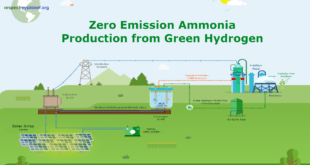
The challenges of our time are that the world’s population is growing more and more and fossil resources are running out. More people need more food and more energy. In order to protect the climate, we want to reduce the CO2 emissions. Researchers and Industry are focussing on sustainable technologies to …
Read More »Recent Posts
CubeSat cameras and optical payloads for Earth Observation small satellites
Constellations of satellites are being proposed in large numbers; most of them are expected to be in orbit within the next decade. They will provide communication to unserved and underserved communities, enable global monitoring of Earth and enhance space observation. In a Low Earth Orbit (LEO), a satellite completes about …
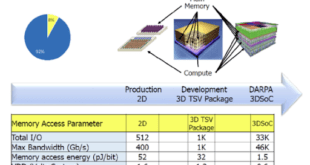
Read More »DARPA 3DSoC developed high performance 3D ICs based on CNT FET for future DOD computation systems
Deployed electronic systems increasingly require advanced processing capabilities, however the time and power required to access system memory – commonly referred to as the “memory bottleneck” – takes a significant toll on their performance. Any substantial improvement in electronic system performance will require a radical reduction in memory access time …
Read More » International Defense Security & Technology Your trusted Source for News, Research and Analysis
International Defense Security & Technology Your trusted Source for News, Research and Analysis