Although nuclear weapons have not been used in conflict for decades, the risk of their use persists. Around the world, countries are still building and modernizing nuclear arsenals. Russia, US and China are rapidly upgrading and modernizing their strategic triad. The potential use of nuclear weapons poses the greatest danger to U.S. security. According to the U.S. National Security Strategy, Recently Nuclear threat is rising again due to nuclear arms race in Asia, modernization of nuclear arsenal by Major and regional powers, statement by countries like North Korea to use nuclear weapons, ongoing missile and nuclear proliferation risks in the Middle East and acquiring of Nuclear weapons by terrorists.
Nuclear command and control (NC2) is the activities, processes, and procedures performed by appropriate military commanders and support personnel that, through the chain of command, allow for senior-level decisions on nuclear weapons employment. The U.S. President has sole authority to authorize the use of U.S. nuclear weapons. This authority is inherent in his constitutional role as Commander in Chief. According to the Nuclear Matters Handbook, published by the Office of the Deputy Assistant Secretary of Defense for
Nuclear Matters, the elements of the nuclear command and control system (NCCS) “support the President, through his military commanders, in exercising presidential authority over U.S. nuclear weapons operations.”
The system relies on “a collection of activities, processes, and procedures performed by appropriate military commanders and support
personnel that, through the chain of command, allow for senior-level decisions on nuclear weapons employment.” Specifically, the NCCS provides the President “with the means to authorize the use of nuclear weapons in a crisis and to prevent unauthorized or accidental use. According to the Congressional Research Service, the Nuclear Command and Control System “collects information on threats to the United Sates, communicates that information through the chain of command to the President, advises the President on options for a response, communicates the President’s chosen response to the forces in the field, and controls the targeting and application of those forces.”
According to open sources, operators at the North American Aerospace Defense Command have less than three minutes to assess and confirm initial indications from early-warning systems of an incoming attack. This compressed decision-making timeframe could put political leaders under intense pressure to make a decision to escalate during a crisis, with incomplete (and possibly false) information about a situation. Therefore, even if nuclear early-warning systems might eventually detect the subversion, heightened levels of uncertainty and tension caused by an alert may impel the respective militaries to put their nuclear weapons on high alert status.
As General Michael Hayden, the former director of the CIA noted, the system “is designed for speed and decisiveness. It’s not designed to debate the decision.” Long-range missiles attacking the United States from Russian territory could reach U.S. territory in around 30 minutes; sea-based systems deployed closer to U.S shores might arrive in half that time. If the United States wanted to retaliate before U.S. weapons, or, more importantly, the U.S. command and control system, were degraded by an attack, then the entire process of identifying, assessing, communicating, deciding, and launching would have to take place in less than that amount of time. Given that some time would be needed for mechanical or administrative steps, analysts estimate that the President would have less than 10 minutes to absorb the information, review his options, and make his decision.

Emerging Technologies
Technology has transformed armed conflict throughout history. Today, emerging technologies in the fields of offensive cyber capabilities, artificial intelligence and autonomous technologies will have a significant impact on military behaviour. Rapid advances in cyberspace and emerging technologies such as artificial intelligence (AI) and hypersonic weapons compound the risks of close calls, mishaps and misunderstandings in the nuclear domain. New emerging technologies are also causing enhanced risks to nuclear including AI-augmented offensive cyber attacks, increasing vulnerability of nuclear command, control, and communication (NC3) systems to cyber attacks.
Any use of nuclear weapons, either by intent, accident or miscalculation, will cause catastrophic humanitarian consequences, so it is critical that policymakers and the public understand the pre-existing dangers of nuclear weapons as well as added risks posed by emerging technologies. Adopting measures that only seek to reduce or mitigate the additional risk that emerging technologies pose to nuclear weapon use is not an adequate response to the nuclear status quo. Eliminating nuclear weapons is the only way to eliminate these risks altogether.
As satellite and other intelligence detection systems become more advanced, it will become more difficult to keep historically concealed nuclear weapons, such as nuclear weapons on submarines, hidden. This could then cause nuclear-armed countries to use all their nuclear weapons earlier in a conflict, given that an adversary would seek to immobilize all known nuclear systems as soon as possible.
Cyber Threat
One of the threats posed by offensive digital technology is the increased uncertainty that it can introduce into the decision to launch a nuclear weapon. There are a few different cyber operations with the potential to impact nuclear weapon decision-making, including: data manipulation, cyber jamming communications channels or; cyber spoofing. Data manipulation refers to tampering with data in any given system. Cyber jamming refers to disrupting authorized wireless communication. Cyber spoofing describes a device impersonating another to be better positioned to launch attacks. Nuclear command and control refers to the process to order and carry out the launch of a nuclear weapon.
In a 2018 study on cyber security and nuclear weapons, researchers at Chatham House made the assessment that: “The risks of a cyber attack on nuclear weapons systems raise significant doubts about the reliability and integrity of such systems in a time of crisis, regarding the ability to: a) launch a weapon b) prevent an inadvertent attack c) maintain command and control of all military systems d) transmit information and other communications e) maintenance and reliability of such systems.
”Manipulated information in the command and control system could lead decision-makers to launch nuclear weapons. What’s more, decision-makers’ knowledge that information could be manipulated could make them more ready to use nuclear weapons in a time of crisis. The fear of an offensive cyber operation preventing the launch of nuclear weapons may result in nuclear-armed states changing their operational protocols to more easily launch nuclear weapons quickly or without the current checks or authorizations. Such changes compound the risk of unintended launch or detonation as a result of false warnings or a miscalculation. A number of possible scenarios involving cyber operations could lead to escalation and the launch of a nuclear weapon, based on network and system vulnerabilities and deliberate attempts to compromise nuclear-weapon decision making.
One such scenario which was raised during an ICAN-hosted expert workshop on emerging technologies and nuclear weapons, could be that malware is discovered on a computer system that controls nuclear weapons in a time of crisis and leads to considerable escalation. Offensive cyber operations could lead to the use of nuclear weapons, even when the cyber attack is not intended to impact nuclear weapons or related infrastructure. Given the entanglement of some conventional and nuclear systems, an intended attack on a conventional system could be interpreted by the victim as an attack on a nuclear system, leading to unintended escalation. An cyber attack on conventional systems, already a dangerous and destabilizing move, could thus have even more drastic consequences.
The threat to the predictability of nuclear-armed actors posed by possible cyber attacks further undermines the credibility of nuclear deterrence. Although the theory of nuclear deterrence has already been discredited for a number of other factors, these new developments are causing even some deterrence proponents to question its ongoing relevance and validity.
Artificial Intelligence (AI)
The increased application of advanced machine learning in defense systems can speed up warfare – giving decision-makers even less time to consider whether or not to launch nuclear weapons; Countries may be eager to apply new artificial intelligence technologies before they understand the full implications of these technologies.
Applied machine learning and autonomous systems would result in an increased speed of warfare and therefore an even shorter period in which decision-makers will have to choose whether to launch nuclear weapons or not. Autonomous systems can also lower the threshold to engage in armed conflict, including nuclear conflict. There is still a debate about whether to remove human evaluation of data from the decision to launch a nuclear weapon, with several government officials stating that they would never remove human input. However, given recent editorials and debate on the subject, the terrifying possibility of machines being programmed to make this existential decision still exists.
The process in which advanced machines “choose” a course of action is becoming increasingly opaque as machine learning advances, to the point that these processes are called “black boxes.” Therefore, it is difficult for humans to check how and why a machine recommended a course of action to understand if the machine has been compromised, is malfunctioning or its programming resulted in an unlawful or
unintentional outcome.
The history of nuclear weapons is riddled with near misses where nuclear war was only averted by a human choosing to disregard false positives presented by machines. One example that demonstrates the importance of having humans in the loop to correct machines, is clear in the story of Stanislav Petrov, who famously ignored the warning presented by nuclear detection technology of incoming U.S.
nuclear missiles due to his skepticism of the machine, and in so doing prevented a massive humanitarian catastrophe. Policy makers and the military may also be overly eager to introduce immature technology, such as new advanced machine learning, without fully understanding its implications. In the case of nuclear weapons, this could have deadly consequences
AI will make existing cyber warfare capabilities more powerful. Rapid advances in AI and increasing degrees of military autonomy could amplify the speed, power, and scale of future attacks in cyberspace. AI systems used in conjunction with existing cyber offense tools might become powerful force multipliers, thus enabling sophisticated cyber attacks to be executed on a larger scale (both geographically and across networks), at faster speeds, simultaneously across multiple military domains, and with greater anonymity than before.
An attacker could also apply AI machine learning techniques to target autonomous, dual-use early warning and other operating systems (e.g., NC3; intelligence, surveillance, and reconnaissance; early warning; and robotic control networks) with “weaponized software” such as hacking, subverting, spoofing, or tricking.
Second, cyber attacks that target AI systems can offer attackers access to machine learning algorithms, and potentially vast amounts of data from facial recognition and intelligence collection and analysis systems. These things could be used, for example, to cue precision munitions strikes and support intelligence, surveillance, and reconnaissance missions by high resolution remote sensing satellites. An attacker could also apply AI machine learning techniques to target autonomous, dual-use early warning and other operating systems (e.g., NC3; intelligence, surveillance, and reconnaissance; early warning; and robotic control networks) with “weaponized software” such as hacking, subverting, spoofing, or tricking.
The machine speed of AI-augmented cyber tools could enable even a low-skilled attacker to penetrate an adversary’s cyber defenses. It could also use advanced persistent threat tools to find new vulnerabilities. For example, air-gapped, nuclear-powered submarines considered secure when submerged could become increasingly vulnerable to a new generation of low-cost — and possibly black-market — highly automated advanced persistent threat cyber attacks when docked for maintenance.
New threats arise due to fully autonomous vehicles and risk of their hacking, precision-guided conventional weapons, anti-satellite weapons or hypersonic weapons to concealed and hardened nuclear assets. Taken together, this trend might further erode the survivability of states’ nuclear forces.
The current NC3 system is also reliant on the US civil infrastructure that provides electricity, water, and other logistical requirements to terrestrial bases that host NC3 receiving stations and command posts. This makes that element of NC3 subject to any break in service on the civilian side. The system is not completely autonomous.
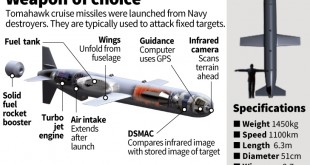
Hypersonic Weapons
Of the new technologies, hypersonic weapons are particularly problematic for the nuclear realm. These new weapons, which can deliver conventional or nuclear payloads, differ from intercontinental ballistic missiles (ICBMs). Their speed and manoeuvrability enable them to have unpredictable flight paths, which can evade traditional missile defence systems. A target thousands of miles away can be hit in a matter of minutes, severely shortening the time for the target country to decide its response. This new class of weapons received significant attention in 2019 when Russian President Vladimir Putin announced that Russia had deployed its own hypersonic glide vehicle known as the Avangard. Russia, China and the United States are rushing to develop their own hypersonic capabilities in what many are calling a new “arms race”.
Experts see the main risk associated with hypersonic weapons to be their severe shortening of the time within which a targeted party will receive, interpret and respond to a warning. While this finding is not revolutionary, it underscores how experts in the nuclear field view the impact of this type of weapon. The hypersonic missile’s ability to carry both nuclear and conventional warheads adds to its disruptive potential, as misunderstandings are easy to imagine. A missile with a conventional warhead could easily be assumed to be one with a nuclear warhead. This ambiguity, together with the hypersonic weapon’s high speed, could provide strong incentives for countries to develop dangerous nuclear postures or even to attack preemptively for fear that it will be struck with a nuclear warhead.
Quantum (Q) technology
Emerging Quantum computers will be able to break the traditional encryption, may disrupt massively the system of authenticating codes of strategic communications that states use to control nuclear weapons and to communicate nuclear fire orders over a variety of physical media—cables, radio transmission, etc. All eight nuclear armed states, face this apparently relatively near-term threat to the security of their nuclear weapons-related communication systems and code-based control technologies such as permissive action links.
Countries which have developed QKD based communications may be able to reconstruct their NC3 using long distance entanglement effects combined with quantum encryption; but less capable nuclear-armed states will need to develop other means such as quantum proof encryption to sustain the security of their nuclear communications and other decision-support systems against external intrusion, decoding, and demolition or disruption.
Quantum sensors will be able to detect stealth planes and nuclear submarines increasing the transparency of nuclear weapons and nuclear weapons delivery systems. This will enable states to identify and track otherwise invisible delivery platforms such as submerged submarines and nuclear armed drones, or of subterranean command centers and missile launch sites used by China and North Korea. With these sites rendered transparent, NC3 systems may be forced to adjust not just to the direct threat of external access to these systems, but to further reduction of the already compressed decision space from minutes to seconds, with the implication that artificial intelligence systems may substitute for humans whose brains are too slow and limited to process sensed information communicated to the nuclear command and control sensors.
Such Q-sensors may also enable nuclear armed states to map with much greater precision the magnetic anomalies of Earth and thereby adjust slightly the intended trajectory of long-range missiles fired over full range (mostly North-South over the pole) rather than in short-range test mode (mostly East-West), thereby increasing the probability of destroying targets. Such a development could increase first strike capability on the one hand and destabilize deterrence on the one hand; or increase the credibility of threats of nuclear attack, thereby reducing the propensity of nuclear adversaries to risk a first strike. The net effects are unknown at this stage and are purely speculative—but may emerge over the time frames in which nuclear modernization of major nuclear weapons delivery platforms will take place.
Short term mitigation
Therefore there is urgent need for countries to modernize their Nuclear Command and Control Strategies, procedures and processes to make them hack proof as well as improve their quality. The 2017 National Security Strategy of the United States highlighted the need to “maintain the credible deterrence and assurance capabilities provided by its nuclear triad and US theater nuclear capabilities deployed abroad.” This means that significant investment would be needed to maintain the nuclear arsenal and its supporting infrastructure and to modernize the nuclear enterprise. This also means that “modernization and sustainment require investing in the aging command and control system.”
We already face the challenge the social media storms may trigger the early warning systems of nuclear armed states. One antidote is to create an independent, impartial early warning fusion center that relies on distributed sensors and indexes of the status of nuclear forces. Q-communications might provide a new way to assure nuclear-armed states that the advice provided by an independent early warning center has not been spoofed by an adversary or malevolent actor, solving the zero knowledge problem addressed in other nuclear arms control and monitoring contexts. Thus, Q-tech might increase the stability of nuclear conflicts, at least in the short term.
Conclusion
In the nuclear weapons realm, these technologies add another layer of risk to an already unacceptable level of risk of nuclear weapons use. Mitigation measures that only seek to reduce the additional risk that emerging technologies pose to nuclear weapon use is not an
adequate response to the nuclear status quo. Eliminating nuclear weapons is the only way to eliminate these risks altogether.
Only the stigmatisation, prohibition and elimination of nuclear weapons can fully address both new and old nuclear weapons risks and guarantee that nuclear weapons are never used again, says ICAN.
References and Resources also include:
https://nautilus.org/napsnet/nuclear-command-and-control-in-the-quantum-era/
 International Defense Security & Technology Your trusted Source for News, Research and Analysis
International Defense Security & Technology Your trusted Source for News, Research and Analysis