Phones and other GPS-enabled devices pinpoint your location on Earth by contacting at least four satellites bearing atomic clocks. Each of these satellites provides a time stamp, and the system calculates your location based on the relative differences among those times. The accuracy of GPS Navigation is primary degraded due …
Read More »Monthly Archives: August 2022
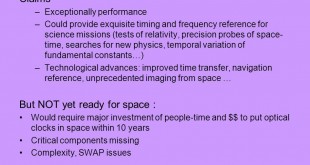
DARPA ROCkN optical atomic clocks will enable multidomain synchronization among various platforms, multi vehicle swarms
Synchronizing modern electronic systems such as the Internet and GPS navigation is currently done using microwave atomic clocks that measure time based on the frequency of natural vibrations of cesium atoms. Those vibrations occur at microwave frequencies that can easily be used in electronic systems. Optical atomic clocks will …
Read More »Russia’s DARPA, the Advanced Research Foundation aims breakthrough high-risk research and development
Emerging technologies such as space technology; 5G, Cloud computing, IoT, “big data” analytics, artificial intelligence, robotics, photonics, materials, nanotechnology; biotechnology; and quantum computing, have significant potential to create, significant social, economic, and military benefits. Therefore countries led by US, China and Russia are spending billions of dollars on them to gain …
Read More »Cloud-Network-Device Convergence
Cloud computing is the delivery of different services through the Internet. Companies that provide cloud services enable users to store files and applications on remote servers and then access all the data via the Internet. Cloud computing is a popular option for people and businesses for a number of reasons …
Read More » International Defense Security & Technology Your trusted Source for News, Research and Analysis
International Defense Security & Technology Your trusted Source for News, Research and Analysis