Digital battlefields, hybrid warfare, and the future of threat intelligence
IDST Intelligence Briefings
(Latest Security & Cyber Videos)
Why This Magazine Exists
Security, Cyber & Counter-Threats examines the evolving landscape of modern security in an era defined by digital conflict, hybrid warfare, and persistent global threats.
From cyber operations, information warfare, and intelligence-driven defense to counter-terrorism, internal security, and emerging threat vectors, this magazine provides strategic analysis, technical insight, and policy-relevant perspectives for decision-makers, practitioners, and researchers navigating an increasingly contested security environment.
What We Track
- Cyber warfare & cyber defense
- Information operations & influence campaigns
- National security threat assessments
- Emerging digital and hybrid warfare doctrines
- Critical infrastructure & cyber resilience
Latest Analysis & Intelligence
-
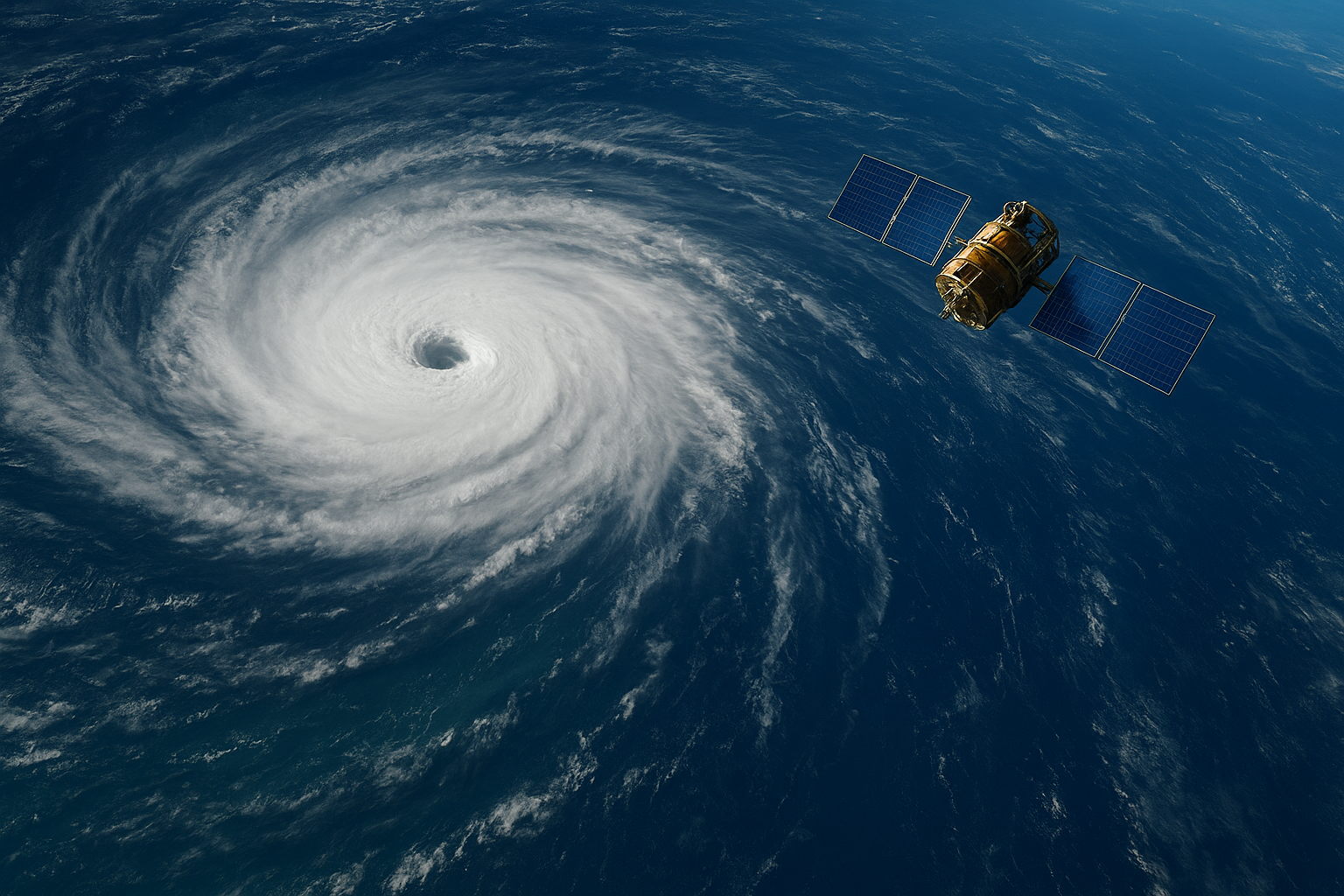
The Hurricane’s Whisper: How Advanced Satellites Decode Ocean Winds to Save Lives
In the vast, sun-drenched expanse of the tropical ocean, a hurricane is born. It begins as a whisper of convection — a cluster of thunderstorms that starts to spin, feeding on the warm, moist air below. For forecasters at the National Hurricane Center, the most agonizing question in these early hours is not just where…
-
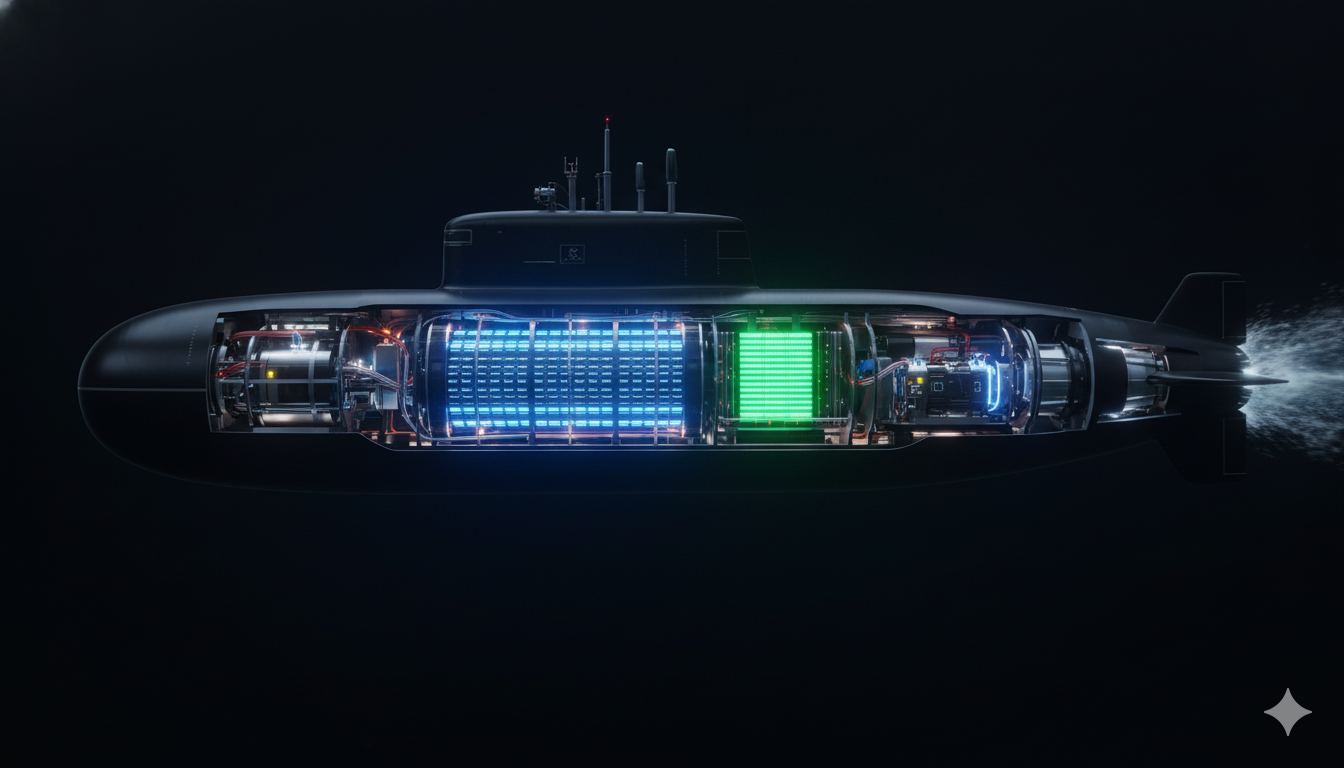
Silent Endurance: The Future of Submarine Power and Propulsion
For more than a century, the deep hum of a submarine powered by lead-acid batteries represented the heartbeat of stealth beneath the waves. Yet this technology, though proven, has reached its practical limits. Heavy, slow to recharge, and constrained in power density, it no longer satisfies the operational demands of 21st-century undersea warfare. Today, a…
-

Beyond Solid and Liquid: How Phase Change Materials are Reshaping Technology
Imagine a material that can absorb excess heat without increasing in temperature, release stored warmth on demand, and store vast amounts of energy in a compact space—all simply by changing its physical state. This is not science fiction; it is the reality of Phase Change Materials (PCMs), substances that are rapidly moving from laboratory curiosity…
-

Quantum-Shielded Networks: The Future of IoT Security in a Connected World
Introduction: The IoT Security Paradox In September 2024, the cybersecurity world was shaken when thousands of pagers and walkie-talkies used by Hezbollah operatives were remotely detonated in a sophisticated cyber-physical attack. Beyond the immediate tactical implications, the incident served as a stark reminder of the fragility inherent in our increasingly connected world. With projections estimating…
-

Water as a Strategic Factor: Harnessing Technology to Predict and Manage Global Water Risks
Water is no longer just an environmental concern; it has emerged as a critical strategic resource whose availability and predictability shape outcomes across military, humanitarian, urban, and industrial domains. Accelerating climate change is intensifying floods, prolonging droughts, and destabilizing ecosystems across large parts of the world. As environmental volatility increases, the ability to monitor and…
-

Mapping the Invisible Battlefield: How Spectrum Analysis is Revolutionizing Modern Warfare
Mapping the Invisible Battlefield: How Spectrum Analysis is Revolutionizing Modern Warfare In contemporary warfare, the battlefield extends far beyond land, sea, air, and space. Increasingly, a decisive domain of conflict exists within the electromagnetic spectrum—the invisible environment that carries communications, radar signals, navigation systems, and electronic warfare capabilities. Modern militaries now recognize that controlling and…
-
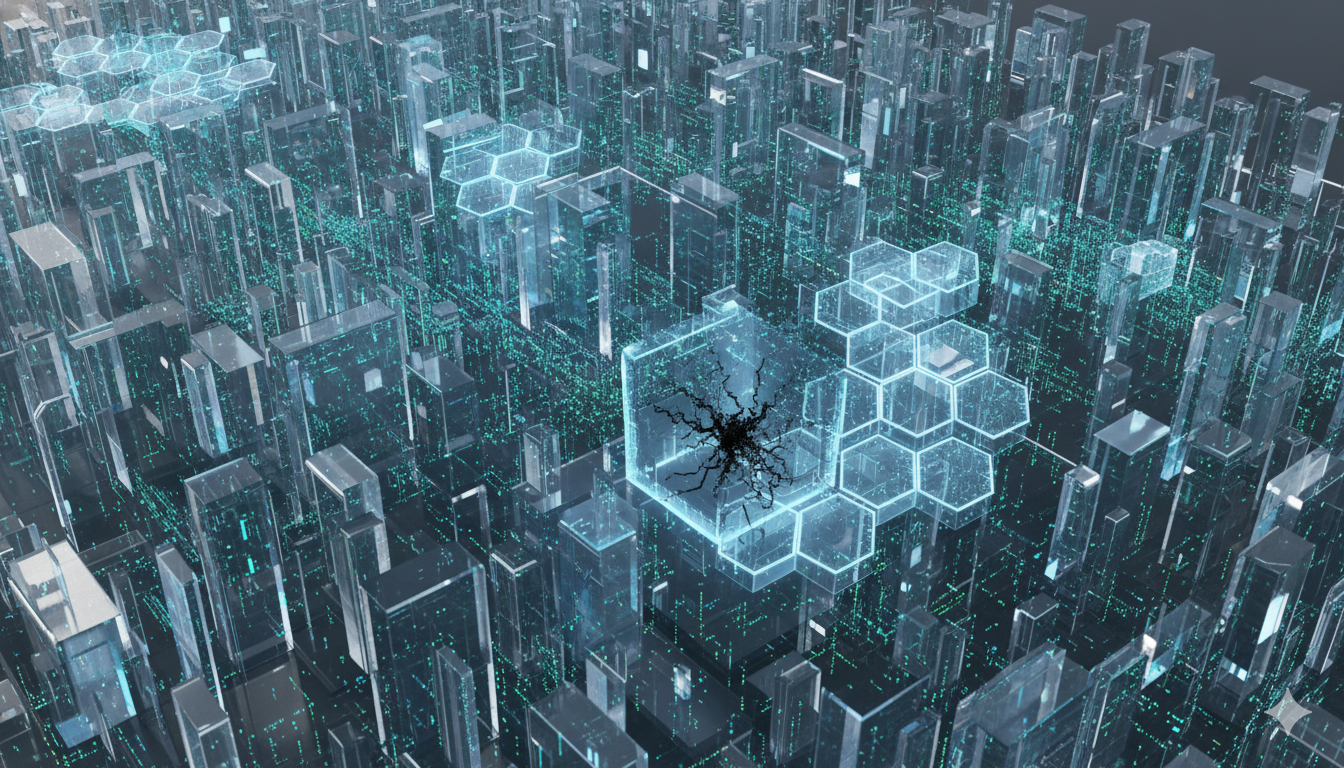
Digital Fortresses: How DARPA’s CPM Program is Reinventing Cybersecurity Through Automatic Compartmentalization
In the relentless cat-and-mouse contest between cyber attackers and defenders, a fundamental asymmetry has long shaped the battlefield. An attacker needs to discover only a single vulnerability to gain entry into a system, while defenders must secure every possible entry point. This imbalance has produced a steady stream of major cyber incidents that have disrupted…
STRATEGIC SUB-MAGAZINES
Modern military power emerges from the interaction of platforms, people, doctrine, and integration across domains. The Defense & Military Systems magazine is structured into focused sub-magazines that examine how combat capability is built, sustained, and employed across air, land, sea, weapons, and human systems.
Cyber & Information Warfare
Industrial outcomes are shaped as much by incentives, policy, and market structure as by engineering. Price signals, investment cycles, and regulatory frameworks quietly determine which technologies scale, stagnate, or fail.
This sub-magazine examines how markets behave under strategic pressure—where capital flows, how demand signals distort decisions, and why some industries adapt faster than others.
Explore the Cyber & Information Warfare Sub-Magazine →
Security & Threat Management
Modern security is defined by persistence, coordination, and anticipation. This sub-magazine focuses on how threats are identified, mitigated, and managed across institutions, infrastructures, and societies.
Explore the Security & Threat Management Sub-Magazine →
