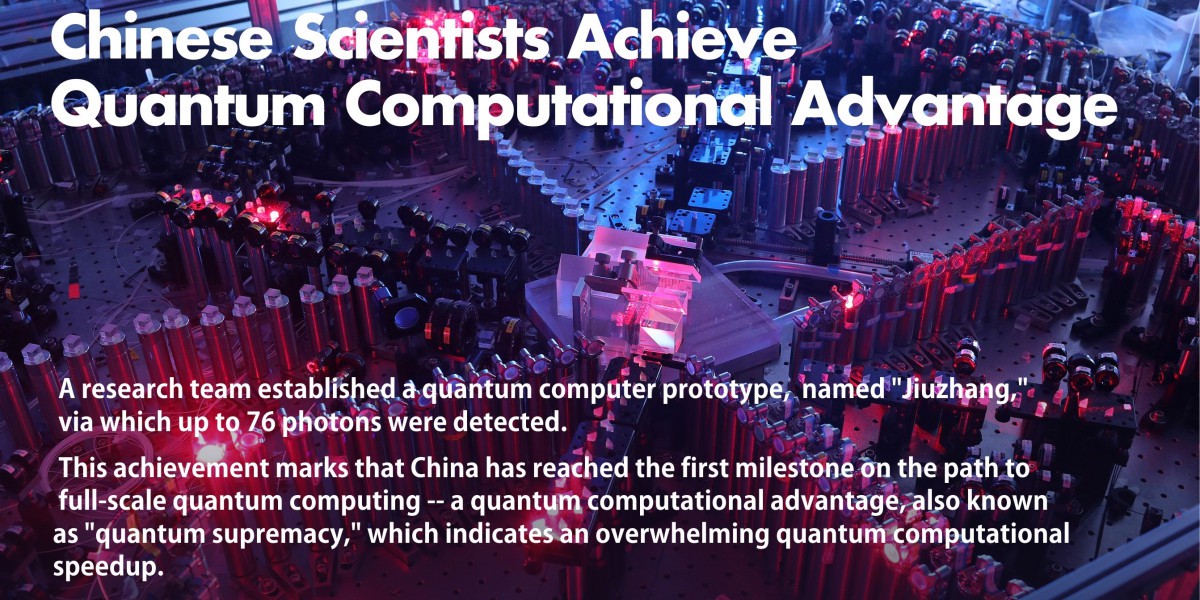
5G Mobile Networks deployments have many security and privacy threats, Require New policies and technologies including quantum cryptography

Countries are now racing to deploy 5G, short for 5th generation mobile networking or 5th generation wireless systems. The Fifth Generation (5G) mobile networks promise fast Internet for everyone, smart cities, driverless cars, critical health care, “internet of things” revolution,…...