Cyberattacks are being conducted daily on any type of target, and any notion that a state of full cyber security can be reached is a mere illusion. Cybersecurity is about managing risks and to ascertain that, to a certain extent, proper procedures and adequate security measures are being taken. Exposed to constant cyber threats, military organisations rely on a vast number of communication and information systems. As global investment in cyber security grows, many businesses have come to recognise the value of regularly assessing the effectiveness of their cyber security to stand up to the latest advanced threats.
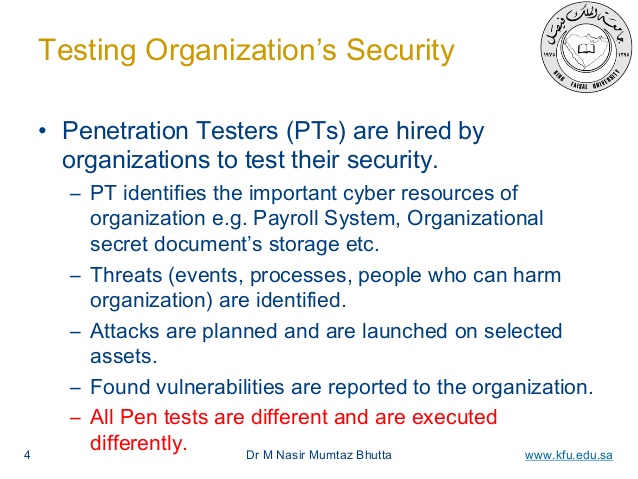
To improve the level of security, an arsenal of solutions has been created and this includes vulnerability assessments. Vulnerability assessments are an integral part of cybersecurity and can take a number of forms that range from security audits to penetration testing. According to the United States National Institute of Standards and Technology, pentesting ‘…is security testing in which assessors mimic real-world attacks to identify methods for circumventing the security features of an application, system, or network. It often involves launching real attacks on real systems and data that use tools and techniques commonly used by attackers. Most penetration tests involve looking for combinations of vulnerabilities on one or more systems that can be used to gain more access than could be achieved through a single vulnerability
A red team or the red team is an independent group that challenges an organization to improve its effectiveness by assuming an adversarial role or point of view. A red team operation is a simulated cyber-attack that rigorously tests an organisation’s ability to detect and respond to breaches. Mirroring the covert tactics and methodologies of real-life attackers, red teaming can highlight critical exposures within IT infrastructure, applications, personnel and processes as well as recommend remedial actions to address any identified weaknesses.
Cyber red teams (CRT) – commonly performing penetration testing – focus on threats from adversaries in the cyber world. They mimic the mind-set and actions of the attacker in order to improve the security of one’s own organisation. As a standing capability in a military environment, these tools can be used in order to enhance preparedness and improve training capacities. Red teaming is the work performed by the red team in identifying and assessing, inter alia, assumptions, alternative options, vulnerabilities, limitations and risks for that organisation.
A red team engagement differs from penetration testing in a number of key ways. Whereas a penetration test is commissioned to identify as many vulnerabilities as possible within a short timeframe and widely present findings to stakeholders, the goal of a red team operation is to covertly test an organisation’s detection and response capabilities over weeks and months, often without the knowledge of all in-house personnel.
Red teaming in cyberspace is not a new phenomenon. Exercise Eligible Receiver , conducted in 1997, was a prominent example of a high-scale exercise led by an NSA red team that consisted of attacks on critical infrastructure networks, particularly energy providers and Command and Control capabilities.
Today cyber red teams are often to be found in exercises and training sessions, as outlined by the US DoD. The main purpose is to test the blue teams that are supposed to defend the networks rather than to focus on vulnerability assessments. Cyber red teaming is a technical endeavour and will mostly rely on high-level specialists with a wide range of skill-sets. It can be conducted either from an internal dedicated organised element, or outsourced to specialised contractors.
Cyber red teaming can be carried out both by operational and simulated (cyber ranges) environments. Cyber ranges will allow an organisation to evaluate and test certain offensive solutions in a harmless environment). Ready-to-use solutions might have unforeseeable consequences that can cause damage and harm, especially when tested on a “live” environment.