturing, automation, artificial intelligence, and synthetic biology. The information moves between living and cyber systems in a two-way flow. Global public health crises create conditions of extreme fragility where dual-use technologies …
Read More »Growing Cyber threats to commercial aviation require cyber risk management, and resilient systems
Cyber attacks are growing in number and sophistication affecting large corporations, critical infrastructures of all kinds, governments to SMEs, and increasingly the aviation industry. Commercial aviation plays a central role in our daily lives and is an essential part of the national economy. The number of passengers rose from …
Read More »Cyberwarfare among US, China and Russia driving Secure Internets cyber technologies
Cyber warfare has developed into a more sophisticated type of combat between countries, where you can destroy critical infrastructure such as power, telecommunications or banking by damaging the computer systems that control those infrastructures. It’s widely acknowledged that offensive cyberattacks will be a necessary component of any future military campaign, …
Read More »Optical Networks Vulnerabilities and Security threats
Optical networks are vulnerable to several types of security breaches or attacks, typically aimed at disrupting the service or gaining unauthorized access to carried data, i.e., eavesdropping. Depending on the aim of the attack, security breaches can induce financial losses to the clients or cause network-wide service disruption, possibly leading to huge …
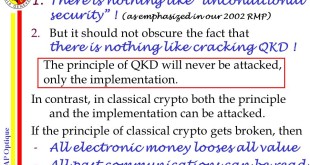
Read More »Quantum cryptography (QC) or Quantum key distribution (QKD) are assumed hackproof but its implementations have vulnerabilities
Quantum computers could undermine almost all of the encryption protocols that we use today. Though quantum computers are still quite some way from being practical, usable machines, once they become so, we could be looking at a whole new world when it comes to online privacy — one in which …
Read More »Cyber Moonshot and Accelerating Security of Systems with Emerging Technologies (ASSET)
The nation’s critical infrastructure is increasingly dependent on the Internet, while cybersecurity attacks are on the rise. Cybersecurity threats are becoming more frequent, more sophisticated, and more destructive—gradually eroding society’s trust in digital infrastructure. As technology continues to advance and every facet of daily life becomes increasingly interconnected, both the …
Read More » International Defense Security & Technology Your trusted Source for News, Research and Analysis
International Defense Security & Technology Your trusted Source for News, Research and Analysis