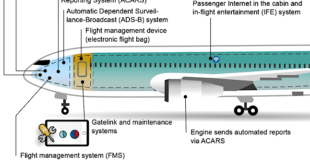
Avionics are the electronic systems used on aircraft. Aircraft avionics is the most crucial component of aircraft systems and helps in providing various operational and virtual information in-flight and on the ground. The avionics system receives data from the air traffic management system and feeds this information to the pilot …
Read More »Growing cyber attacks require Organization Incident response plan
The accelerating pace of digitalisation, fuelled by the COVID-19 pandemic, has led to a record-breaking year for cybercrime with ransomware attacks rising 151 per cent in 2021, and an average of 270 cyberattacks per organisation being faced, a new study showed in Jan 2022. The World Economic Forum’s ‘Global …
Read More »Critical Infrastructure Protection Market
Networked technologies touch every corner of the globe and every facet of human life. They have driven innovation, nurtured freedoms, and spurred economic prosperity. Even so, the very technologies that enable these benefits offer new opportunities for malicious and unwanted cyber activities. Cyber-attacks are continuously growing in size and breadth, targeting …
Read More »DARPA HACMS employed Formal Verification Methods to develop hack proof unmanned vehicles , weapons , satellites, and command and control systems
In 2011, Iran claimed to have downed a sophisticated American stealth drone, and unveiled what it alleged was a reverse-engineered copy of the futuristic looking RQ-170 Sentinel UAV, produced by defense giant Lockheed Martin. The drone was brought down by the Iranian Armed Forces’ electronic warfare unit which commandeered the …
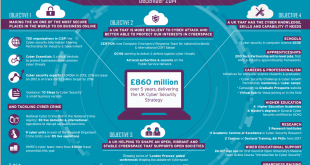
Read More »UK Cyber Security Strategy emphasizes Defence , Deterrence and Cyber technology development
The rapid development of digitalized services and online shopping in the UK has been paralleled with significant growth in cybercrime, leading to greater spending on security in public and private sectors. Organizations’ IT footprints have also become increasingly complex, driving demand for more sophisticated and bespoke cyber solutions. There …
Read More »US DOD establishing Cyber Ranges and testbeds with Live-Virtual-Constructive (LVC) simulation under CyberWarfare Threat
As World is becoming more digitized, its National Critical Information Infrastructure assets in critical sectors like energy, banking, defence, telecom, transportation etc. have becoming more vulnerable to cyber attacks like the use of ransomware to hold assets at risk, disabling of CII threatening domestic public safety. In the Future, IOT will …
Read More »5G Mobile Networks deployments have many security and privacy threats, Require New policies and technologies including quantum cryptography
Countries are now racing to deploy 5G, short for 5th generation mobile networking or 5th generation wireless systems. The Fifth Generation (5G) mobile networks promise fast Internet for everyone, smart cities, driverless cars, critical health care, “internet of things” revolution, and reliable and secure communications for critical infrastructures and services. The …
Read More »Growing threat of Cryptocurrency in terrorism for terror financing
Modern terrorist attacks display increasingly sophisticated ICT skills in both conducting their attacks and communicating them globally through digital technologies, combined with, in some cases, an awareness of counter-intelligence measures, largely enabled by Web 2.0. The Paris attackers displayed the most sophisticated use of these, including so-called Dark Web platforms …
Read More »Emerging technologies sounding death knell to Privacy, requirement of new governance structures
Significant technological advances are being made across a range of fields, including information communications technology (ICT); artificial intelligence (AI), particularly in terms of machine learning and robotics; nanotechnology; space technology; biotechnology; and quantum computing. The technological advances are driven by a digital revolution and need to gather, process, and analyze …
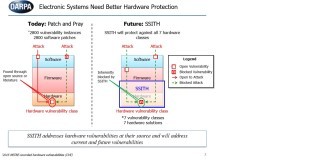
Read More »DARPA SSITH developed secure hardware architectures for Unhackable Military systems, FETT testing exploits to thwart Tampering
As 5G and IoT proliferation sweep across the planet, businesses and consumers are benefiting greatly from increased connectivity. However, this connectivity is also introducing greater risks and security concerns than ever before. As the Military and civilian technological systems, from fighter aircraft to networked household appliances, are becoming ever more …
Read More » International Defense Security & Technology Your trusted Source for News, Research and Analysis
International Defense Security & Technology Your trusted Source for News, Research and Analysis