Brain-Computer Interfaces (BCIs) are bidirectional devices that allow communication between the brain and external systems, such as computers. Every action our body performs begins with a thought, and with every thought comes an electrical signal. The electrical signals can be received by the brain-computer interface, consisting of an electroencephalograph (EEG) or an implanted electrode, which can then be translated, and then sent to the performing hardware to produce the desired action.
There are various techniques for picking up signals from the brain. This can be done, for example, on the outside of the brain with sensors. Commercial manufacturers such as NextMind or Emotiv offer headbands for playing computer games or controlling the lighting in a house. In contrast, with the semi-invasive method, the sensors are located under the skull and on top of the brain. Even beyond that, in the full-invasive method, the sensors are located inside the brain. A well-known example is Deep Brain Stimulation, a medical application used by some patients with Parkinson’s disease.
The BCI acts as a bridge between the brain and external devices. The aim of BCI is to convey human intentions to external devices by directly extracting brain signals. Eventually, the brain and computers would be highly integrated. On the one hand, BCI systems permit the acquisition of neuronal data, study of the status of the brain, and control of external devices such as wheelchairs or prosthetic devices. On the other hand, they are used for neurostimulation procedures to stimulate targeted regions of the brain.
Brain-computer interfaces are being applied in neuroprosthetics, through which paralyzed persons are able to control robotic arms, neurogaming where one can control a keyboard, mouse, etc using their thoughts and play games, neuro analysis (psychology), and in defense to control robotic soldiers or fly planes with thoughts. These devices are employed for controlling exoskeletons, aiming to restore lost motor functionality or even improve natural human strength.
One of these military application scenarios is systems able to monitor soldiers’ mental state, assessing the cognitive and emotional response against complex situations. They are also being researched to augment soldiers’ mental capabilities in physical, cognitive, and emotional dimensions. Additionally, they could serve as systems to mentally transmit commands between individuals, improving the telecommunication systems on the battlefield.
BCI threats and vulnerabilities
BCI are also vulnerable to privacy and security threats. The emerging security concerns include neuro-ethics, neuro-confidentiality, neuro-integrity, neuro-security/privacy, and brain data hacking.
Companies who opt to use BCI technology to collect private information about employee in the workplace. Even when used with the best of intentions, companies could risk becoming overly dependent on using brain data to evaluate, monitor, and train employees, and there are risks associated with that.
Recent experimental results show how electroencephalographic (EEG) signals, recorded from consumer-grade BCI devices, can be used to extract private information about a user. With sufficient computational power, this information can be exploited by others to make inferences about our memory, intentions, conscious and unconscious interests, as well as about our emotional reactions.
The typical brain-computer interfaces consist of acquisition devices that capture the brain’s neural signals After the signal acquisition, BCI systems transform these analog signals into digital signals. Then, using signal processing, the features are extracted and classified. Then, finally, the signal output is sent to BCI applications. So far, most studies in this area have focused on developing BCI classifiers that are faster and more reliable, rather than investigating their possible security vulnerabilities.

BCI technology for the mass market collects information — processing it through an app before sending messages back to the user, whether it’s a physician, therapist or company collecting the data for a specific purpose. The attacker can intercept the transmission, save brain neural signals, and decompose the raw signals to obtain private information.
BCI are also vulnerable to hacking. Hackers can access a BCI headband and create/send manipulated EEG data. A hacker could also intercept and alter all data transmitted by your BCI. It’s possible that a hacker could steal your “passthoughts” user credentials and interact with your devices (laptop, car, etc.). The technology is premature, Usieto explained, and any mishandling could lead to abuse of confidential data regarding an individual’s health, personal preferences and emotions, said cybersecurity expert Pablo Ballarin Usieto.
BCI devices may give access not only to a user’s psychological information, but to private information like PINs and passwords, as well. The captured EEG signal could reveal the user’s private information about, e.g., bank cards, PIN numbers, area of living, the knowledge of the known persons.
Additionally, attackers could use malware strategies to affect data integrity and data confidentiality, compromising the normal functioning of the system. Furthermore, attackers could inject false signals or modify the signal to jeopardize the safety of prosthetic limbs of patients to give dangerous movement to patients injuring themselves or others.
If a malicious actor were to gain access to a user’s BCI, it could lead to paralyzation, severe brain damage or even potentially a loss of life. They could also be used by criminals to manipulate thoughts or even cause death or used to control soldiers’ brains and their actions. According to some Analysts, Human Brain is going to become the sixth warfighting domain.
The manufacturers of BCI devices focus on application development, without paying much attention to security and privacy-related issues. Privacy and security issues arising from the misuse of BCI devices is an important issue that deserves immediate attention and the development of suitable countermeasures.
Moreover, as more BCIs start involving wireless communication, the security vulnerabilities are also getting further multiplied. The smartphone-based BCI applications are prone to attacks that originate in the mobile device itself. Therefore, most of the possible attacks on smartphone issues could also be considered as security and privacy issues of smartphone-based BCI applications.
The recent rise in mobile malware has made Mobile phones vulnerable to data leakage and tempering of sensitive information such as business documents, bank details, credit card information, and make purchases. These applications can access private data which is acquired from BCI devices and stored in smartphones or SD card. This data can be illegally transferred by malware to a remote server (e.g., privilege escalation attacks. Developers of malware can analyze the private signals and attack the users of BCI devices.
There can be cryptographic attacks aiming to disrupt the encryption mechanisms used to protect the transmitted data between BCI devices and computers, being essential to implement robust cryptographic systems. There can be jamming attacks focused on emitting electromagnetic noise could prevent the electrodes from acquiring neural data.
There can be replay and spoofing attacks over BCI systems, where the attacker acquires legitimate neuronal signals from a user, later retransmitting them to the medium. These could be particularly damaging in BCI authentication scenarios, where the attacker obtains the neural signals able to authenticate a user, used later to gain control over the protected assets
Adversarial attacks on Machine learning
In recent years, advances in machine learning (ML) have enabled the development of more advanced BCI spellers, devices that allow people to communicate with computers using their thoughts. Recent research, however, suggests that machine learning algorithms can sometimes be fooled by attackers, whether they are used in computer vision, speech recognition, or other domains.
Researchers at Huazhong University of Science and Technology have recently carried out a study investigating the security of EEG-based BCI spellers, and more specifically, how they are affected by adversarial perturbations. Their paper, pre-published on arXiv, suggests that BCI spellers are fooled by these perturbations and are thus highly vulnerable to adversarial attacks. “This article aims to expose a critical security concern in EEG-based BCI spellers and more broadly, EEG-based BCIs, which has received little attention before,” Dongrui Wu, one of the researchers who carried out the study, told TechXplore. “It shows that one can generate tiny adversarial EEG perturbation templates for target attacks for both P300 and steady-state visual evoked potential (SSVEP) spellers, i.e., mislead the classification to any character the attacker wants, regardless of what the user-intended character is.”
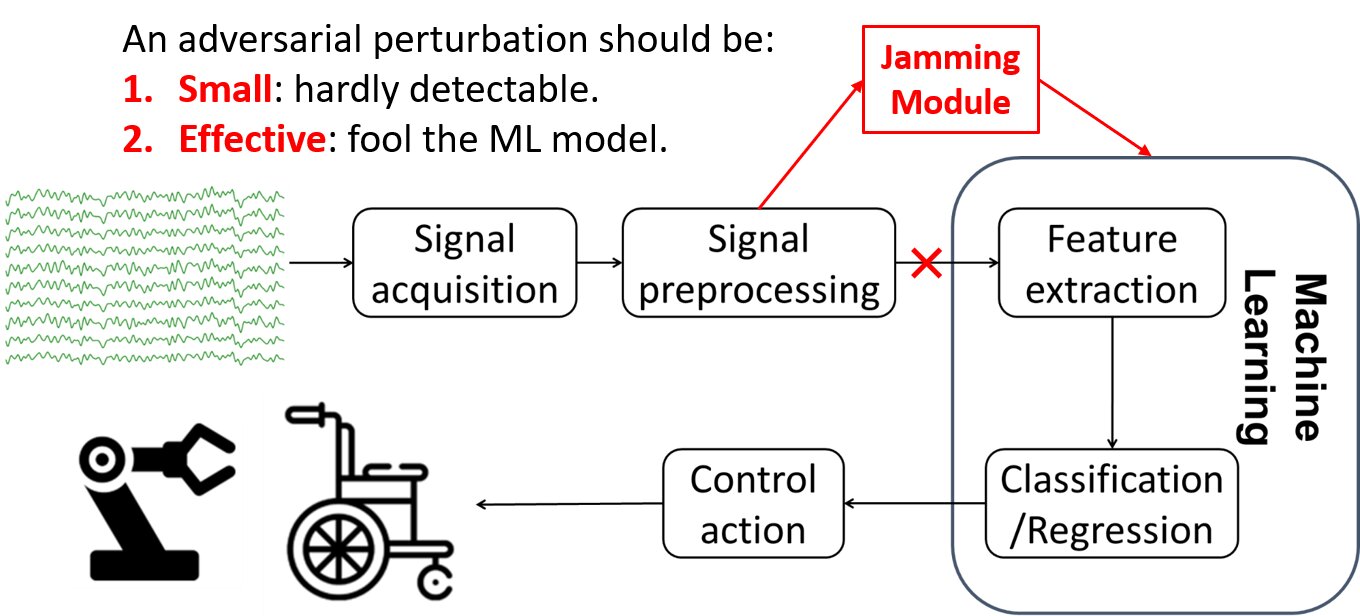
P300 BCI spellers are already used in several settings, including in clinics, to evaluate or detect disorders of consciousness. Adversarial attacks to BCI spellers could thus have numerous consequences, ranging from simple usability issues to severe patient misdiagnoses. “We believe that a new and more detailed understanding of how adversarial EEG perturbations affect BCI classification can inform the design of BCIs to defend against such attacks,” Wu explained.
“Defending adversarial attacks is a common research problem in many applications of machine learning, e.g., computer vision, speech recognition, and BCIs,” Wu said. “If we know the approach the attacker takes, then we can develop strategies to defend against it, just like how we defend against computer viruses: a virus breaks out first and then we find ways to kill it.”
Attackers are always trying to come up with new ways to circumvent security measures, so it is important for researchers to continue investigating system vulnerabilities and come up with new security measures. While it is unavoidable for targeted security solutions to be developed after a specific vulnerability has been identified, uncovering general issues with a system and taking precautions can be very useful.
BCI Cybersecurity
In 2019, the Organisation for Economic Co-operation and Development (OECD) emphasized that there are major risks surrounding brain-computer interfaces. This warning was followed in 2021 by the UNESCO Bioethics Committee, with a report stating that there is hardly any legislation on neurotechnology. Yet, countries are still not doing enough in this area. Currently, Chile is leading the way in creating proper legislation. In 2020, the Chilean parliament passed a law to establish neuro rights. The aim of this legislation is to give personal brain data the same status as an organ so that it cannot be bought or sold, trafficked or manipulated.
Proper legislation is only one key aspect ensuring that this technology is used wisely. BCI manufacturers also need to protect their users. Especially when it comes to valuable and intangible affairs as someone’s thoughts, emotions, feelings and the biological brain.
BCI safeguards and Security technologies
The concept of security, refers to the “protection of information and information systems from unauthorized access, use, disclosure, disruption, modification, or destruction to provide integrity, confidentiality and availability”.
- Integrity is “protection against unauthorized modification or destruction of information. A state in which information has remained unaltered from the point it was produced by a source, during transmission, storage, and eventual receipt by the destination”.
- Confidentiality: “preservation of authorized restrictions on access and disclosure, including means for protecting personal privacy and proprietary information”.
- Availability: “property that data or information is accessible and usable upon demand by an authorized person.”
- Safety: “freedom from conditions that can cause death, injury, occupational illness, damage to or loss of equipment or property, or damage to the environment.” This work considers the safety concept from the physiological, psychiatric, and psychological perspectives
It is vital that security considerations span the entire lifecycle of a BCI, from secure design, secure and safe surgery and implant (where BCIs are invasive), secure operation, and secure decommissioning.
Supply Chain Threats – The production of hardware devices involves multiple suppliers at various stages of the production and support lifecycle, so it’s important that all BCI manufacturers follow strict process and governance around supply chains.
There are some appropriate safeguards in the design of the neuromedical applications which can be deployed in the coming years. . Some of the potential solutions for these issues could be as complicated as maintaining firmware updates to ensure the device has the necessary security updates to simply having a shutdown switch for the BCI device should it be compromised. The communication between neural implantable devices and patients must be kept confidential. The information should be transmitted in an encrypted format
Authentication is a process that ensures and confirms a user’s identity. Using EEG brain signals as authentication measure has been proposed in many literatures and proved to be effective. BCI devices record brainwave signals when a subject performs a custom task (e.g., singing, breathing or finger movement). Then, brain signals are wirelessly transmitted to a computer application which collect and process this data. Their authentication system analyses the similarity between such brain data and training data to authenticate subjects.
The privacy risks implementing BCI can be overcome, Javier Minguez, Usieto’s research collaborator, told Digital Privacy News. He also is co-founder and chief technology officer at Bitbrain, a neurotechnology company also based in Spain. First, anonymity during the data-collection process cannot be understated. “The most-important aspect to address when acquiring the data is to comply with European GDPR, which is very strict,” Minguez said. Taking effect in May 2018, the U.K.’s General Data Protection Regulation sets limitations on what organizations can do with any personal data they collect across Europe. “There are many points that we need to address, but one of the most relevant for privacy is that the personal data always needs to be dissociated from the biomedical data,” Minguez said.
He also recommended using two protection layers with the BCI technology, though with a single encryption. The first layer would be the main server, where all data is stored. To ensure anonymity, an individual’s biometric and personal data should be encrypted and housed in different folders during this stage, Minguez explained. The second layer would be a corporate cloud server, where only the biometric data — having been encrypted in the main computer — is stored.
The adversary can even attack the authentication system via synthetic EEG signals, using EEG generative model based on the historical EEG data from a subject can also attack the authentication system. One of the countermeasures would be to use multiple authentication signals (e.g., the signals of singing, breathing, or being shocked). Besides, we can combine the existing authentication methods on smartphone device to perform multidimensional authentication.
BCI Interface Security – BCIs will need to communicate data out from the brain (and possibly back into the brain by way of stimuli); so it’s important that these communications are conducted in a safe and secure way. This could involve new ways to authenticate access to BCIs and considerations around preventing jammed communications.
All smartphones, as computers, are preferred targets of attacks. These attacks exploit weaknesses inherent in smartphones that can come from the communication mode—like Short Message Service (SMS), Multimedia Messaging Service (MMS), wifi, Bluetooth and GSM, the de facto global standard for mobile communications. There are also exploits that target software vulnerabilities in the browser or operating system. And some malicious software relies on the weak knowledge of an average user.
Companies are now incorporating security counter-measures in smartphones, from security in different layers of software to the dissemination of information to end users. The first layer of security in a smartphone is the operating system (OS). Beyond needing to handle the usual roles of an operating system (e.g. resource management, scheduling processes) on the device, it must also establish the protocols for introducing external applications and data without introducing risk. Above the operating system security, there is a layer of security software. This layer is composed of individual components to strengthen various vulnerabilities: prevent malware, intrusions, the identification of a user as a human, and user authentication. Smartphones are providing end-to-end encryption on some widely-used messaging apps to delivering rapid updates of security patches .
In the future, more effective countermeasures should be proposed to guarantee that neuromedical applications are not only safe and effective, but also these applications are robust enough to prevent attacks.
University of Washington’s BioRobotics Lab BCI security project
This project focuses on making improvements to privacy and security properties of BCI-enabled technologies. In doing so, the project consists of two major steps. The focus of the first step is to identify which components of an electroencephalography (EEG) signal can be used to extract private information. After identifying potential vulnerabilities, the researchers will quantify the amount of exposed information.
Based on the obtained results, the focus of the second step is the development of a software tool, aimed at preventing potential extraction of users’ private information. The proposed tool, referred to as the “BCI Anonymizer”, is based on hypothesis that recorded brain signals can be decomposed into a collection of characteristic signal components in real time. From these components, one can extract information corresponding to a user’s intended BCI commands, while filtering out any potentially private information.
The aims of this project are expected to enhance the development of the closed-loop brain-controlled interfaces. The knowledge of how to extract private information from the recorded brain signals, and more importantly, how to decompose recorded signals to prevent the potential private information leakage, will advance the ability to select useful control commands from the brain in real time.
Moreover, as more BCIs start involving wireless communication, this project will provide enabling technology for addressing the emerging security and privacy issues.
References and resources also include:
http://brl.ee.washington.edu/neural-engineering/bci-security/
https://techxplore.com/news/2020-02-unveils-vulnerabilities-eeg-based-brain-computer-interfaces.html
 International Defense Security & Technology Your trusted Source for News, Research and Analysis
International Defense Security & Technology Your trusted Source for News, Research and Analysis