Non-lethal weapons have been used by security forces to deter hostile crowds. They fill gaps …
Read More »Masonry Layout
Rising Green alternatives to fossil-based jet kerosene driven by rising global and military aircraft industry and concern of emissions
Global aviation fuel market was valued at US$178.560 billion in 2019 and is expected to …
Read More »Continuing interest of Space agencies and Militaries to exploit Zero-Point Energy for applications like propulsion and for generating electric power.
Zero-point energy is the energy that remains when all other energy is removed from a …
Read More »Militaries developing scalable hundreds of Kilowatts to Megawatts High Power Laser technologies for air and missile defense
The Laser Directed Energy Weapons (DEWs) offer a transformational ‘game changer’ to counter asymmetric and …
Read More »Navies developing cyber security measures and cyber defense technologies to counter growing cyber threats
Ships are increasingly using systems that rely on digitization, integration, and automation. Offensive actors understand the …
Read More »Quantum engineering established at leading universities world-wide to realize quantum hardware of quantum computers, cryptography and sensors
Traditionally, quantum science has been a domain of fundamental research explored mostly by physicists. At the …
Read More »Flexible displays enable lighter-weight, lower-power, more-rugged smartphones , soldiers wearable and vehicle applications
With the flat panel display having already been widely used more than 40 years, there …
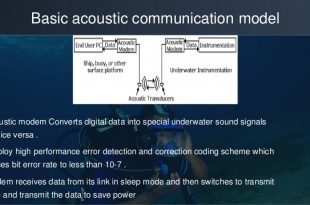
Read More »Underwater Acoustic Wave (UWAC) Communication technologies including Acoustic Modems enable Unmanned Underwater Vehicles (UUWs) missions
Approximately 70% of the Earth’s surface is covered by water, yet almost 95% of the …
Read More »Fuel cells technologies enabling less expensive, durable, eco friendly power on-demand for transportation and military systems
Since the Industrial Revolution, the environmental impacts of energy have posed a concern. Recently, this …
Read More »Heterogeneous computing architecture for emerging digital warfare
The world of high-performance computing is particularly challenging, as new flavors of sophisticated sensors, complex …
Read More » International Defense Security & Technology Your trusted Source for News, Research and Analysis
International Defense Security & Technology Your trusted Source for News, Research and Analysis