A Content Delivery Network (CDN) is a globally distributed network of web servers or Points of Presence (PoP) whose purpose is to provide faster content delivery. The content is replicated and stored throughout the CDN so the user can access the data that is stored at a location that is …
Read More »High Frequency Surface Wave Radars (HFSWR) for Ship detection and tracking far beyond the horizon
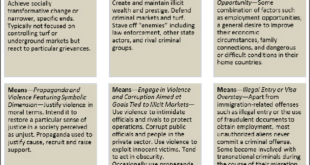
In recent years organized crime in maritime regions has flourished, threatening both secure flow of goods from Exclusive Economic Zones (EEZ) and lives of participants in the marine operations. Security threats and humanitarian risks caused by trafficking (drugs, weapons, etc.), irregular transport of migrants, maritime terrorism or even piracy are …
Read More »Countries advance Border management Strategy and technology to counter terrorists, and criminals, smuggling weapons, and illegal drugs, and counterfeit goods
In an increasingly globalised and interconnected world it has become simple for people and goods to cross borders and so for terrorists. America’s borders and ports are busy places, with tens of millions of cargo containers and hundreds of millions of lawful travelers entering the country each year, while tens …
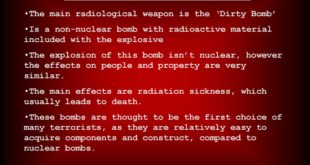
Read More »Threat of Radiological warfare, Radiological weapons and Dirty Bombs
The threats of chemical, biological, radiological, nuclear and explosive (CBRNE) hazards continue to advance. CBRN weapons are some of the most indiscriminate and deadly weapons in existence today, with capability to affect large population in wide geographical area and in short time. The release of Chemical, Biological, Radiological and Nuclear …
Read More »Compact Electronic noses can monitor air quality, diagnoze diseases to biohazards like covid-19, explosives and nerve gas
Government and local law enforcement agencies have employed canines for decades to sniff explosives and such banned goods as fresh produce, exotic wildlife, undeclared currency and illicit drugs. Now researchers are developing electronic noses imitating the sense of smell of humans and animals especially dogs. The smells are composed of molecules, …
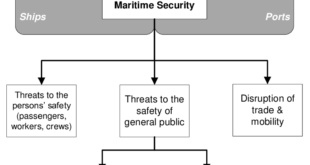
Read More »Rising Maritime threats require Smart Ports, Ship security and safety technologies to improve security and stability of maritime domain
The oceans are vital to the overall growth of the world economy and population, and to the continued economic integration of nations. The oceans are a primary source of food, energy, and transportation, all key requirements of human activity in an interconnected world. They are also essential to meet the …
Read More »Drones that can Autonomously launch and Land from a moving platform are new requirements for Defense and Security
An unmanned aerial vehicle (UAV) ( commonly known as a drone) is an aircraft without a human pilot on board. UAVs are a component of an unmanned aircraft system (UAS); which include a UAV, a ground-based controller, and a system of communications between the two. The flight of UAVs may …
Read More »Fire safety of High-rise buildings several unique challenges require new solutions and technologies
The World Trade Center events of September 11, 2001, focused the world’s attention on high-rise buildings. Since that time, there have been several other events that have kept the world’s attention on high-rise building fire safety, including fires in Madrid, Venezuela, and two in Chicago. The two deadliest high-rise fires …
Read More »France thrust on counter terrorism initiatives after glaring security gaps exposed by brazen attacks
France suffered a series of deadly terror attacks in November 2015. In 2015, the brazen murders of 17 innocent people, in three separate attacks in as many days, have revealed serious breaches and lapses in the French system of intelligence, surveillance and security, according to numerous counterterrorism experts. In July …
Read More »Changing role of Military Scientific and Technical Intelligence ( S&TI)
If the Militaries are to fight and win in future wars, it must thoroughly understand the challenges that it will face and how those challenges will impact the way it intends to fight. It must act now to ensure that it possesses a technological edge over its adversaries. This is …
Read More » International Defense Security & Technology Your trusted Source for News, Research and Analysis
International Defense Security & Technology Your trusted Source for News, Research and Analysis