Terahertz (THz) represents the portion of the electromagnetic radiation between the microwave and the infrared region. It is within the frequency range of 0.1–10 THz, corresponding to wavelengths of radiation from 3000 to 30 µm. The advantages of the terahertz light are that they are non-invasive, intrinsically safe, and non-ionizing, …
Read More »Monthly Archives: February 2023
Thermobaric Munitions
A thermobaric weapon (also known as an aerosol bomb or Fuel Air Explosive) is a type of weapon the used the oxygen in the surrounding environment to generate a high-temperature explosion. While conventional explosive weapons are 25% fuel and 75% oxidizer, Thermobaric weapons consist of 100%fuel and as a result, are …
Read More »Wi-Fi technologies migrating from Wi-Fi 5 to Wi-Fi 6
Bluetooth, developed in the late 1990s, is a technology designed to enable short-range wireless communication between electronic devices, such as between a laptop and a smartphone or between a computer and a television. Bluetooth works by using radio frequencies, rather than the infrared spectrum used by traditional remote controls. As …
Read More »Bluetooth technology powers everything from smartphones and wearables to smart home devices and headphones
Bluetooth, developed in the late 1990s, is a technology designed to enable short-range wireless communication between electronic devices, such as between a laptop and a smartphone or between a computer and a television. Bluetooth radio technology was developed by L. M. Ericsson in 1994. The standard is named after the …
Read More »Reduction of Magnetic Field Signature of Military Vehicles and Ships
As a vessel travels under or on the surface of water, it causes a detectable local disturbance in Earth’s magnetic field. This disturbance, referred to as the magnetic signature, makes the vessel vulnerable to enemy defense systems. In submarine warfare, adversaries use increasingly sophisticated magnetic sensor and signal processing equipment to …
Read More »Automotive Alternative Propulsion Market
Currently, most vehicles rely on internal combustion engines for locomotion; however, a significant shift toward partial and complete electrification is likely to emerge as an alternative propulsion system for vehicles. An internal combustion engine system is highly cost-effective and hence, its usage is higher than other propulsion systems. Being a …
Read More »Photonics Masts are critical subsystems of Submarine imaging, navigation, electronic warfare and communications system
A submarine is a naval platform that can stay underwater for an extended period to carry out missions, both offensive and defensive. It is a complex platform that includes multiple components. As radio waves cannot propagate in water, communication with submarines is difficult. To overcome this issue, submarines are being …
Read More »Facial recognition widely employed in commercial, Security and Military applications
Facial recognition is a way of using software to determine the similarity between two face images in order to evaluate a claim. The technology is used for a variety of purposes, from signing a user into their phone to searching for a particular person in a database of photos. …
Read More »Next-generation In-Vehicle Networking
Advances in automotive design have led to an exponential increase in vehicle electronics. Today’s vehicle design improvements are due in large part to the application of electronics to automotive systems. Vehicle functions are divided into systems and sub-systems to provide for passenger entertainment, comfort, and safety, as well as to …
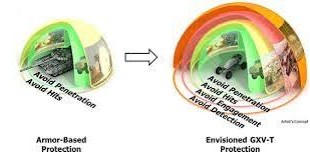
Read More »Future armored vehicles will have enhanced lethality, survivability, situation awareness, mobility and signature management
The effectiveness of anti-tank weapons used by Ukraine against Russian tanks revives old questions as well as generates new ones about armoured fighting vehicles and their future. Oryx, an open-source site tracking military-equipment losses around the world, has reported that Moscow has lost 5,020 military vehicles since the beginning of its …
Read More » International Defense Security & Technology Your trusted Source for News, Research and Analysis
International Defense Security & Technology Your trusted Source for News, Research and Analysis