There are two approaches to connect Warfighting and emerging technologies. One is to consider the present and future threat environment and then through system analysis we can identify technologies required to mitigate those threats. Secondly, we can identify the emerging technologies that can offer new military capability.
Coming to first approach, What is the full spectrum of threat environment against which we should prepare? We can classify the full threat environment into three types. The first class is what we can National security threats affecting all the population or country.
These threats are occurring at world, regional or national level due to climate change, urbanization, energy, water and material scarcity, which can lead to future conflicts. These threats require national response, national strategy and implementation plan. But these also affect military and therefore we need to assess their military impact and then technology requirements.
The second class is actual warfighting domains; five have become well established Air, Land, Sea, Space and Cyber. Fighting these types of threats require military strategies, tactics, commands, personnel, weapons, equipment, and adequate supplies to accomplish their missions. Apart from these domains there are also additional domains that have become important. Information warfare is “Actions taken to achieve information superiority by affecting and exploiting adversary information, information-based processes, information systems, and computer based networks while defending one’s own information, information-based processes, information systems and computer-based network and exploiting our own military information functions.
National Security Threats
These threats are occurring at world, regional or national level due to climate change, urbanization, energy, water and material scarcity, which can lead to future conflicts. These threats require national response, national strategy and implementation plan. But these also affect military and therefore we need to assess their military impact and then technology requirements.
First we shall consider few National security threats and identify some of the technological requirements. First we all know India is one of the worst hit nations by climate change. Climate change is killing people by heat waves, endangering rivers, causing Rapid melting of Himalayan glaciers that are predicted to bring in flash floods and a series of mini disasters downstream. Climate Change poses risk to military readiness, Operations and Strategy Increasing number of avalanches is killing our soldiers stationed in High altitude areas. Extreme weather like drought, flooding and extreme temperatures pose risks to military bases which could affect their deployment, and training. Supply Chains could be affected. Naval Installations are vulnerable to rising sea level which might be redesigned or re-located leading to enormous infrastructural costs. Military will be deployed more and more for disaster relief tasks.
Battlefield threats
The Last category is advanced battlefield threats which have now been expanded to fifth generation stealth fighters, directed energy weapons both laser and electromagnetic types, CBRNE threats including tactical nuclear weapons, hypersonic weapons and platforms, UCAVs, Rail guns, large number of autonomous air, ground and underwater systems, Super Cavitating Submarines and Torpedoes and Missile torpedoes. Finally of these battlefield threats have also being integrated into comprehensive C4ISR framework and Network Centric Operations which further enhances their lethality. To neutralize these advanced threats, we need system of system solution like neutralizing stealth aircrafts you need system of system counter stealth solution. For Aircrafts, UAVs, Ballistic and Cruise Missiles require integrated air and missile defense.
Some of the emerging threats are also multidomain threats like torpedo missiles and submarines which shall launch UAV. There is also trend to combine different domains US Army’s Integrated Cyber and Electronic Warfare, or ICE that looks to leverage both cyber and Electronic Warfare capabilities as an integrated system.
Warfighting Domains
The second class is actual warfighting domains; five have become well established Air, Land, Sea, Space and Cyber. Fighting these types of threats require military strategies, tactics, commands, personnel, weapons, equipment, and adequate supplies to accomplish their missions.
Apart from these domains there are also additional domains that have become important. Information warfare is “Actions taken to achieve information superiority by affecting and exploiting adversary information, information-based processes, information systems, and computer based networks while defending one’s own information, information-based processes, information systems and computer-based network and exploiting our own military information functions. US also considers Electromagnetic domain that is electromagnetic spectrum portion of the information environment. Electromagnetic spectrum is expanding to cover the complete range of frequencies of electromagnetic radiation.
Military operations require assured access to electromagnetic spectrum for their communications, radar sensing, command and control, time transfer, and geo-location. Electromagnetic weapons have now become common in all three domains Air, Land and Water. The US Electromagnetic Spectrum Strategy 2013, calls for ensuring the access to the congested and contested electromagnetic environment of the future, by adopting new agile and opportunistic spectrum operations, and through systems which are more efficient, flexible and adaptable and adopting new technologies capable of more efficient use of the spectrum and reduced risk of interference.
Another emerging domain is the neuro cognitive domain that includes mind warfare and control. We can also consider few other domains relevant to our environment that is Mountain warfare, Jungle Warfare or even tunnel warfare. Each of these domains has unique capability requirements and technological solutions.
Our adversary is rapidly developing military capability to dominate in all these domains. It has developed high-performance fifth-generation stealth fighters, and large number of missiles including “Carrier killer” missile, anti-ship cruise and ballistic missiles, nuclear submarine and long-range intercontinental missile. Its homegrown aircraft carrier is nearing completion. It has also developed Anti Satellite capability that can target from Low Earth Orbit to medium Earth orbits, carrying ever increasing cyber-attacks and cyber warfare campaigns. and carried out psychological warfare campaign during Doklam standoff.
Climate Change and Military Readiness & Operations
First we shall consider few National security threats and identify some of the technological requirements. First we all know India is one of the worst hit nations by climate change. Climate change is killing people by heat waves, endangering rivers, causing Rapid melting of Himalayan glaciers that are predicted to bring in flash floods and a series of mini disasters downstream.
Climate Change poses risk to military readiness, Operations and Strategy Increasing number of avalanches is killing our soldiers stationed in High altitude areas. Extreme weather like drought, flooding and extreme temperatures pose risks to military bases which could affect their deployment, and training. Supply Chains could be affected.
Naval Installations are vulnerable to rising sea level which might be redesigned or re-located leading to enormous infrastructural costs. Military will be deployed more and more for disaster relief tasks. Technology can play very important role in early warning, rapidly respond and deliver relief care to the affected population after disaster such as earthquakes, search for survivors, provide backup to damaged critical infrastructure including communications e.t.c.
- Improved capabilities for predicting high impact weather events including heavy rain, thunderstorm, cyclone, fog, heat and cold wave etc.
- Military bases should be designed to withstand future extreme weather. Future military equipment would be required to be designed to work under extreme weather conditions would further increase their costs. For example Ships would require greater sea-keeping ability for higher sea states and prolonged extreme weather operations
- Real-time information on the most damaged areas of a city or locations of where people remain stranded saves lives data allows emergency management to develop more targeted response plans. The use of social media, drones, satellite imagery through GIS, real-time disaster modeling. Wearable devices for providing early warning, supporting search and rescue, and reconnecting families. Google’s Person Finder has been used to help reconnect families after floods in Pakistan, the 2013 Japan earthquake, and more.
- Smart home sensor networks for sensing and reporting, augmented reality systems software adds a layer of computer-generated data, into reality through smart glasses and other Internet-connected devices.
- Beyond information and communications technology (ICT), other technologies such as robotics, manufacturing, medical and transport technologies are also important.
- Unmanned aerial vehicles for temporarily restoring communications networks and delivering critical relief items, such as medicines. There is need to have better dual use equipments like boats, bridges, hospital ships, earth moving equipment, and medical facilities. Robots can provide diagnostic support, treatment and monitoring of medical patients.
- 3D printers to produce medical supplies, disaster-resistant structures and building materials and making spare parts to maintain the other emerging technologies.
These technologies can be classified as Adaptation – making our soldiers and military systems to be more resilient to the effects to actual or expected future climate so that our vulnerability is lowered.
Another set of technologies are those of Mitigation – reducing climate change – involves reducing the flow of heat-trapping greenhouse gases into the atmosphere, either by reducing sources of these gases (for example, the burning of fossil fuels for electricity, heat or transport) or enhancing the “sinks” that accumulate and store these gases (such as the oceans, forests and soil).
How US also considers the third option, climate intervention, also known as geo engineering. For example Carbon dioxide removal and albedo-modification techniques however they may cause environmental risks, socio-economic impacts, and cost. Examples are injection of aerosols into the stratosphere and marine cloud brightening. The ‘marine cloud brightening’ technique modifies the low clouds to make them more reflective thereby cooling the climate.
Building Energy Security in Future Military
Coming to second option, the mitigation the threat of climate change requires switching to renewable energy. Indian government has set ambitious renewable energy target of installing 175 gigawatts of renewable energy capacity by 2022. Again to note China has become world leader in renewable energy investment and technology. China has vaulted to the top of the world in solar power capacity in 2016, passing Germany the country added more than 34 gigawatts of solar capacity last year and more than 23 gigawatts of wind power in 2016.
Military itself is a great polluter. Aircraft exhaust has unique polluting effects that result in greater warming effect by per unit of fuel used. The military also consumes huge amount of electricity, which accounts for even more greenhouse gas emissions. Therefore, climate mitigation also requires that military should also move to clean sources of energy. Switch to renewable energy would Improve energy performance that will also reduce the risk and effects of attacks on supply lines and enable tactical and operational superiority. According to US department study, one in nearly 40 fuel convoys in Iraq in 2007 resulted in a death or serious injury, and one in 24 fuel convoys suffered casualties In Afghanistan.
Another reason is the vulnerability of Electrical grid to natural disasters like tornados, hurricanes and winter storms and recently Cyber warfare. Solar photo voltaic (PV)-powered Distributed microgrid tech can secure the electrical grids at military bases to reduce the impact of physical attacks and cyber-attacks. (In 2012, the US Department of Defense reported about 200 cyber incidents across critical infrastructure systems and nearly half targeted the electrical grid. DoD realizes that an over-reliance on fossil fuels could undermine its resilience during a power grid failure or reduce its fighting capability if energy supplies are compromised at the time of war.) By actively promoting low-and no-carbon energy alternatives shall also boost the military energy readiness.
Indian Military has also taken few steps in this direction particularly Indian Navy has been embarking on an ambitious path of wholeheartedly embracing `Green Initiatives’ since 2014. The Navy has planned to install 19 MW solar PV installations by 2018. The Solar power panels were installed on board survey ship INS Sarvekshak, based in Kochi. The Army has launched a renewable energy project for developing durable power supply in high altitudes to enhance the living conditions of its personnel. The plan is to have renewable energy in place of fossil fuels that are unreliable and face transportation and maintenance hassles.
As far as US military is concerned, they depending on geographical locations military installations get electricity from solar, wind, geothermal, waste-to-energy landfill gas and biomass. Some of the technologies used by Navy are Azura is a 45-ton (41-tonne) multi-mode; point absorber wave energy converter that through its unique 360-degree rotating float mechanism, is able to extract power from both the heave (vertical) and surge (horizontal) motions of waves, to maximize energy capture. Ocean Thermal Energy Conversion technology, known as OTEC, uses the ocean’s natural thermal gradient to generate power. USAF uses solar as the dominant source of clean energy at the base.
The ultimate goal of making base energy infrastructure self-sufficient by using microgrids and relying less on public utilities.
Army has partnered with Sandia National Laboratories to provide a solar-powered microgrid and vehicle-to-grid storage. The Vehicle-to-grid approach uses vehicles as microgrid energy storage devices, when the vehicles are parked; they receive electrical power from the microgrid. If they have excess power, they return it to the microgrid.
Material Risks and Technologies
However, the sustainable growth of renewable energies depend on the availability of key materials, for example Lithium is the key limiting resource for most batteries – while rare earth metals, in particular “lanthanides” such as neodymium, are required for the magnets in wind turbine generators. Copper is the conductor of choice for wind power, being used in the generator windings, power cables, transformers and inverters.
There is also threat of Scarcity of strategic Minerals like Tungsten, Tantalum, Lithium, Nickel, Cobalt etc. Processing of high purity energy critical materials Ga, Ge, Se, In, Te, etc. Tungsten and its alloys are applied to blades used on jet engines. Cobalt is a strategic and critical metal used in many diverse industrial and military applications. The largest use of cobalt is in superalloys, which are used to make jet engine parts. Tantalum is one of the most corrosion resistant metal alloys in the market. The principal importance of GaInAs is its application as a high-speed, high sensitivity photodetector of choice for optical fiber telecommunications.
Magnesium oxide is used in high-temperature super-conducting device growth plate (super-conducting quantum devices, CT, communication), high temperature and accurate optic materials(aviation, spaceflight, laser guidance, military industry), plasma screen thin film, high-temperature crucible materials(FPD, telephone and TV screen), high-temperature insulating materials(neutron test, metallurgy industry), optic ceramics and semiconductor materials(bottom liner, sensor) and so on as well.
There is also scarcity of Rare earth materials that play an essential role in several critical weapons components and systems such as precision-guided munitions, electric ship drives, command and control centers, and aircraft, tanks, and missile systems. World is almost wholly dependent on single supplier China that produces over 95% of REE supply. China now imposing export quotas and tariffs on REE.
What are technology requirements for mitigating material risks. First we need to develop processing technologies for rare earth ores. Another is pursuit of substitutes: US Scientists have figured out a better way to extract rare earth elements from coal waste. A team of scientists at Virginia Commonwealth University has synthesized a powerful new magnetic material that could reduce the dependence of the United States and other nations on rare earth elements produced by China. The new material consists of nanoparticles containing iron, cobalt and carbon atoms with a magnetic domain size of roughly 5 nanometers. Another is Recycling, which in the long term, is a potential way to reduce mineral shortages.
Urbanization & Urban Warfare Capability
26/11 Mumbai incident saw the emergence of new form of conflict urban warfare, wherein the security forces found it challenging to locate terrorists and track their movements in multistory buildings like hotels, railway stations, markets, sports stadium and military facilities. The likelihood of urban insurgency or urban warfare is increasing due to large population growth and rapid urbanization or growth of cities. Experts predict by 2050, two thirds of humans will live in cities, while india will rise to 50%. Indian experts also point to threat of urbanization of deserts close to the border, with a growing network of canals and irrigation channels, with a good network of roads and motorable tracks. Thus, the geography of desert and semi-desert is undergoing a dramatic change which will impact upon the military operations in such areas.
Urban warfare is complex due to the presence of civilians and the complexity of the urban terrain. Tactics are complicated by a three-dimensional environment, limited fields of view because of buildings, enhanced cover and concealment, below-ground infrastructure, and the ease of placement of booby traps and snipers. The terrorists resort to Asymmetric Warfare exploiting the limitations and vulnerabilities of high-tech weapon and platforms, with relatively simple, low-cost countermeasures, tactics and solutions. Some civilians may be difficult to distinguish from combatants such as armed militias and gangs, and particularly individuals who are simply trying to protect their homes from attackers.
If these terrorists are aided by external states there is also bigger threat of Hybrid war. This type of warfare exploits regular and irregular capabilities demonstrated by Pakistan-backed Taliban, Russian-backed militias in Ukraine and Iran-backed Hezbollah. Our experts also point to possibility of initiation of hybrid war in the North-East. Military needs to define its strategy, doctrine, concept of operations, force restructuring, special equipment, and special training. It would require combatants and non-combatants as part of the force, to deal with every element of hybrid war.
Military and Security forces require new air, ground and sea based platforms having capabilities of accurately engaging targets in urban terrain with low collateral damage. The size of projectiles and weapons need to be miniaturized so that they can be employed in helicopters and small UAVs, while enhancing their lethality and engagement ranges to defeat even defeat concealed targets. New generation of smaller and smarter Air-delivered munitions are required that provides an economically viable ground-attack and low-collateral-damage capability. They should have precise position location and navigation capability as well as miniaturization of the fuses, sensors and guidance systems. One example is Textron Systems developed a new lightweight, precision-guided glide bomb Fury. The Fury is a small 27-inch, 13-pound GPS and laser-guided bomb engineered to fly and fire from medium and large drones, and designed to be effective against moving targets.
Spike a 5-pound weapon, 2 ½ inches diameter, $50,000 cost and with parts off the shelf, can be air launched from UAV, or mounted on a ship for use against small swarms of boat or fired from the shoulder on the battlefield. Developed by the Navy, it is guided by a miniature camera and is described as “smallest guided missile in the world”. It is designed to shoot against soft targets, stationary or in motion like people, lightly armoured vehicles, structures, boats and small planes, and to minimize the chances of collateral damage.
Another useful technology is DARPA’s “Virtual Eye” that by combining the data from the two cameras, can reconstruct a 3D model of the environment. The Virtual Eye, enable soldiers or police to throw a couple of cameras into a building to “digitally map” a room before they enter. They can check the interior of a room for number of people, weapons they are carrying, where they are hiding and their activities before barging inside, before they’re even detected by the people in the room.
Space Security Strategy
The space is increasing becoming another domain of conflict due to enhanced militarization along with proliferation of counter space weapons like electronic warfare, anti-satellite weapons, and DEW weapons. The space security of our ever-expanding space assets from either attack or interference has become essential. So under broader concept of information dominance the goal of offensive counter space weapons, is to delay or deny an enemy’s capability to collect, process, and disseminate information by disrupting or destroying, as required, the enemy’s space systems.
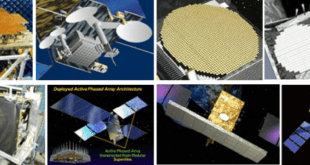
Our space security strategy should consist of four important elements: first is developing full range of military space capability like complementing our excellent imagery intelligence (photo and synthetic aperture radar), with signals intelligence (COMINT, ELINT) satellite constellations, early warning for Ballistic Missile Defence, data relay satellites, Microsatellites constellations. Launch on demand. One of space capability gaps is that we lack capability to detect ASAT launches, like Chinese 2007, ASAT weapon test, when it deliberately hit and destroyed its own aging weather satellites at an altitude of 865 kilometers. India did not have any direct independent assessment of the Chinese test. It had to depend on the delayed US information for it to know that such a test had indeed occurred. Again on May 13, 2013, China reportedly tested ASAT again that reached more than 10,000 kilometers in altitude; still we don’t know what is happening.
Space situational awareness (SSA) is the foundational element of space security, National SSA Programmes should be launched to provide dependable, accurate and timely data regarding space situation (Space debris, Artificial Space objects, Space environment and NEOs) as well as Threat Warning and Assessment for threats like ASATs, Directed energy weapons, and HAND. Comprehensive SSA requires a networked system of radars and electro-optical sensors. Recently the trend is to use space based sensors to provide timely detection, collection, identification and tracking of man-made space objects from deep space to LEO orbits.
These shall be complemented by space- and ground-based space weather sensors monitoring the electromagnetic and sub-atomic particle fluxes incident on the Earth. Our space capabilities are also critically affected by Space Weather and need to be protected in severely degraded space environment due of natural and man-made space weather degradations like HAND events. The third element is space protection. The numerous threats to our space assets demand that we develop new architectures say in MEOs which are less vulnerable to threats. For example, the U.S. Air Force placed two Space Based Infrared System (SBIRS) satellites in highly-elliptical orbits that are more challenging for China to target because of their high orbital speeds as they approach their perigee.
Satellite Clusters or satellite constellation consisting of networked microsatellites in multiple orbits can provide Robust, fault tolerant, flexible and scalable formation architectures for distributed spacecraft communication, control, and sensing. This require development of
A Formation Flying Control System which highly autonomous and which optimize the performance of the cluster by cluster reconfiguration based on mission life span, collision avoidance, and mission related requirements such as resolution, observation time, and satellite failures and subsequent performance is desirable. Of course, the final element is development of space deterrent and we have to develop satellite jammers, directed energy weapons, and ASAT capability. The India can also plan to strike ground node
On-orbit Satellite Servicing
Building and launching Satellites are costly business. Any fault could lead to making hundreds of crores satellite useless and must be replaced, which is both difficult and extremely expensive. We just heard how ISRO is working overtime to restore the communication link with its GSAT-6A satellite “which is still alive” according to ISRO Chairman K Sivan.
A new emerging technology is Space Robotics that shall enable in space satellite repair and upgrade and in future in space spacecraft assembly and building. Orbital ATK has developed first “mission extension vehicle,” (MEV) that would dock with the similarly-sized Intelsat-901 in 2019, extending its life for five years. Another player is Maxar Technologies’ SSL division, is also developing space robotic servicing vehicles with highly capable robotics and end effectors for NASA and for the Defense Advanced Research Projects Agency.
NASA is developing robotic satellites, known as “service stations in orbit,” that would not only refuel satellites, they could drastically improve their longevity and lifespan. The robots could fix minor maintenance issues, keeping up with current orbiters as they age and sustain damage. In-space-assembly is also critical to enhance space security. All these capabilities to refuel, service and assemble satellites on orbit can extend operational life and repairing or refurbishing systems in response to system degradation due to ASATs. Furthermore, these automated agents shall enhance operational performance as they shall be able to integrate new technologies into satellites like improved sensors or countermeasures against adversary’s space weapons. They could also expand or reconfigure capability to meet user or mission needs.
However, this technology is also dual use, the same automated agents which are designed to repair owns satellites can also be used to degrade or destroy adversary’s satellites. They could be weaponized with lasers or explosives. The satellites are very vulnerable by their construction. This is leading to new race among leading space nations to develop similar satellites which could function as killer Robotic microsatellites. This is also another example of robotization of warfare. We had developed ground, air and water based unmanned systems and now we have moved to space. DARPA is having even more ambitious plan to design, assemble and build satellites in space to replace satellites due to space weapons.
Near Space Domain
After space we can consider another emerging domain of warfare that is Near space. Aerospace companies including Facebook, Boeing and Google planning solar-powered plane that can fly at high altitudes for years at a time, and can provide broadband communication services. Near space, which begins at about 20km above sea level, has until now been regarded a “death zone” for drones – thin air at this altitude makes it hard to generate lift, while extremely low temperatures mean electronic components like batteries are prone to fail. Until now, the Northrop Grumman RQ-4 Global Hawk, limited to an altitude of about 19km, has been the highest-flying drone in use.
The altitude range adopted for HAP operation, around 20 km, is motivated by the facts that in these altitudes the wind speed is less intense and, consequently, the HAP requires less power to maintain position. The altitude next to 20 km also has the advantage of being positioned above the strong wind currents (jet stream) existing between 10 and 15 km. Other important advantages are a large coverage area for telecommunications and be situated above normal commercial airline traffic. The maximum altitude for controlled airspace varies from country to country, 20 km (65,000 ft) being a typical value, set at the time of Concorde commercial supersonic jet operation
Military is also turning to solar powered stratospheric drones for persistent, wide area, real time Intelligence, Surveillance, and Reconnaissance (ISR) and communications. Military has been employing various platforms like Balloons, Aerostats, Airships, and UAVs for satisfying the requirement for persistent, real time and wide area coverage of battle space. The helium powered Airships have safety issues, while satellites have been expensive to launch. Airbus is building unmanned “Zephyrs” that flying at heights of about 70,000 feet at speeds of 20mph will be used to demonstrate technology that could ultimately see the British military fielding reconnaissance aircraft that could monitor targets for months at a time.
Zephyr is a High-Altitude Pseudo Satellite (HAPS) UAV running exclusively on solar power. The UAV has all the advantages of an aircraft and satellite combined: it can be re-used and has a wide coverage due to its flexibility in location. At the same time it’s capable of taking on similar tasks as satellites: it can fly at high altitudes, perform similar applications and is reliable. The Zephyr already holds the record for the longest unmanned flight, staying aloft for 14 days in tests at a secret location in the Southern hemisphere.
Flying at 20km altitude at a fixed location, Zephyr can see over 400km to the horizon and provide persistent high-resolution imagery and high bandwidth communications to areas in excess of 1,000km2. Britain’s Ministry of Defense (MoD) will acquire three solar-powered drones, the drone’s manufacturer said. On October 13, 2015, China started the 24 hour test flight of its largest airship yet in Xilinhot, Inner Mongolia. The Yuanmeng has a volume of 18,000 cubic meters, a length of 75 meters and a height of 22 meters.
Yuanmeng will be one of the largest solar-powered airships in existence. Using solar power to drive its rotors will save additional weight in order to increase payload, and gives it a total flight endurance of six months. The Yuanmeng’s 5- to 7-ton payload of data relays, datalinks, cameras and other sensors would also be powered by the sun. The Yuanmeng aircraft can reach a height of 100 kilometers and conduct reconnaissance without being seen by other aircraft or rockets. The ship will operate at altitudes inaccessible to the majority of air defense systems.
Like its smaller American counterpart, the JLENS (currently parked outside Washington DC), the Yuanmeng can use its sensors and high altitude to detect threats such as stealth aircraft, cruise missiles, missile launchers, and warships from several hundred miles away. But the Yuanmeng has other advantages over the JLENS. While the JLENS is an aerostat, anchored to one location by a 3,000m long tether, the Yuanmeng can freely move about and be redeployed. Its high flight altitude also gives the Yuanmeng’s sensors superior situational awareness, and the ability to act as a communication rely to Chinese aircraft and drones in the event of a loss in satellite communications.
These large dimensions lead to very severe optimization requirements of HAPs structural weight. In the case of airships and balloons, the envelope material must have low weight characteristics, high strength, high ability to withstand damage (tear, pin holes), low permeability to lifting gas, maintain flexibility at low temperature and low degradation with UV radiation and ozone
The most commonly adopted solution for very long endurance HAP is, during the day, the solar energy converted into electricity by means of photovoltaic cells (solar cells), and part of this electricity is used to charge a storage system, usually rechargeable batteries or RFC for later use at night In Japan, research for the SPF airship defined as a target for the RFC system achieving a specific energy of 450 Wh/kg. The current systems have 350 Wh/kg of specific energy
In the definition of HAP equipment, it should be considered that the environment in the stratosphere has aspects similar to the space, such as very low temperatures, marked temperature cycles (day/night) and intense solar radiation and UV (Keck Institute for Space Studies 2014) Another important technology that is weaponizing this near space domain are Hypersonic weapons and platforms. NASA categorizes speeds between Mach 5 (6125 kilometers per hour) to 10 Machs as Hypersonic.
Air & Space Superiority Through Hypersonics
The era of hypersonic flight had arrived. They provide revolutionary military capability like prompt global strike, launch on demand, satellite servicing and antisatellite missions. There are range of hypersonic missions which are being considered. One of the mission is faster global transportation for both military and civilian purposes. Countries are developing future hypersonic Spaceplanes, enabling intercontinental travel at very high speeds.
Common Aero Vehicle (CAV) is a hypersonic vehicle mainly gliding in the near space, the region of atmosphere with altitude of 20-100 km. With the benefit of L/D up to 3 and initial speed close to the first cosmic velocity, the glide range of CAV can be more than ten thousand kilometers while its lateral maneuver range can also be up to thousands of kilometers.
US Air Force X-41 is a Common Aero Vehicle (CAV), or space plane that is able to transport 1000 lb payload on sub orbital route at hypersonic speeds as well as releasing that load to atmosphere. It could deliver a range of conventional weapons at hypersonic speeds to counter ASAT launches.
Russia and China are testing Boost glide vehicles. An unpowered hypersonic vehicle is carried to altitude (boosted) by a rocket, detaches in the vicinity of 100 km altitude, and subsequently glides on the top of the atmosphere at speeds of 8–10 Mach. This type is also known as hyper-glide vehicle (HGV)
A hypersonic ISR drone could enter and exit enemy territory, sending back imagery without being detected by enemy sensors in time to react. To meet future requirements, DARPA envisions a survivable and affordable hypersonic regional ISR aircraft with the following attributes: Range greater than 1200 nm, Speed greater than Mac 5 and 60,000+ ft operation.
Weapons travelling at hypersonic speeds would present serious complications for enemy defences with only seconds available to respond against the incoming attack. Additionally, such weapons can destroy targets without any explosives, using their kinetic energy alone. For example, the energy delivered at the target by a small 20 kg hittile travelling at Mach 6 may compare to the energy of an exploding Mk-8 42,000 lbs (900kg) general purpose bomb. A high-flying hypersonic air vehicle could have sufficient kinetic energy to launch a small mission payload into low earth orbit. Space access not only requires the attainment of very high vehicle velocities but also must traverse the varying atmospheric layers to reach an orbital path.
Global access missions also benefit from hypersonic speeds but do not require the large orbital altitudes. Therefore, HV systems provide the desired speeds but demand complexity.
Hypersonic technology is extremely difficult to master.
However, hypersonic speeds are frequently limited not by available thrust or drag, but by the heat buildup caused by atmospheric friction. The temperatures hitting the aircraft can reach anywhere from 2,000 to 3,000 °C. The structural problems are primarily caused by processes called oxidation and ablation. This is the when extremely hot air and gas remove surface layers from the metallic materials of the aircraft or object traveling at such high speeds. At speeds above Mach 10, air molecules break apart creating an electrically charged plasma layer around the aircraft. Plasma interferes with electronics making it difficult for ISR sensors to operate in a boost-glide reusable vehicle. Weapons employment is also a challenge, as it is difficult to model how weapons bay doors or the weapons themselves will behave at hypersonic speeds.
Many enabling technologies are required for hypersonics. As a closed system, internalized by the plasma sheath formed around the exterior, the vehicle will rely on an inertial reference system for mid-course and terminal guidance to navigate to a pre-planned position. Any weapon travelling at hypersonic speed in its terminal phase will need a very accurate, low-error tolerance, and a high-speed fuzing mechanism that will initiate the on-board warhead and accurately deliver the damage effect to then target. Air-breathing hypersonic vehicles require tightly integrated airframe and propulsion systems to manage drag and heating.
Hypersonic flights, re-entry, and propulsion vehicles, regardless of their design, require maneuverability of materials against high temperature erosion more than 2400°C. Melting temperature is only one of the many properties required of the materials. As most engine and hypersonic leading edge applications will involve exposure to oxidizing fuels or aero-heating, all non-oxide materials will undergo oxidation to form some combination of solid, liquid, or gaseous reaction product. It is the oxidation behavior that is one of the primary constraints associated with the selection process of UHTC materials. Additionally, the adverse environmental effects include detrimental effects of chemical reactions, mechanical stresses and radiation.
Hypersonic flights require ultrahigh temperature materials (UHTM). These are materials with temperature capability greater than 1650 °C and able to withstand extreme erosive / corrosive environments. UHTM should possess high strength at high temperatures, oxidation resistance, ablation resistance, thermal shock resistance. These materials will be required for hypersonic air breathing vehicles, hyper speed cruise missile, hypersonic aircrafts, re-usable launch vehicles to protect leading edges and nose cones that experience very high temperatures (> 2000 °C). Refractory diboride composites like ZrB2, HfB2 etc and multilayer coatings of HfC, SiC on C-C composites are most promising UHTM candidates.
Now Researchers from Imperial College London in the UK discovered that the tantalum carbide and hafnium carbide materials can withstand scorching temperatures of nearly 4000 degrees Celsius. Being able to withstand temperatures of nearly 4000°C could pave the way for both materials to be used in ever more extreme environments, such as in heat resistant shielding for the next generation of hypersonic space vehicles. Aerodynamic drag roughly scales with the square of airspeed; double the speed, and the drag goes up four times. Streamlined shapes have partly overcome this problem, but the solution then, as it is now, is more thrust.
The development of hypersonic propulsion systems have been riddled with two intertwined, seemingly intractable challenges: The top speed of traditional jet-turbine engines maxes out at roughly Mach 2.5, while hypersonic engines such as scramjets cannot provide effective thrust at speeds much below Mach 3.5. This gap in capability means that any air-breathing hypersonic vehicles developed today would use disposable rockets for one-time boosts up to operating speed, limiting the vehicles’ usefulness.
Therefore countries are experimenting with new concepts and developing next generation engine technologies for hypersonic flight. Lockheed Martin is working with Aerojet Rocketdyne to find a way to integrate a turbine engine, which would get the plane up to Mach 3, with a supersonic ramjet engine, or scramjet, to push it to Mach 6. DARPA has launched its Advanced Full Range Engine (AFRE) program to develop and demonstrate a new aircraft propulsion system that could operate over the full range of speeds required from low-speed takeoff through hypersonic flight.
A scramjet (supersonic combustion ramjet) is a variation of a ramjet with the distinction being that the combustion process takes place supersonically. At higher speeds, it is necessary to combust supersonically to maximize the efficiency of the combustion process and to avoid the losses induced by a final normal shock. ISRO (Indian Space Research Organisation) has successfully test-fired its Scramjet Rocket Engine On 28 August 2016, a breakthrough technology in air-breathing propulsion. The Scramjet engine designed by ISRO uses Hydrogen as fuel. Says ISRO, “Air-Breathing systems become much lighter and more efficient leading to reduced overall costs.” India is the fourth country to demonstrate the flight testing of Scramjet Engine.
Future Aerospace Dominance
Aero Domain Threats
China has already deployed its J-20 fifth generation stealth fighter jet, to the South China Sea and is armed with live weapons to patrol the disputed waters. The multi-role J-20 offers the People’s Liberation Army Air Force the ability to penetrate defended airspace to deliver its large payload of weapons. Due to its larger size it will carry significantly more internal fuel, so it will have a longer range and be less dependent on vulnerable aerial refueling tankers in the vast Asia-Pacific. J-20 is meant to have much greater range and endurance than F-22. Its long combat radius of approximately 2000 km (1242 miles) will provide China a long-range strike system capable of reaching targets within Japan, Taiwan, Philippines, Vietnam and Guam. Therefore, we need to develop counter stealth systems.
Our adversary has developed large arsenal of short, medium, and intermediate-range ballistic missiles; long-range, land-attack, and anti-ship cruise missiles therefore we need to develop Integrated Air and Missile Defence Network which can deal with these threats. Advanced Electronic warfare shall be employed in the battlefield therefore our Air assets should be Jam Resistant augment Alternative GPS technologies.
It has tested its hypersonic platform prototype seven times and on the way to operationalization. Therefore, we also need to develop hypersonic platforms and missiles and again DEW weapons can be effective in countering these threats. Similarly, it has also developed Advanced Integrated and networked Air defence Systems and purchasing Russian S-400 systems. Therefore, to carry our missions under this operating environment we need to have Fifth Gen Stealth fighters, UCAVs, UAV Swarms and Collaborative Manned and Unmanned Missions
Sixth generation gighter aircraft
Many countries including China are planning “sixth generation” of fighter jet Future Airspace dominance. They are evaluating what should be desirable capabilities of those planes. First is that they must be able to operate in the anti-access/area-denial environment that will exist in the 2030–50 timeframe. The future system will have to counter adversaries equipped with next generation advanced electronic attack, sophisticated integrated air defense systems, passive detection, integrated self-protection, directed energy weapons, and cyber-attack capabilities.
Russian has planned that its next gen aircraft shall be unmanned capable of reaching speeds above 11 thousand kilometers per hour, is super-maneuverable and is capable of maneuvering into the near outer space. A Russian sixth-generation fighter will be fitted with a unified electronic warfare system, which will serve as a radar, an electronic warfare system, a data transmission system and as communications equipment. Additionally, it will function as a navigation system and as an IFF transponder.
China’s has planned J-28 will also act as an information platform or a node of the battlefield network transferring enemy targets information to whole C4ISR system in real-time to provide decisive decision-making as well as utilizing information from network to maximizing combat performance. It will carry laser weapons and terahertz radar.
SAAB is advocating instead “high-powered electronic attack to deny shared situational awareness and targeting data, and to negate data networks”. Germany and France have come together to develop Future Combat Air System (FCAS) will be a “system of systems” that combines manned and unmanned aircraft into one operational unit. FCAS could be both manned and unmanned, and manned versions could fly alongside and control unmanned versions. The twin-tail stealth design would be a twin-seat design, which would see it operate in a wider battle network, potentially as a command and control asset or UCAV/UAV mission commander. Sixth generation aircrafts shall also carry laser directed energy weapons.
Laser Directed Energy weapons on Aircrafts SHIELD laser DEWs
The first new generation laser weapon that was deployed in a combat theater was a 30-kilowatt Laser Weapon System (LaWS) deployed on USS Ponce in 2014. The system, offers military leaders precision accuracy at cost as low as a dollar per shot. ONR showed off a video disabled a small Scan Eagle-sized UAV, detonated a rocket propelled grenade (RPG) and burned out the engine of a rigid hull inflatable boat (RHIB).
A laser’s ability to disable a target depends in large part on the power and beam quality of its light beam. The power of the light beam is measured in kilowatts (kW) or megawatts (MW). Beam quality (BQ) is a measure of how well focused the beam is. Something on the order of 10,000 J/cm2, delivered in a sufficiently short time would be adequate to damage most targets.
Currently countries are preparing to demonstrate tactical laser weapons with outputs of hundreds of kilowatts. These DEWs can be used in varieties of missions such as wide-area, ground-based defense against rockets, artillery and mortars (Counter RAM); engage Low flying Aircraft and helicopters, and UAVs; They shall also enable precision strike missions for airborne platforms; and shipboard defense against cruise missiles. US Navy is planning to test a 150-kilowatt solid-state laser weapon system aboard its amphibious warships. Lasers with power levels in the megawatts could have ability for countering counter manned aircraft and some missile including supersonic ASCMs and ballistic missiles—at ranges of up to about 10 nautical miles. These future category Strategic laser weapons which can be both endo or exo-atmospheric and will be deployed on high altitude Airborne, space based / satellite based platforms or space relayed (Endo-atmospheric with Orbiting Relay Mirrors) for countering Tactical Ballistic Missiles (TMD) – boost phase defence, ICBMs (NMD) – boost phase defence and Anti Satellites (ASAT).
There are two important technologies that are enabling these DEWS. One are Fiber lasers due to their many advantages like: high electrical to-optical efficiency (40%), high reliability for operation in harsh military environments, and high beam quality near diffraction-limited light output. However, the power of state-of-the-art single-mode fiber lasers is limited by thermal and nonlinear effects like thermal lensing to ∼10kW. Second are Beam combining technologies to combine multiple low-power lasers with good beam quality into one high-power beam helps in overcoming power limitations of fiber lasers. In future for strategic applications Free electron lasers are good candidate as their power can be scaled up in power from 10 kW to 1 MW without any increase in the size of the system or need for a beam combiner (a component that adds to system complexity and cost).
Laser beams begin to cause plasma breakdown in the atmosphere at energy densities of around one megajoule per cubic centimetre. This effect, called “blooming,” causes the laser to defocus and disperse energy into the surrounding air. The scintillation of atmosphere also causes severe distortion or beam focusing. This requires Adaptive or deformable mirror consisting of thousands of miniature actuators that continuously predistort the beam for it to remain focused.
Laser Weapons require beam control/fire control (BC/FC) system that tracks a target, measures range to the target, compensate for atmospheric turbulence, select an aimpoint (vulnerable area) on the target, focuses and points the laser beam. A high precision target tracking system is needed and beam pointing system having extremely low jitter depending on the distances involved.
However, Lasers are not all weather weapons. The most important variable that effects the laser beam is the atmosphere. Lasers cannot penetrate cloud, fog, haze, sandstorm or aerosols. Because laser beams must be propagated through the atmosphere, they can be affected by airborne particles (dust, smoke), water vapor or atmospheric turbulence that absorb, bend or scatter laser energy.
Since laser light tends to fly through the atmosphere on an essentially straight path, shipboard lasers would be limited to line-of-sight engagements, and consequently could not counter over-the-horizon targets or targets that are obscured by intervening objects. Laser Weapons are now being planned for future sixth generation aircrafts that will significantly increase engagement ranges compared to ground-based systems. US Air Force Research Laboratory released a request for information (RFI) for a laser weapon that could be mounted on next-generation air dominance fighters by the 2030s.
The Air Force is interested in three categories of lasers: low-power for illuminating, tracking, targeting, and defeating enemy sensors; moderate-power for protection to destroy incoming missiles; and high-power to offensively engage enemy aircraft and ground targets. The Air Force plans to scale-up laser weapon to 150 kW and then 200 kW. A 200kW laser cannon will be able to destroy surface-to-air and air-to-air missiles apart from armored vehicles on the ground.
DARPA’s HELLADS program is developing a 150-kilowatt (kW) laser weapon system, with a weight goal of less than five kilograms per kilowatt, and volume of three cubic meters for the laser system. The weapon is planned to be deployed on AC-130 which is powered by the four Rolls-Royce T56-A-15 engines each producing 3.9 megawatts of power, enough to power a 200 kW laser weapon. AFRL Self-Protect High Energy Laser Demonstrator (SHIELD) integration and demonstration programs is addressing the risk of integrating on LWS onto an aerial platform. The program will develop and integrate a more compact, medium-power LWS onto a fighter-compatible pod to demonstrate effectiveness of an LWS in a relevant flight environ-ment for self-defense against ground-to-air and air-to-air weapons.
The SHiELD system has three subsystems, the beam control system SHiELD turret research in aero effects (STRAFE) that will direct the laser onto the target and laser pod research and development (LPRD), which is a pod mounted on the tactical fighter jet to power and cool the laser. It also includes the high-energy laser itself, Laser Advancements for Next-Generation Compact Environments (LANCE), which can be trained on adversary targets to disable them.
The AFRL has split the SHiELD program into three separate development contracts:
1USD39 million contract, awarded to Northrop Grumman in August 2016, for the development and production of the SHiELD Turret Research in Aero Effects (STRAFE) – the beam control system which characterizes the tight environment for atmospheric disturbances that could distort the laser beam, acquires and tracks incoming targets, determines an aim point for the laser, then ‘shapes’ and focuses the outgoing beam on the target;
USD 90 million contract, awarded to Boeing in December 2016, for the Laser Pod Research and Development (LPRD) component – the LPRD contract provides for system integration into a pod, and integration of that pod onto anaircraft;
The USD b 26.3 million contract, awarded to Lockheed Martin in early November for the development of the LANCE high-energy fiber laser. LANCE, coupled with the STRAFE beam control system will be integrated into the LPRD pod, along with the systems required to operate it, which will then be integrated onto the tactical fighter testbed aircraft and subsequently trialled on a tactical fighter jet by 2021.
There are variety of obstacles impede the utilization of an airborne laser weapon system, several of which have been identified as being most crucial to its success or failure. Most fundamentally, it is essential to maximize laser power while reducing volume and mass, maintaining a size, weight, and power (SWaP) that offers tactical effectiveness. Moreover, beam control systems must be adequately advanced to enable precise aiming, tracking, and pointing amidst the aero-mechanical jitter induced by vibrations during flight. Similarly, system temperature must be controlled via the dissipation of waste heat, and high-speed aerodynamic flow must be mitigated to avoid aero-optical disturbances. Should any of these elements be allowed to dominate, the laser beam can disperse, losing its precision and effectiveness at operational ranges. Finally, it is important to note that a laser system is a complex piece of technology, which must be ruggedized into a compact package capable of surviving a battlefield environment.
V/STOL
VTOL technology means aircraft can theoretically take off and land almost anywhere, making them far more flexible. They’re also able to perform various manoeuvres not possible with a conventional plane; a significant advantage for aircraft in combat situations. They also have some deficiencies: first is the fuel consumption is too large, take-off requires a third of the amount of oil consumed, so on the voyage is greatly reduced. This also has impact on the bomb load which is small.
Lockheed Martin has designed the F-35B Standard Take-off and Vertical Landing (STOVL) a single-engine, fifth generation fighter aircraft which minimizes these disadvantages. It is the first aircraft to combine stealth technology and supersonic speeds with STOVL capabilities. The F-35B can fly at a maximum speed of 1,960km/h. The combat radius and maximum range of the aircraft are 833km and 1,667km respectively. The weapon loads and cockpit layout of the F-35B are similar to those of the F-35 Joint Strike Fighter (JSF). The Rolls-Royce LiftSystem,”Three Bearing Swivel Module” (3BSM) is a thrust vectoring nozzle which allows the main engine exhaust to be deflected downward at the tail of the aircraft.
What are military capabilities it has enabled. Since now more ships capable of operating high-performance, low-observable, multi-role fighters, It has in fact doubled its theoretical fixed wing capable, carrier force. landing aircraft, for sea warfare is a great advantage. By eliminating the preparation time on the runway, operational response time greatly improved. Last year Taiwan’s Quadrennial Defense Review” (QDR) that the country plans to acquire stealth fighters and vertical/short takeoff and landing (V/STOL) aircraft to strengthen its defense forces. One RAND report analyzing the threat of China to Taiwan it said: China’s procurement and development of fighter aircraft, surface-to-surface ballistic missiles, land-attack cruise missiles and bomber aircraft advancements are not slowing, and could pulverize Taiwan’s air bases within hours of a war, the report says. None of Taiwan’s fighter aircraft would survive or be deployable on runways turned into a lunar landscape.
So this was reason of Taiwan’s purchase of VTOL aircrafts. This technology has advantage that you can always operational, can be in place a small landing can be in building or any other ground easily camouflage. On the battlefield survival rate is the highest. Followed by the aircraft carrier can be equipped with many China itself has successfully tested its vertical takeoff and landing fighter during field test as reported by Japan in 2016.VTOLs have much more control to move forward, backward, and up and down, spin around, etc which may be able to better counteract turbulence and wind encountered in urban environment. All of designs have one thing in common that is they should have directed energy weapons.
UAV Threat Range
Future warfare is going to be unmanned, and our adversaries are integrating in large numbers of UAVs into their forces and during peacetime too there is ongoing intrusion of adversary UAVs, collecting intelligence from our Borders. Considering the UAV threat, it has wide spectrum. On one end is the security threat of terrorists weaponising small commercially available drones. ISIS is already using them in in Syria and Iraq to carry small improvised explosive devices. They can also be used to disperse biological or chemical agents. These are small in size (e.g., < 25 kgs.) making them difficult to detect, they fly at low altitudes (e.g., < 125 m) which make them easily hidden by background urban structures, they are slow (e.g., < 150 Km/ hr) which make them difficult to differentiate from other targets like birds. In addition, they also have low IR signature and depending on model may generate small amount of acoustic noise.
Other is military threat of military UAVs of China, which has full equivalent of western UAVs like Predators, Global Hawks to UCAVs. China has become biggest manufacturer and exporter of drones. One of their characteristic is they have large payload capability in tons because of which they can carry large number of weapons. Endurance and stealth is also fast becoming close to American counterparts. Therefore, there is need to develop counter UAV technologies to neutralize them. The Indian army and air force are seeking more than 70 counter-UAS systems as part of the Ministry of Defence’s’ Technology Perspective and Capability Roadmap – 2018 (TPCR-2018).
Counter UAV Systems
To countering UAV threat many drone detection and neutralization technologies are being developed. One is the shoulder-mounted launcher system that fires a projectile that deploys a large net to physically capture it, and also deploys a parachute to bring it down safely. Phantom Technologies has launched Eagle 108 Tactical Jammer designed for the detection and jamming of drones. It has been designed to neutralize unauthorised drone / quadcopter that has entered a secured field / campus / sport event.
The system uses passive detection scheme, scans using an array of directional antennas. Once a threat is detected, an automatic command to the jamming unit blocks all radio communication channels. Forcing the drone to drift away and lose communication with its operator. The detection radius is more than 1km and jamming radius is up to 2km. US Army has modified its counter missile Enhanced Area Protection and Survivability system to counter drones. The system uses a precision tracking radar interferometer to detect and track UAVs, a fire control computer to perform computations, a radio frequency transmitter and receiver and a standard 50mm cannon to launch the projectile. The prototype uses a readily available 50-millimeter Orbital ATK Bushmaster III cannon to launch command guided interceptors. Army says it has range of more than a kilometer.
The most comprehensive commercial system is British AUDS system that claims to counter micro, mini and larger unmanned aerial vehicles (UAV) or drones. The system can detect drone five miles (8 km) away using electronic scanning radar, track it using infrared and daylight cameras disrupting the flight using an inhibitor to block the radio signals that control it. Latest version features a quad band radio frequency (RF) inhibitor/jammer, as well as optical disruptor. The quad band inhibitor disrupts the different licensed telemetry bands of commercial drones no matter where in the world they are designed and licensed for use. For example, both the 433 and 915 MHz frequencies commonly used by unmanned aircraft systems (UAS) can be disrupted as can the 2.4 GHz control band and the global satellite (GNSS) bands.
The optical disruptor can be utilised for both pointing at a drone for identification purposes and disrupting the automatic gain control settings in the drone’s camera system such that the operator loses visibility. The optical disruptor can also provide a very precise identification of known UAV launch activity to any ground forces.
Next are Directed energy weapons, Many counter drone laser directed energy weapons have been demonstrated. One of the comprehensive system is by Rheinmetall has demonstrated the effectiveness of highenergy lasers in the 5 kW-class in an APC, the 20 kW class in a Boxer infantry fighting vehicle as well as the 50 kW-class in an 8X8 truck container. The Mobile HEL Effector Container L in the 50-kW laser class demonstrated the detection, tracking and subsequently neutralization of optics of unmanned aerial vehicles at ranges of up to 2,000 metres. These systems are meant for small UAVs, but what about these predators and Global Hawks. We also must find ways to neutralize them.
One of the system we are getting from Russia the S-400 Triumph air defence system can engage all types of aerial targets including aircraft, unmanned aerial vehicles (UAV), and ballistic and cruise missiles within the range of 400km, at an altitude of up to 30km. The system can simultaneously engage 36 targets. It integrates a multifunction radar, autonomous detection and targeting systems, anti-aircraft missile systems, launchers, and command and control centre. It is capable of firing three types of missiles to create a layered defence.
Arrival of Offensive & Defensive Swarms
‘The vulnerability of large UAVs due to their large radar cross section is now driving military to UAV swarms which shall be difficult to detect and engage. These Swarms can find, fix, and communicate precise target location of ground, sea, and air targets and they can serve as weapons platforms to attack air defense systems from multiple axes
Swarms of ‘mini’ or ‘micro’ UAVs would offer advantages such as: low observability due to small radar, infrared and acoustic signatures; reduced mission risk as the swarm can be spread out; operational flexibility; mission sustainability because even if some individual UAVs are lost, the remaining swarm can complete the mission; and cost effectiveness because each small UAV is relatively cheap.
To survive and successfully perform missions, autonomous systems must be able to sense, perceive, detect, identify, classify, plan for, decide on, and respond to a diverse set of threats in complex and uncertain environments. Another is collaborative autonomy, so that UASs would perform their mission by sharing data, negotiating assignments, and synchronizing actions and communications among team members and with the commander. Another is human-system interface (HSI) is designed to allow a single person to visualize, supervise, and command a team of unmanned systems in an intuitive manner.
The most important challenge is to enhance their endurance which can be through the ability to refuel or recharge in flight or remote recharging through directed-energy transmission. To solve this endurance challenge, DARPA’s Gremlins program aims to use C-130 transport aircraft, fighter jets and bombers to launch and retrieve swarms of drones in mid-flight once they complete their missions and then reuse those unmanned systems for up to 20 times.
In June 2017, the state-owned China Electronics Technology Group Corporation, or CETC, conducted its own record-breaking swarm experiment with nearly 120 unmanned fixed wing aircraft, as well. This event included simulated missions where the entire formation acted as a whole and instances where smaller groups broke away to complete separate objectives. There is also need to develop efficient swarm tactics. The US Defense Advanced Research Projects Agency (DARPA) has commenced a project to explore how swarms of robots could be used to operate alongside army and marine units at the company level and below.
OFFensive Swarm-Enabled Tactics (OFFSET) seeks to dramatically increase the effectiveness of small-unit combat forces operating in urban environments by developing and demonstrating 100+ operationally relevant swarm tactics that could be used by groups of unmanned air and/or ground systems numbering more than 100 robots.
These swarm tactics for large teams of unmanned assets would help improve force protection, firepower, precision effects, and intelligence, surveillance, and reconnaissance (ISR) capabilities.
Land Dominance
Our future forces should be combat effective, adaptive, deployable, informed and agile, versatile, precise and lethal, survivable and sustainable. They also should be better networked and capable of operating in a joint engagement environment. Corresponding platforms also need to be versatile, efficient and with very small footprints.
Indian Army’s armored directorate has begun setting requirements for small light tanks to weigh about 22 tons and be capable of operating at heights of more than 3,000 meters in hilly terrain. The tanks would need to be able to penetrate highly protected armored vehicles and main battle tanks from more than 2 kilometers, as well as be able to fire highly explosive anti-tank shells and guided missiles. Earlier China also tested its homegrown light tank, Xinqingtan, which is equipped with a 105mm main gun and a 1,000-horse-power engine. The Xinqingtan was tested in July 2017 in the Tibet region bordering India.
Indian Army is seeking HMV based tactical high energy laser systems Weapon system should be capable of an effective range of 6-8km. A LASER weapon system to cause physical damage/destruction to EW systems, communication systems and non-communication systems/radars and their antennas. (b) Should be also effective against microwave towers, cellular towers, and cables. (c) (d) Should be capable against small aerial targets/objects. Phase II (a) Should be effective against soft skinned vehicles and troops. (b) Range should be upto 20 KM and beyond. Should be capable of antisatellite role from ground and aerial platform. Should be as effective in ground-to-ground role as for ground-to-air role. Should have gyrostabilised aiming and target locking capability.
What are some of the capabilities US army is looking at:
Army Research Laboratory is working on Collaborative Cooperative Engagement (CCOE) programme which aims to develop a swarm of precision weapons which can defeat the countermeasures which are only designed to protect against one or two simultaneous missile attack.
Frank Fresconi are also proposing a Parent-Child scheme to achieve performance metrics with simplified components and reduce overall costs. The idea is to link an individual smart munition with a flock of dumber, cheaper companions. The smart weapon handles all of the tricky navigation and target identification; its companions just have to work out where they are in relation to their master, and then go where they are told. Data are passed between them in brief radio chirps. The precision swarm of smart weapons shall also be having capabilities of accurately engaging targets in urban terrain with low collateral damage.
Tactical High-Performance Computing (HPC) effort will provide 100 Petaflop computing power in the battlespace to enable real-time processing for Soldiers operating at the tactical edge and improve mission effectiveness and mitigate risk in hostile environments. Computing power of this magnitude is also an enabling technology for autonomous systems and real-time data analytics for Soldiers and intelligence analysts.
Maximizing Soldier Effectiveness
The vision for the future soldier is to be combat effective and highly mobile, adaptive, networked, sustainable with total battle space situation awareness and information assurance. Therefore, he is equipped with night- vision goggles, radios, smartphones, GPS, infrared sights, a laptop as well as batteries to power them. Some of the missions the soldiers perform can take weeks, away from in difficult terrain like deserts and mountains which requires maintaining an incredibly high level of physical fitness. Around the world, armies are recognizing the importance of maximizing the effectiveness of Soldiers physically, perceptually, and cognitively.
Militaries are developing exoskeleton technologies designed to increase the physical strength of the Soldier or increase their endurance. Today’s exoskeletons allow soldiers to carry 17 times more weight than normal and march with significantly less strain on the body. With an XOS 2 suit, for example, a solider can carry 400 pounds but feel the weight of only 23.5. Cina’s Norinco, has debuted its second-generation military exoskeleton, can allow the user to carry over 100 pounds, with enough charge to walk 20km at a speed of 4.5 km/h. The new version is also lighter, which will likely reduce strain felt by the exoskeleton’s wearer, making it a better choice for troops in mountainous terrain.
UK’s Dstl’s dismounted close combat sensors (DCCS) system is wearable sensor technology that provides GPS-free navigation, and automatic threat detection. By using inertial and visual navigation sensors, the DCCS accurately tracks the location of an individual within buildings and tunnels.Its acoustic and camera technology automatically identifies where enemy weapons are being fired from and this information is transmitted to the wearer and to commanders. DCCS is expected to enter service in the 2020s.
The Russia’s Ratnik infantry combat gear has advanced voice command system to help servicemen survive during a possible military conflict. The voice control system frees a soldier’s hands and eyes during fighting, and he can simultaneously move, shoot, and interact with the computer. Also, he can communicate with the command, send messages and listen to the advice of an advanced automated system as well as receive ciphered voice messages,” he said. The Russian army’s Ratnik uniform kit could be equipped with newly-developed Mukha unmanned armed vehicles (UAV).
Naval Dominance
Defense Ministry report had warned of the “grave threat” posed by the Chinese navy in the Indian Ocean. China is stepping up its undersea activities in IOR. The Indian Navy has been tracking at least six Chinese submarines in the IOR, over the last four years. China has also planned to sell 8 Chinese Yuan-class conventional diesel-electric powered submarines to Pakistan. Indian In response has inducted of the US-built P8-I anti-submarine warfare jets to track Chinese submarines in the Indian Ocean.
US is also facing this asymmetric threat through Russia’s new generations of conventional and nuclear propulsion submarines Yasen, Lada, Borei and Kalina classes of submarines, that are significantly more difficult to detect and track for western naval forces. US is developing range of technologies to tackle this asymmetric threat. DARPA has launched Distributed Agile Submarine Hunting, or DASH, effort is to find an adversary’s quiet submarine using advanced standoff sensing from unmanned underwater systems. Through a scalable number of collaborative sensor platforms that use multiple sensing modalities, the program will demonstrate system solutions to detect and localize submarines over large areas in both shallow and deep water environments.
DARPA under its MOCCA program is developing technology to enable submarines to detect other submerged vessels at greater distances, while minimizing the risk of counter-detection. Most sonar systems are monostatic, in that the transmitter and receiver are in the same place. But DARPA wants a Bistatic sonar describes would leverage the benefits of active sonar systems while protecting the submarine’s location, since the pings would be coming from a UUV at some unknown distance from the submarine.
Under MOCCA program, an attack submarine shall launch a small UUV 21 inches in diameter or smaller, and may operate in littoral waters, the bottom of the ocean and other challenging environments. The UUV will carry a small but powerful sound projector, which shall transmit sound pings of high volume. The sound reflected by enemy submarines shall be received by attack submarine and be used to detect and track enemy submarines at long ranges. The volume available for the projector is highly constrained which makes high-output transducer materials a necessity. Innovative sonar transducer concepts and designs should consider high-drive materials, efficient power-amplifiers, and compact array projector configurations that will optimize sound output in a UUV volume-and-energy constrained package.
The U.S. Navy under Anti-Submarine Warfare (ASW) Continuous Trail Unmanned Vessel (ACTUV) program has developed unmanned surface vehicle (USV) designed to operate and patrol autonomously for 60-90 days straight, being able to track quiet diesel-electric submarines and avoid surface ships by itself. The ACTUV is designed to out-endure any diesel-electric submarine, even those equipped with Air Independent Propulsion (AIP) at a fraction of their size and cost. Once the enemy sub is spotted it could guide other U.S. naval assets to the vessel’s location to destroy it. Submarines themselves are being upgraded with new concepts and technologies from sonar absorbent composites, advanced propulsion systems like AIP and nuclear, ultrafast through super cavitating, mind controlled, equipped with laser based communications.
US navy’s recent Virginia-class attack submarines can even launch UUVs and UAVs. It has replaced standard Tomahawk compartment with Virginia Payload Modules in tubes can hold these other payloads. Sensor payloads under development include a submerged launched Unmanned Aerial Vehicle (UAV) and a remotely launched Unmanned Underwater Vehicle (UUV). Another underwater technology is Blue-green lasers for high bandwidth underwater wireless communication because of its high data transfer rate, reasonably large range, small size, low power consumption, immunity to interference and jamming and covertness of transmission. Blue and blue-green laser wavelengths can penetrate sea water so offer the potential of improved submarine communications.
Cyber Warfare
India is continuously a target of many cyber-attacks, cyber espionage and cyber warfare campaigns from our adversaries. The vulnerability of Indian critical infrastructure is further increasing under Digital India with increasingly networking of critical infrastructure like transportation networks, power grids and financial institutions. As our Military is migrating to Net-centric operations, military networks and key supporting critical infrastructures are now at significant risk from cyber intrusion. Large hardware imports from China is also leads to growing threat of hardware attacks through malicious insertion of malware or kill switch. Government has also taken much cyber security Initiatives like implementing National Cyber Security Policy, establishing Computer Emergency Response Team (CERT-IN) and the National Critical Information Infrastructure Centre (NCIIC) and creating a new cyber agency, which would be a precursor to a cyber command.
The cyber strategy has four areas important areas: Cyber situation awareness, cyber defence, deterrence and developing cyber capability.
Situational awareness is the dynamic understanding of the current and projected state of own and other systems and actors and is necessary for decision making. It involves Intelligence or collection, processing and analysis of information pertaining to cyberspace and its actors. Threat estimation, or judgment of the possible technical nature of threats (e.g. hardware or software based), likely manifestations (e.g. intermittent loss of communications) and the potential impact on cyber and interdependent systems. Generation and sharing of cyber indications and warnings are generated and shared regarding the movement of high-end state cyber-threat activity towards our networks and information assets. This would allow Planning and shaping includes the selection and use of capabilities to influence and shape the cyber environment to support operations.
Cyber Defence deals with protecting computers, networks and data. The mission is to protect information and information infrastructure in cyberspace, build capabilities to prevent and respond to cyber threat, reduce vulnerabilities and minimize damage from cyber incidents through a combination of institutional structures, people, processes, technology and cooperation. Second, extending/enhancing automated intrusion protection and developing resilience efforts, starting with data classification and segmentation, to militaries, telecommunication companies, and electrical grids.
Information assurance encompasses the confidentiality, availability and integrity of information whether it is stored (at rest), being processed (in use) or transmitted (in transit). Utilize high-end protection capabilities, such as multi-factor authentication, end-to-end data encryption and diverse, redundant networks, to ensure best information assurance practices in data confidentiality, integrity, and availability. Equally important is the ability to recover, reconfigure, operationalize and restore all ICT assets/ services after any national scale cyberattack in a short period of time. The required future capabilities are predictive models of adversary networks, tamper resistant, immune networks and systems, automated remediation etc.
Another important element is development of offensive capability which enables ability to have active presence within the adversaries’ information infrastructure, stealthily ex-filtrate any remotely-located open or closed information systems to discover unknown information and launch surgical strikes for Deceive, Deny, Disrupt, Degrade, Destroy (D5) effects.
The deterrence consists of developing capability to destroy critical infrastructure such as power, telecommunications or banking by damaging the computer systems that control those infrastructures. It also calls for setting up Unified cyber commands for more effective and coordinated efforts for conducting cyberspace operations, both offensive and defensive. The offensive operations are seen as deterrent to adversaries. Militaries are developing cyberweapons which are malware agent employed against specific targets for military, paramilitary, or intelligence objectives.
Stuxnet was the first cyberweapon
Stuxnet was the first cyberweapon, discovered in 2010 and the subsequent information leaks confirmed that the trojan was indeed a state sponsored malware designed to damage the targeted industrial control systems for a specific type of centrifuge equipment in a special nuclear facility in Iran. First, it targeted Microsoft Windows machines and networks, repeatedly replicating itself. Then it sought out Siemens Step7 software, which is also Windows-based and used to program industrial control systems that operate equipment, such as centrifuges. Finally, it compromised the programmable logic controllers. Just as missile is comprised of three basic elements, the delivery vehicle (rocket engine), followed by a navigation system (tells it how to get to the target) and finally the payload (the component that causes harm) cyber weapons also contain the same three elements. It may be delivered through Emails with malicious code embedded, web sites that can have malicious links and downloads.
Just as navigation system guides a missile; it allows the malicious payload to reach a specific point inside a computer, system or network. System vulnerabilities are the primary navigation systems used in cyber weapons. Vulnerabilities in software and computer system configurations provide entry points for the payload of a cyber weapon.
A ‘weaponised’ exploit must then be created in order to deliver and install the malware on the target, and covert communications must be established back to the attacker in order to await further instructions, or capture data for exfiltration
In a cyber weapon the payload could be a program that copies information off of the computer and sends it to an external source. It can also be a program that begins to ease or alter information stored on the system.
Cyber warfare also requires development of techniques, tactics, and procedures (TTPs). Militaries are setting up Unified cyber commands for more effective and coordinated efforts for conducting cyberspace operations, both offensive and defensive.
Last Area is developing cyber capability and technologies. One of the technologies is using Formal methods which are mathematical approaches to software and system development that support the rigorous specification, design and verification of computer systems.
DARPA has developed a unmanned drone with secure software using formal methods that protects the control and navigation functions of the aircraft from a systems hack. The software was developed under Defense Advanced Research Project Agency (DARPA)’s High Assurance Cyber Military Systems (HACMS) program whose goal is to demonstrate the feasibility of using formal verification to improve the software security for complex cyber-physical systems. They even gave it to a team of hackers for six weeks but they failed to crack it.
The formal methods consist of using formal specification as a way of defining what, exactly, a computer program does and formal verification as the way of proving beyond a doubt that a program’s code perfectly achieves that specification. A team of Yale researchers has unveiled CertiKOS, the world’s first operating system that runs on multi-core processors and shields against cyber attacks. DARPA intends to use these tools to construct high-assurance military vehicles.
The insider threat has posed significant challenges to US DOD from millions of documents unearthed by former contractor Edward Snowden to recent breach where sensitive personal data of tens of millions of federal employees has been lifted that not only puts individuals at risk. Organizations and Intelligence agencies are now using User Behavior Analytics or UBA to detect when legitimate user accounts/identities have been compromised by external attackers or are being abused by insiders for malicious purposes.
The idea behind UBA is that there’s no way to know which users or machines are good or bad. So you assume they’re all bad, that your network has been compromised, and you constantly monitor and model everything’s behavior to find the bad actors. UBA focuses on what the user is doing: apps launched, network activity, and, most critically files accessed (when the file or email was touched, who touched it, what was done with it and how frequently). DARPA, earlier had launched a program known as Cyber Insider Threat (CINDER) that proposed to monitor the “keystrokes, mouse movements, and visual cues” of insider threats.
Variety of supervised and unsupervised machine learning algorithms are used to detect anomalous patterns of user behavior, as gleaned from a variety of sources, like server logs, Active Directory entries, and virtual private networking (VPN) logs. UBA then uses big data and machine learning algorithms to assess the risk, in near-real time, of user activity. While UBA won’t prevent hackers or insiders from getting into your system, it can quickly spot their work and minimize damage.
Cybersecurity solutions have traditionally been based on signatures, relying on matches to patterns identified with previously identified malware to capture attacks in real time. Intrusion Prevention System (IPS) and Next-generation Firewall (NGFW) perimeter security solutions inspect network traffic for matches with a signature that has been created in response to analysis of specific malware samples. However, Minor changes to malware reduce the IPS and NGFW efficacy.
Another important element is development of National Scale Cyber War Test Range to test and validate strategies, tactics, inter-operability, functionality and performance of solutions.
Space Security
The space is increasing becoming another domain of conflict due to enhanced militarization along with proliferation of counter space weapons like electronic warfare, anti-satellite weapons, and DEW weapons. The space security of our ever-expanding space assets from either attack or interference has become essential. So under broader concept of information dominance the goal of offensive counter space weapons, is to delay or deny an enemy’s capability to collect, process, and disseminate information by disrupting or destroying, as required, the enemy’s space systems.
Our space security strategy should consist of four important elements: first is developing full range of military space capability like complementing our excellent imagery intelligence (photo and synthetic aperture radar), with signals intelligence (COMINT, ELINT) satellite constellations, early warning for Ballistic Missile Defence, data relay satellites, Microsatellites constellations. Launch on demand.
One of space capability gaps is that we lack capability to detect ASAT launches, like Chinese 2007, ASAT weapon test, when it deliberately hit and destroyed its own aging weather satellites at an altitude of 865 kilometers. India did not have any direct independent assessment of the Chinese test. It had to depend on the delayed US information for it to know that such a test had indeed occurred. Again on May 13, 2013, China reportedly tested ASAT again that reached more than 10,000 kilometers in altitude; still we don’t know what is happening.
Space situational awareness (SSA) is the foundational element of space security, National SSA Programmes should be launched to provide dependable, accurate and timely data regarding space situation (Space debris, Artificial Space objects, Space environment and NEOs) as well as Threat Warning and Assessment for threats like ASATs, Directed energy weapons, and HAND.
Comprehensive SSA requires a networked system of radars and electro-optical sensors. Recently the trend is to use space based sensors to provide timely detection, collection, identification and tracking of man-made space objects from deep space to LEO orbits. These shall be complemented by space- and ground-based space weather sensors monitoring the electromagnetic and sub-atomic particle fluxes incident on the Earth. Our space capabilities are also critically affected by Space Weather and need to be protected in severely degraded space environment due of natural and man-made space weather degradations like HAND events.
The third element is space protection. The numerous threats to our space assets demand that we develop new architectures say in MEOs which are less vulnerable to threats. For example, the U.S. Air Force placed two Space Based Infrared System (SBIRS) satellites in highly-elliptical orbits that are more challenging for China to target because of their high orbital speeds as they approach their perigee. Satellite Clusters or satellite constellation consisting of networked microsatellites in multiple orbits can provide Robust, fault tolerant, flexible and scalable formation architectures for distributed spacecraft communication, control, and sensing. This require development of
A Formation Flying Control System which highly autonomous and which optimize the performance of the cluster by cluster reconfiguration based on mission life span, collision avoidance, and mission related requirements such as resolution, observation time, and satellite failures and subsequent performance is desirable. Of course, the final element is development of space deterrent and we have to develop satellite jammers, directed energy weapons, and ASAT capability. The India can also plan to strike ground node
On-orbit Satellite Servicing
Building and launching Satellites are costly business. Any fault could lead to making hundreds of crores satellite useless and must be replaced, which is both difficult and extremely expensive. We just heard how ISRO is working overtime to restore the communication link with its GSAT-6A satellite “which is still alive” according to ISRO Chairman K Sivan.
A new emerging technology is Space Robotics that shall enable in space satellite repair and upgrade and in future in space spacecraft assembly and building. Orbital ATK has developed first “mission extension vehicle,” (MEV) that would dock with the similarly-sized Intelsat-901 in 2019, extending its life for five years. Another player is Maxar Technologies’ SSL division, is also developing space robotic servicing vehicles with highly capable robotics and end effectors for NASA and for the Defense Advanced Research Projects Agency.
NASA is developing robotic satellites, known as “service stations in orbit,” that would not only refuel satellites, they could drastically improve their longevity and lifespan. The robots could fix minor maintenance issues, keeping up with current orbiters as they age and sustain damage. In-space-assembly is also critical to enhance space security. All these capabilities to refuel, service and assemble satellites on orbit can extend operational life and repairing or refurbishing systems in response to system degradation due to ASATs. Furthermore, these automated agents shall enhance operational performance as they shall be able to integrate new technologies into satellites like improved sensors or countermeasures against adversary’s space weapons. They could also expand or reconfigure capability to meet user or mission needs.
However, this technology is also dual use, the same automated agents which are designed to repair owns satellites can also be used to degrade or destroy adversary’s satellites. They could be weaponized with lasers or explosives. The satellites are very vulnerable by their construction. This is leading to new race among leading space nations to develop similar satellites which could function as killer Robotic microsatellites. This is also another example of robotization of warfare. We had developed ground, air and water based unmanned systems and now we have moved to space. DARPA is having even more ambitious plan to design, assemble and build satellites in space to replace satellites due to space weapons.
Near Space Domain
After space we can consider another emerging domain of warfare that is Near space. Aerospace companies including Facebook, Boeing and Google planning solar-powered plane that can fly at high altitudes for years at a time, and can provide broadband communication services. Near space, which begins at about 20km above sea level, has until now been regarded a “death zone” for drones – thin air at this altitude makes it hard to generate lift, while extremely low temperatures mean electronic components like batteries are prone to fail. Until now, the Northrop Grumman RQ-4 Global Hawk, limited to an altitude of about 19km, has been the highest-flying drone in use.
The altitude range adopted for HAP operation, around 20 km, is motivated by the facts that in these altitudes the wind speed is less intense and, consequently, the HAP requires less power to maintain position. The altitude next to 20 km also has the advantage of being positioned above the strong wind currents (jet stream) existing between 10 and 15 km. Other important advantages are a large coverage area for telecommunications and be situated above normal commercial airline traffic. The maximum altitude for controlled airspace varies from country to country, 20 km (65,000 ft) being a typical value, set at the time of Concorde commercial supersonic jet operation
Military is also turning to solar powered stratospheric drones for persistent, wide area, real time Intelligence, Surveillance, and Reconnaissance (ISR) and communications. Military has been employing various platforms like Balloons, Aerostats, Airships, and UAVs for satisfying the requirement for persistent, real time and wide area coverage of battle space. The helium powered Airships have safety issues, while satellites have been expensive to launch. Airbus is building unmanned “Zephyrs” that flying at heights of about 70,000 feet at speeds of 20mph will be used to demonstrate technology that could ultimately see the British military fielding reconnaissance aircraft that could monitor targets for months at a time.
Zephyr is a High-Altitude Pseudo Satellite (HAPS) UAV running exclusively on solar power. The UAV has all the advantages of an aircraft and satellite combined: it can be re-used and has a wide coverage due to its flexibility in location. At the same time it’s capable of taking on similar tasks as satellites: it can fly at high altitudes, perform similar applications and is reliable. The Zephyr already holds the record for the longest unmanned flight, staying aloft for 14 days in tests at a secret location in the Southern hemisphere. Flying at 20km altitude at a fixed location, Zephyr can see over 400km to the horizon and provide persistent high-resolution imagery and high bandwidth communications to areas in excess of 1,000km2. Britain’s Ministry of Defense (MoD) will acquire three solar-powered drones, the drone’s manufacturer said.
On October 13, 2015, China started the 24 hour test flight of its largest airship yet in Xilinhot, Inner Mongolia. The Yuanmeng has a volume of 18,000 cubic meters, a length of 75 meters and a height of 22 meters. Yuanmeng will be one of the largest solar-powered airships in existence. Using solar power to drive its rotors will save additional weight in order to increase payload, and gives it a total flight endurance of six months. The Yuanmeng’s 5- to 7-ton payload of data relays, datalinks, cameras and other sensors would also be powered by the sun
The Yuanmeng aircraft can reach a height of 100 kilometers and conduct reconnaissance without being seen by other aircraft or rockets. The ship will operate at altitudes inaccessible to the majority of air defense systems. Like its smaller American counterpart, the JLENS (currently parked outside Washington DC), the Yuanmeng can use its sensors and high altitude to detect threats such as stealth aircraft, cruise missiles, missile launchers, and warships from several hundred miles away. But the Yuanmeng has other advantages over the JLENS. While the JLENS is an aerostat, anchored to one location by a 3,000m long tether, the Yuanmeng can freely move about and be redeployed. Its high flight altitude also gives the Yuanmeng’s sensors superior situational awareness, and the ability to act as a communication rely to Chinese aircraft and drones in the event of a loss in satellite communications.
These large dimensions lead to very severe optimization requirements of HAPs structural weight. In the case of airships and balloons, the envelope material must have low weight characteristics, high strength, high ability to withstand damage (tear, pin holes), low permeability to lifting gas, maintain flexibility at low temperature and low degradation with UV radiation and ozone. The most commonly adopted solution for very long endurance HAP is, during the day, the solar energy converted into electricity by means of photovoltaic cells (solar cells), and part of this electricity is used to charge a storage system, usually rechargeable batteries or RFC for later use at night In Japan, research for the SPF airship defined as a target for the RFC system achieving a specific energy of 450 Wh/kg. The current systems have 350 Wh/kg of specific energy
In the definition of HAP equipment, it should be considered that the environment in the stratosphere has aspects similar to the space, such as very low temperatures, marked temperature cycles (day/night) and intense solar radiation and UV (Keck Institute for Space Studies 2014) Another important technology that is weaponizing this near space domain are Hypersonic weapons and platforms. NASA categorizes speeds between Mach 5 (6125 kilometers per hour) to 10 Machs as Hypersonic.
 International Defense Security & Technology Your trusted Source for News, Research and Analysis
International Defense Security & Technology Your trusted Source for News, Research and Analysis