The exponential price/performance improvements in semiconductor technology stemming from Moore’s Law are enabling even the smallest and most application-specific devices, such as sensors and actuators, to include networking capabilities. The overwhelming majority of such devices will be cheap and power-constrained. Low device costs permit deployment in unprecedented numbers, with some estimates as high as a trillion devices, which for CHARIOT we call “hyper-scale.” Support for communication amongst such devices in, or using, 5G wireless networks makes them “hyper-connected” and collectively they form what is called an Internet of Things (IoT).
The rapid growth in IOT devices, however will offer new opportunities for hacking, identity theft, disruption, and other malicious activities affecting the people, infrastructures and economy. Some incidents have already happened, FDA issued an alert about a connected hospital medicine pump that could be compromised and have its dosage changed. Jeep Cherokee was sensationally remote-controlled by hackers in 2015. The implementation of IoT in military domain shall also make military systems and networks vulnerable to cyber and other attacks from adversaries, hackers, and terrorists. There is threat of unauthorized monitoring or even seizure and control of vital networks critical to military operations.
Revolutionary security technologies are needed for IoT devices. Cryptography is an important part of how the internet keeps secret information (such as your credit card number) hidden from potential thieves.
The emergence of public-key cryptography, such as the RSA (Rivest-Shamir-Adleman) scheme predicated on the hardness of factoring, used number-theoretic concepts to derive protocols for confidential communications, identity verification with digital signatures, message integrity checking with secure hashing, etc. A logistical challenge arises, however, as these protocols presume the legitimacy of the public key used. While no universal public key infrastructure (PKI) exists, legitimacy is now “certified” using a sequence of digital signatures starting from a trusted authority such as the Department of Defense.
A 10+ year deployment lifetime is expected for some types of IoT devices. Today, energy (such as battery power) consumed by cryptographic operations reduces deployment lifetimes, discouraging manufacturers from including security.
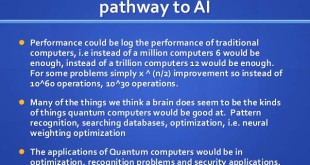
By harnessing quantum super-positioning to represent multiple states simultaneously, quantum-based computers promise exponential leaps in performance over today’s traditional computers. Quantum computers shall bring power of massive parallel computing i.e. equivalent of supercomputer to a single chip. Quantum algorithms can break current security by reverse computing private keys may only take days or hours. For example, Shor’s algorithm, which uses quantum computing to accelerate factoring, undermines the security model of RSA-based cryptography.
Organizations are now working on post-quantum cryptography (also called quantum-resistant cryptography), whose aim is to develop cryptographic systems that are secure against both quantum and classical computers, and can interoperate with existing communications protocols and networks. NSA, whose mission is to protect vital US national security information and systems from theft or damage, is also advising US agencies and businesses to prepare for a time in the not too-distant future when the cryptography protecting virtually all e-mail, medical and financial records, and online transactions is rendered obsolete by quantum computing.
The official impetus for Project CHARIOT was lifted right off a report published by The National Institute of Standards and Technology (NIST) in 2016; itself preceded by a 2015 announcement by the National Security Agency (NSA) to begin the “transition” into quantum-resistant encryption algorithms. NIST’s Post-Quantum Crypto (PQC) report studied the impact of quantum computing algorithms on existing encryption schemes and mirrors many of the goals and milestones specified by DARPA in Project CHARIOT. Among these is the 10-year deadline and the need for the development of “revolutionary security technologies.” Dustin Moody, NIST mathematician and PQC co-author, warned that the U.S. must be “prepared to transition to new algorithms in 10 years” in a presentation at the 2017 Asiacrypt cryptography conference in Hong Kong.
Quantum computing may appear before today’s deployments end. CHARIOT’s objective is solutions that are fast, efficient, and quantum-resistant on even the cheapest devices. DARPA’s newest program seeks to create an encryption technology standard across the breadth and scope of the Internet of Things (IoT). The Cryptography for Hyper-scale Architectures in aa Robust Internet Of Things or Project CHARIOT “will prototype low-cost, low-footprint, post-quantum cryptographic techniques with minimal energy use for devices in an IoT” on the 5G network, according to the Pentagon’s boutique agency’s SBO.
CHARIOT Program
CHARIOT will prototype low-cost, low-footprint, post-quantum cryptographic techniques with minimal energy use for devices in an IoT. Technical requirements should have their genesis in expected use cases. Vehicle-embedded and wearable uses with a zero-trust networking architecture are of particular interest, e.g., uses within a larger scenario of wearable-equipped passengers entering, traveling in and departing from a vehicle such as a troop carrier or school bus.
Phase I
Phase I feasibility will be demonstrated through evidence of: completed evaluations of security risks and vulnerabilities of existing IoT devices; definition and characterization of post-quantum security core competencies and attributes (i.e., the properties desirable for both DoD and civilian use); and comparisons with alternative state-of-the-art methodologies (competing approaches).
Phase II
The goals of the Direct to Phase II (or DP2) (24 months in duration) are to develop a compelling technology consistent with the CHARIOT goals to develop revolutionary approaches for fast, efficient, and quantum-resistant cryptographic operations for IoT devices. DP2 proposals should:
(1) describe a proposed design/architecture to achieve these goals, along with application programming interfaces that allow for a secure IoT ecosystem (e.g., one based on zerotrust principles);
(2) present a plan for maturation of the architecture to a prototype system to demonstrate confidential communications, message integrity, group membership, and scalable key management; and,
(3) detail a test plan, complete with proposed metrics and scope (e.g., network structure, types/numbers of devices, etc.), for verification and validation of the system cryptography.
Phase II will culminate in a system demonstration using one or more compelling IoT use cases consistent with commercial opportunities and/or insertion into the DARPA/I2O Open Programmable Secure 5G (OPS-5G) program.
Dual Use Applications (Phase III)
The Phase III work will be oriented towards transition and commercialization of the developed security technology. The proposer is required to obtain funding from either the private sector, a non-SBIR Government source, or both, to develop the prototype software into a viable product or non-R&D service for sale in military or private sector markets. Phase III refers to work that derives from, extends, or completes an effort made under prior SBIR funding agreements, but is funded by sources other than the SBIR Program.
Primary CHARIOT support will be to national efforts to develop approaches to protect network infrastructure and technologies (e.g., 5G). Outcomes have the potential to significantly benefit the DoD and numerous commercial entities by providing protected and resilient capabilities. Specifically, in the commercial space, CHARIOT security technologies have applications to companies that develop digital entities (e.g., networks, clouds, devices participating in the IoT, etc.); in the DoD space, CHARIOT security technologies have value to all Service Components due to the widespread use and migration to such digital entities to support mission operations.
 International Defense Security & Technology Your trusted Source for News, Research and Analysis
International Defense Security & Technology Your trusted Source for News, Research and Analysis