The traditional, not so secure way to log in to your bank account: enter your username and that familiar password you probably use for most of your online accounts. Then, you’re in. You can go about your business. If you’re one of the 54% of consumers who, according to TeleSign, use five or fewer passwords for all of their accounts, you could create a “domino effect” that allows hackers to take down multiple accounts just by cracking one password. There’s an easy way to better protect your accounts (which contain a lot of personal information) with multi-factor authentication (MFA).
Multi-factor authentication is an electronic authentication method in which a computer user is granted access to a website or application only after successfully presenting two or more pieces of evidence – your credentials – when logging in to an account.Two-factor authentication (also known as 2FA) is a type, or subset, of multi-factor authentication. Your credentials fall into any of these three categories: something you know (like a password or PIN), something you have (like a smart card), or something you are (like your fingerprint). Your credentials must come from two different categories to enhance security – so entering two different passwords would not be considered multi-factor.
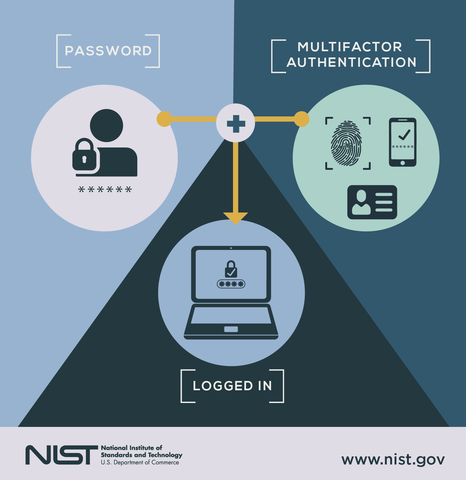
A third-party authenticator (TPA) app enables two-factor authentication, usually by showing a randomly-generated and constantly refreshing code which the user can use. So look at a simple scenario: logging in to your bank account. If you’ve turned on MFA or your bank turned it on for you, things will go a little differently. First and most typically, you’ll type in your username and password. Then, as a second factor, you’ll use an authenticator app, which will generate a one-time code that you enter on the next screen. Then you’re logged in – that’s it!
MFA helps protect you by adding an additional layer of security, making it harder for bad guys to log in as if they were you. Your information is safer because thieves would need to steal both your password and your phone. You would definitely notice if your phone went missing, so you’d report it before a thief could use it to log in. Plus, your phone should be locked, requiring a PIN or fingerprint to unlock, rendering it even less useful if someone wants to use your MFA credentials.
Using 2FA is one of the top three things that security experts do to protect their security online, according to recent Google survey. And consumers feel the same way: almost 9 in 10 (86%) say that using 2FA makes them feel like their online information is more secure, according to TeleSign.
You should use MFA whenever possible, especially when it comes to your most sensitive data—like your primary email, your financial accounts, and your health records. While some organizations require you to use MFA, many offer it as an extra option that you can enable—but you must take the initiative to turn it on. Furthermore, if a business you interact with regularly, say your health organization, wants to provide you with convenient online access to health records, test results, and invoices, but only offers a password as a way to protect that data, consider saying: ‘no thanks, not until you provide MFA to secure my information.’
Multifactor authentication in the Defense Department
A 2019 Defense Department IG audit found that the Army, Navy and Missile Defense Agency aren’t taking basic cybersecurity steps to protect networks and systems from unauthorized use and access. Some facilities even failed to use common access card, and single-factor authentication was a common practice. Additionally, a recent audit of the Navy’s stance on cyber readiness found that the organization does not have the resources it needs to detect and protect threats to its data.
The DoD needs to find a way to bolster authentication methods. Government agencies typically use two-factor authentication, sometimes referred to as multifactor authentication, to validate users. Generally, this comprises something you know (like a password) and something you have (like an ID badge or token). Two-factor authentication is a crucial starting point for security. However, even these techniques are too static in a threat landscape that is incredibly dynamic — and today’s technology can often support a stronger approach.
The Pentagon uses common access card (CAC) which is going to remain the principal authenticator for the DoD, and while it is solid, allowing users to access networks using single-factor authentication increases the potential for cyberattackers to exploit passwords and gain access to critical data. However, there are effective ways the DoD can tighten multifactor authentication and enhance their overall cyber posture.
However, there are effective ways the DoD can tighten multifactor authentication and enhance their overall cyber posture. Agency leaders first need to consider how to secure the identities of government workers and manage access among privileged users by putting tighter identity access management and security measures in place to enhance the CAC. While its assurance level is considered the gold standard of IT security, the CAC only utilizes two aspects of multifactor authentication — what you have and what you know. The third aspect, who you are, can strengthen the CAC. The DoD should look to emerging technologies to begin bolstering the traditional approach.
According DOD Chief Information Officer Dana Deasy, work on developing an up-to-date identity, credential and access management (ICAM) approach involving an authentication system based on cutting-edge biometrics like facial recognition, iris, and fingerprints, locational patterns, gait, speech, keystrokes, etc., is farther away down the road. The goal of ICAM is to “know who is on the network at any given time,” and to build a “secure, trusted environment where any of our users can access all of the authorized resources, including applications and valuable data,” Deasy said.
“So we have this conversation, but I always tell people you can’t have it at any one point,” he said. “You have to discuss the entire ecosystem of cybersecurity.” Nevertheless, he stated, existing ICAM innovation “will revolutionize how we create digital identities and any maintenance of associated attributes, including both people and non-person entities. ICAM creates a secure, trusted environment where any of our users can access all of the authorized resources, including applications and of course our valuable data, to have a successful mission. It will also let us know who is on the network at any time.”
LastPass Recognized for Authentication Technology Innovation with 2020 CyberSecurity Breakthrough Award
LastPass MFA has been named the winner of the “Multifactor Solution of the Year” award in the fourth annual CyberSecurity Breakthrough Awards program. The CyberSecurity Breakthrough Awards honor excellence and recognize the innovation, hard work and success in a range of information security categories, including Cloud Security, Threat Detection, Risk Management, Fraud Prevention, Mobile Security, Email Security and many more.
LastPass MFA goes beyond the standard two-factor authentication (2FA), ensuring only the right users are accessing the right data, at the right time while minimizing complexity. Through biometric factors, like face and fingerprint ID, coupled with contextual factors, such as geolocation and IP address, LastPass MFA offers an intuitive authentication experience that’s seamless for employees to use and easy for admins to deploy across cloud, legacy and on-premise apps, as well as VPN. LastPass MFA offers a host of features that deliver the control IT managers need and the convenience users expect.
In light of today’s increasingly remote workforce, every employee logging in to the network is outside of the traditional corporate perimeter, and authentication technologies that help IT verify that the user logging in is legitimate, is critically important. With a step-by-step guide for a seamless deployment, and no additional training or services required, IT teams can easily roll out LastPass MFA to their entire organization.
References and Resources also include:
 International Defense Security & Technology Your trusted Source for News, Research and Analysis
International Defense Security & Technology Your trusted Source for News, Research and Analysis