Cyber warfare refers to the use of technology to launch attacks on nations, governments and citizens, causing comparable harm to actual warfare using weaponry. Cyber warfare has developed into a more sophisticated type of combat between countries, where you can destroy critical infrastructure such as power, telecommunications or banking by damaging the computer systems that control those infrastructures.
There are several benefits of pursuing cyber warfare, including the fact that these attackers are more difficult to track down. Malware, too, can lie dormant and communicate in secret with a command-and-control server until its operators decide to pull the trigger on its destructive capabilities. Quite often, nobody will initially claim responsibility for these attacks, creating havoc and confusion as victims speculate as to who may be responsible.
To date, there hasn’t been an outright “cyber war” with declared antagonists, however, there are a number of incidents that have caused serious disruption to countries’ infrastructure that are suspected of being carried out by another state. It’s widely acknowledged that offensive cyberattacks will be a necessary component of any future military campaign, and the extreme cyberweapons are being developed now.
According to the 2020 Verizon Data Breach Investigation Report (“DBIR”), there’s been an increase in state-sponsored espionage-related incidents, ranking only second after organized crime. What’s more, Google’s Threat Analysis Group (TAG) revealed in October 2020 that it had managed to absorb one of the biggest DDoS attacks in 2017 – a massive bandwidth attack of 2.5 TB per second over six months. In a separate report, Google TAG also revealed that the attack was state-sponsored, wherein the researchers could connect the dots to internet service providers in China. In February 2020, Iran announced that it faced and eliminated a DDoS against its communications infrastructure that disrupted the internet. In the same month, Chinese hackers tried to steal confidential information on Malaysian government-backed projects through its officials.
We know that Russia and China are developing cyber weapons to use in any future cyber conflict, and the US, France and Israel are just as active as nation-states leading the way in this endeavor. Russia has been accused of mounting multiple cyberattacks against Ukraine, including the BlackEnergy attack that cut the power to 700,000 homes in the country in 2015 and the NotPetya malware, which masqueraded as ransomware but was in reality designed purely to destroy the systems it infected. Russia also conducted a denial of service attack against Estonia allegedly for removing a war memorial. Russian hackers have also been reported of targeting US nuclear plants.
North Korea, which has been generating headlines over its nuclear posturing and turbulent diplomatic relationship with the US, has also been active in cyberspace. According to researchers, the North Korean state has been linked to the prolific and dangerous hacking organization codenamed HIDDEN COBRA, also known as the Lazarus Group. Both the Sony hack of 2014 and the hack of a Bangladeshi bank in 2016 were pinned on these hackers. North Korea targeted an American entertainment organization due to a movie perceived to portray their supreme leader negatively, leading to significant economic damage.
The battle has begun. “External actors probe and scan [U.S. Department of Defense (DoD)] networks for vulnerabilities millions of times each day, and over 100 foreign intelligence agencies continually attempt to infiltrate DoD networks,” Eric Rosenbach, assistant secretary for homeland defense and global security, testified before the U.S. Senate Committee on Armed Services, Subcommittee on Emerging Threats and Capabilities.
“Now we are talking about a much more sophisticated type of cyberwar where you’re infiltrating other countries, you are looking for their spy operations, you are looking for their implants, their little tricks they’ve hidden, and you’re even trying to subvert them for your own ability, or you are trying to put things in place so that in the event of a conflict you can hijack all of their stuff, steal information and gain the upper hand in terms of intelligence and in terms of destroying their communications infrastructure,” said Marc Rogers, Head of Security for DefCon.
Laura Galante, a former U.S. Department of Defense intelligence analyst who now works for the firm Mandiant, said that the U.S. isn’t just tracking the activities of nations like Russia and China, but also Syria and Stuxnet’s target of choice: Iran. Galante said cyberweapons give smaller, poorer nations a way to leverage asymmetric force against much larger foes.
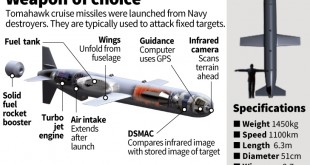
US has also been involved in carrying out cyber warfare. Stuxnet, for example, was a joint venture between Israel and the USA to destroy Iran’s nuclear program capability. In February 2016, Secretary of Defense Ashton Carter confirmed that the United States was using cyber as a weapon of war. In referencing US military actions against the Islamic State in Syria and Iraq (ISIS), Secretary Carter said, “Just like we drop bombs, we’re dropping cyber bombs. United States directed the military’s Cyber Command for the first time to mount computer-network attacks that are now being used alongside more traditional weapons. Open-source information suggests, however, that the United States may have cyber weapons with the ability to cause destructive effects in the physical domain, for example, malware similar to the Stuxnet malicious code capable of ‘blowing up nuclear centrifuges’ in Iran, or computer viruses designed to ‘sabotage missile launches’ in North Korea.
Even the British army has been reported as examining ways of using malware as a military tool. General Sir Patrick Sanders, outlined recently how the UK targeted devices like smartphones and laptops used by ISIS to communicate with their allies.
Many countries starting with US and which now includes U.K., China, Russia, Israel and others are setting up Unified cyber commands for more effective and coordinated efforts for conducting cyberspace operations, both offensive and defensive. The offensive operations are seen as deterrent to adversaries.
CyberWeapons
A cyberweapon is a malware agent employed by a state or non-state actors against specific targets for military, paramilitary, or intelligence objectives. The “Tallinin Manual on International Law Applicable to Cyber Warfare” defines a cyber weapon as a “cyber means of warfare” that is capable, by design or intent, of causing injury to persons or objects.
Military Cyber Weapons are software and IT systems that, through Information and Communication Technology (ICT) networks, manipulate, deny, disrupt, degrade, or destroy targeted information systems or networks. Commonly, cyber technology will have dual functions: attack/defense, peaceful/aggressive, legal/illegal.
Cyberweapons are perfect weapons – they are invisible and, unlike the nuclear arms race, countries can keep them under wraps as there is no visible sign of research and development, according to Mikko Hypponen, chief research officer at security firm F-Secure. “Governments are very interested in them because they are effective, deniable, and relatively cheap,” he told delegates at the Infosecurity Europe 2016 conference in London. There is a lot of “fog” surrounding cyber weapons and cyberwar, said Hypponen, because there is no way of knowing the true capability of any country. “The leaders are undoubtedly the US, followed by Israel, Russia and China, but after that the fog just gets thicker – there really is no way of knowing the cyber offensive capability of countries like Brazil, Vietnam and Australia,” he said.
Stuxnet was the first cyberweapon, discovered in 2010 and the subsequent information leaks confirmed that the trojan was indeed a state sponsored malware designed to damage the targeted industrial control systems for a specific type of centrifuge equipment in a special nuclear facility in Iran. An employee situated inside an Iranian nuclear power site inserted a USB stick embedded with the Stuxnet worm, either knowingly or unknowingly, into an air-gapped system. Exploiting multiple zero-day exploits, this malware searched for specific software running centrifuges, and commanded them to spin dangerously fast and then slow for a period of months without being detected. These centrifuges eventually broke and more than 1,000 machines were rendered useless
A recent cyberattack that resulted in physical damage occurred in 2014, when the German Federal Office for Information Security (BSI) reported that a steel mill suffered severe damage and forced a shut down due to a cyberattack that caused heavy equipment to go out of control. Analysts have concluded that the attack was effective primarily because the hackers had an intimate knowledge of the workings of the steel mill plant, according to BBC News.
The US military has reportedly drafted a classified list of cyber weapons that includes computer viruses and software that can be used to penetrate enemy networks. Defining these tools as weapons, as opposed to systems or processes, allows the military to apply the same authorisation controls as they apply to conventional weapons such as guns and tanks. The true cyberweapon can damage an electromechanical or process control system such that a serious industrial accident results in loss of life or property beyond the system, or major economic damages.
The insider threat is a very real weapon in the cyber warfare armory, with a mole able to introduce a threat directly to the network or exfiltrate highly sensitive or secret material. “We now have a weapon that can strike at the speed of light, it can be launched from anywhere in the world, and it can target anywhere in the world,” says Kevin G. Coleman is a Senior Fellow and Strategic Management Consultant with the Technolytics Institute. Unlike personnel and equipment, computer code may be instantly redeployed to any area, and because code is reusable, it offers a practically bottomless magazine for future attacks.
Cyberweapon as the class of WMD
The growing danger of destructive cyber weapons in the future joint operating environment and the devastating effects they may have in the physical domain has prompted experts to catergorize the cyberweapons as WMD.
In his book, Countering WMD, Air War College Professor and WMD expert Al Mauroni specifies three basic conditions that a for weapon systems should meet to be defined as a WMD. Benjamin B. Hatch of United States Air Force argues that modern cyber weapons satisfy those conditions.
The system’s fundamental design is the initial consideration for the system to act as a weapon. To meet this threshold, there are two examples to consider. First, the 2009 Stuxnet worm that damaged the centrifuges involved in Iran’s nuclear program is assessed as the “world’s first digital weapon” and the code was fundamentally designed to cause physical destruction on equipment controlled by computers. Second, Secretary of Defense Carter’s confirmation the United States uses cyber in the form of “cyber bombs” and as a weapon of war further supports an argument cyber code designed to cause destruction in the physical domain has met this initial condition.
The second condition Mauroni set is a determination that the weapon has the “capability to cause mass causalities (defined as more than one thousand injuries or deaths) at a single point in time and space.” The DOD Law of Armed Conflict outlines three examples where cyber weapons could be employed to achieve mass casualties. Specifically, cyber operations that: trigger a nuclear plant meltdown; open a dam above a populated area, causing destruction; or disable air traffic control services, resulting in airplane crashes. These examples demonstrate meeting the second condition.
Mauroni’s final condition is that the WMD should be “defined by internationally accepted conventions as a ‘special’ category of weapons systems.” While there is not currently an international convention, there have been attempts to explore such a possibility. The international community has discussed the broader topic, establishing the current international position that international law and in particular, the U.N. Charter is applicable to acts in and through cyberspace, as published in the 2013 U.N. Group of Governmental Experts (UNGGE) consensus report on cyberspace.
Military demanding and developing Extreme Cyberweapons
The U.S. military has spent five years developing advanced cyberweapon and digital capabilities and is likely to deploy them more publicly soon, said the head of the Pentagon’s U.S. Cyber Command.Adm. Mike Rogers, who is also director of the National Security Agency, said U.S. policy makers have largely agreed on rules of engagement for when cyberweapons can be used for defense.
A new unit headed by Lt. Gen. Edward Cardon was tasked with developing digital weapons — fashioned from malware and other cyber-tools — that can intensify efforts to damage and destroy the Islamic State’s networks, computers and cellphones. This was also a test of operational effectiveness of its cyber command to conduct offensive mission against ISIS that was formed to thwart traditional foes like Russia, China, Iran and North Korea.
“There is still an open discussion, however, about when cyberweapons should be used for “offense,” such as carrying out attacks against a group or foreign country,” reports Damian Paletta in wall street journal “You can tell we are at the tipping point now,” Adm. Rogers said. “The capacity and the capability are starting to come online [and] really starting to pay off in some really tangible capabilities that you will start to see us apply in a broader and broader way.”
The Pentagon has put out a call for vendors bid for $460 million project contract to develop, execute and manage its new cyber weaponry and defense program. The scope of this Cyberspace Operations Support Services contract under CYBERCOM (United States Cyber Command) includes counterhacking, as well as developing and deploying lethal cyberattacks — sanctioned hacking expected to cause real-life destruction and loss of human life. The initial work order will support “cyber joint munitions effectiveness” by developing and deploying “cyber weapons” and coordinating with “tool developers” in the spy community, the documents state.
The U.S. Navy has opened a new “Cyber Foundry” – a development center specifically for offensive (not defensive) cyber capabilities in June 2020. “The Navy’s Cyber Foundry is the Navy’s cyber weapon building shipyard,” said Capt. Ann E. Casey, commanding officer of U.S. Navy Cyber Warfare Development Group (NCWDG). “With [88] developer billets, lab space, and development operations networks at the unclassified and classified levels, the Foundry was built to deliver cyber weapons as directed by . . . Fleet Cyber Command.”
The mission of the Foundry is to provide the Navy with reverse engineering, vulnerability discovery and software development to target adversaries’ cyber and cyber-physical systems. It includes a “hardware exploitation lab” for exploit and tool creation. The Foundry sits under the Navy Cyber Warfare Development Group, which has been conducting the Navy’s cyber, cryptologic and electronic warfare R&D for more than 30 years.
Accroding to reports, the US and UK are collaborating to develop so-called “cyber weapons” to defend their interests in cyber space. Cyber weapons, said the UK’s armed forces minister, are now regarded as “an integral part of the country’s armoury”.
China Fires ‘Great Cannon’ Cyber-Weapon At The Hong Kong Pro-Democracy Movement
In 2019 China employed a state-operated, distributed denial of service (DDoS) cyber-weapon, aiming online forum used by pro-democracy movement protesters in Hong Kong to help coordinate their anti-government demonstrations. According to a report from Chris Doman, a security researcher at AT&T Alien Labs, the Great Cannon of China started the current attack on November 25 2019. This follows an initial attack on August 31 when the LIHKG forum, the Hong Kong equivalent to Reddit. The forum was targeted as it has been used by members of the Hong Kong pro-democracy protest movement to coordinate demonstrations.
While not as well-known as the Low Orbit Ion Cannon (LOIC), a DDoS tool put to very effective use by the Anonymous hacking group when attacking websites supporting the Church of Scientology and later those opposed to WikiLeaks, the Great Cannon has the potential to be a much more significant threat. It works by hijacking web traffic from users within the boundaries of the government-controlled Great Firewall of China and redirecting that traffic to websites external to it. This is achieved by “injecting” malicious JavaScript code into the insecure HTTP connections of sites visited by Chinese users. This interception allows the operators of the cyber-weapon to target a chosen web resource with a DDoS attack.
A Distributed Denial of Service attack is when a threat actor sends more access requests, of various technical flavors, to a web server than it can handle. The more of these superficially “genuine” requests that are sent simultaneously, the harder it is for the website to function normally. The bigger the attack, the slower the targeted site becomes in dealing with ordinary users trying to connect, ultimately resulting in the site going offline. Some of the biggest and best-known websites have been taken offline by such attacks. Perhaps most notoriously of late when Wikipedia, the seventh most popular site on the planet, was the victim of a massive DDoS attack.
An official statement from LIHKG regarding the DDos attack on August 31, stated that the total number of server requests that day exceeded 1.5 billion. “The enormous amount of network requests have caused internet congestion and overload on the server which has occasionally affected the access to LIHKG. The website data and members’ information are unaffected,” the statement confirmed.
Threat of stolen ‘cyber weapons’
The dangers of state investment in the collecting of software flaws and the creation of powerful tools which then exploit these previously unknown weaknesses was painfully demonstrated through the leaking of the vulnerability stockpiled by the NSA, EternalBlue. This was the backbone of the WannaCry attack which made international headlines in 2018 through its impact on the British NHS and other international business and government services.
Other tools allowed NSA analysts to break into a range of systems, network equipment, and firewalls, and most recently, Linux servers, as well as a range of Windows operating systems. Companies scrambled to fix the vulnerabilities in the aftermath the WannaCry attack.
“The Shadow Brokers” claimed to have stolen “cyber weapons” from an elite hacking group linked to the NSA. The malicious hacking tools were claimed to come from the highly sophisticated Equation hacking gang, which has previously been rumoured to have links to the NSA. The Equation Group is known to use some of the most advanced malware and probably helped develop the infamous Stuxnet computer worm, according to security firm Kaspersky Lab.
In a highly unusual move, the Shadow Brokers announced that they would be running an auction, offering the stolen hacking code – which they claimed to be “better than Stuxnet”. “We auction best files to highest bidder. Auction files better than Stuxnet,” the hackers said in a Tumblr posting.
It’s a pretty bold claim, but the hackers have offered sample files, and some security researchers say they appear to contain legitimate exploits. Samples of the stolen files are dated most recently to 2013, and they do contain coding related to hacking, said Nicholas Weaver, a security researcher at the International Computer Science Institute in California. “It appears to be a large amount of NSA infrastructure for controlling routers and firewalls, including implants, exploits, and other tools,” he said in an email. The exploits specifically target firewall technology from Cisco, Juniper, Fortinet, and Chinese provider Topsec, said Matt Suiche, CEO of cyber security startup Comae Technologies, in a blog post.
Cyber Weapons Market
The global cyber weapons market is anticipated to witness significant growth over the forecast period owing to rise in threats to critical infrastructures across vital sectors including corporate IT and government. Rise in defense expenses coupled with the continuous evolution of cyber weapons as a warfare tool is also expected to drive market growth. Military, paramilitary, and intelligence agencies penetrate through enemy’s network with the usage of cyber weapon, essentially a malware or virus. Growing demand for violating the privacy of the target and securing the sovereignty of the host nation is expected to drive the global market substantially over the forecast period. Offensive usage of cyber weapons by cybercriminals and defensive usage by law enforcement officials further contributes to market demand.
Major challenges to the global cyber weapons market include preventing weapons development and usage as it leads to mass destruction and creates disharmony worldwide if used offensively. Further, cyber weapons usage increases cyber warfare and anonymity between hackers, which may negatively impact market growth.
Surging demand for offensive and defensive cyber weapons by NATO nations, especially the U.S to defend their interest in cyberspace may considerably drive the cyber weapon market. Additionally, non-NATO nations are anticipated to invest in internet warfare capabilities, which will further drive the cyberweapons demand. Furthermore, North America is estimated to account for a significant share in the global cyber weapon market closely followed by Asia Pacific owing to its increased usage in aerospace, defense, and intelligence units.
The global military cyber weapon market is dominated by companies based in the United States, Israel and the EU.
The application terrain of the Military Cyber Weapons market can be classified into Communication Network, Power Grid, Air Traffic Control, Transportation Systems, Financial Systems and Hospitals.
Leading Companies in the Military Cyber Weapons Market are AeroVironment, Airbus Defence and Space, AVAST, BAE Systems, Boeing Co
Clear Water Compliance, CynergisTek, Elbit Systems, Exodus Intelligence, Fire Eye, Israel Aerospace Industries, Leonardo, Lockheed Martin, MetricStream, Netragard, Nettitude, Northrop Grumman Corp, Saab, Telus Security Labs, VSR, and Zerodium
References and Resources also incude:
https://www.maritime-executive.com/article/u-s-navy-opens-center-for-cyber-weapon-development
https://www.itpro.com/security/28170/what-is-cyber-warfare
 International Defense Security & Technology Your trusted Source for News, Research and Analysis
International Defense Security & Technology Your trusted Source for News, Research and Analysis