Digital battlefields, hybrid warfare, and the future of threat intelligence
IDST Intelligence Briefings
(Latest Security & Cyber Videos)
Why This Magazine Exists
Security, Cyber & Counter-Threats examines the evolving landscape of modern security in an era defined by digital conflict, hybrid warfare, and persistent global threats.
From cyber operations, information warfare, and intelligence-driven defense to counter-terrorism, internal security, and emerging threat vectors, this magazine provides strategic analysis, technical insight, and policy-relevant perspectives for decision-makers, practitioners, and researchers navigating an increasingly contested security environment.
What We Track
- Cyber warfare & cyber defense
- Information operations & influence campaigns
- National security threat assessments
- Emerging digital and hybrid warfare doctrines
- Critical infrastructure & cyber resilience
Latest Analysis & Intelligence
-

The Algorithmic Assault on Dirty Money: How AI Is Redrawing the Front Lines of Global Financial Defense
Introduction: The Algorithmic Battlespace of Illicit Finance In the contemporary global order, financial systems no longer function merely as economic infrastructure—they have become a primary domain of strategic competition. Capital flows now move at machine speed across jurisdictions, digital platforms, and regulatory boundaries, enabling unprecedented efficiency in legitimate commerce. Yet this same velocity has fundamentally…
-
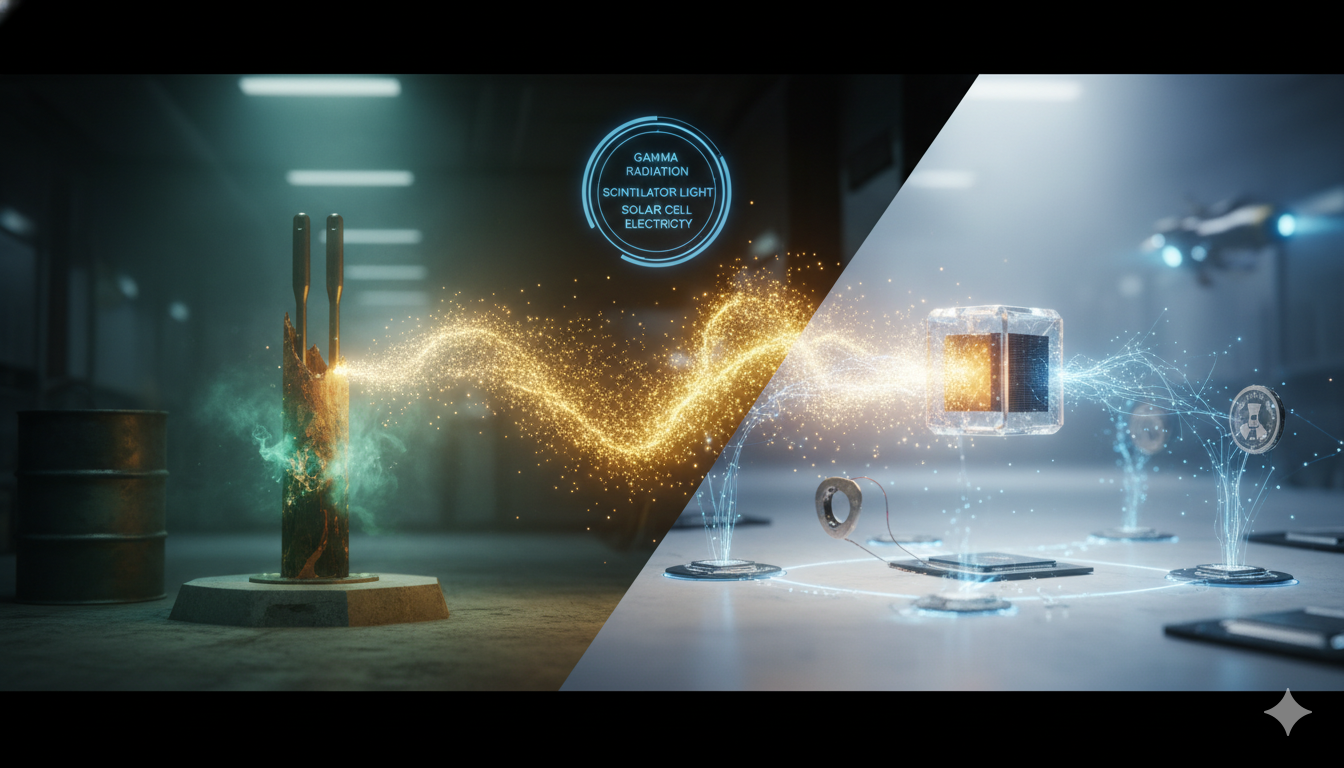
Harnessing the Power of Atomic Batteries: The Rise of Nuclear Micro-Energy Systems (2025–2026 Update)
Introduction: From Experimental Curiosity to Strategic Energy Technology The global energy transition is no longer driven solely by megawatt-scale renewable generation and grid modernization. Increasingly, strategic attention is shifting toward ultra-long-duration, maintenance-free micro-energy systems capable of operating for years—or even centuries—without recharge or replacement. In this context, atomic batteries, also known as nuclear batteries, radioisotope…
-
Perovskite Solar Cells: Closing the Gap Between Lab Breakthroughs and Commercial Reality (2025–2026 Update)
Introduction: From Scientific Curiosity to Strategic Energy Infrastructure Solar power is no longer viewed solely through the lens of climate policy. It has become a central pillar of geopolitical competition, industrial strategy, and technological sovereignty. In this rapidly evolving landscape, perovskite solar cells (PSCs) are emerging not merely as the next generation of photovoltaics, but…
-

Energy Tech Breakthroughs and Challenges: Navigating the 2026 Global Energy Transformation
Introduction: The Great Energy Realignment of the AI Era The global energy sector is entering one of the most consequential transformations since the industrial revolution. By 2026, the convergence of artificial intelligence, electrification, geopolitical fragmentation, climate policy, advanced materials, and digital infrastructure is fundamentally reshaping how energy is generated, transmitted, stored, and consumed. The transition…
-
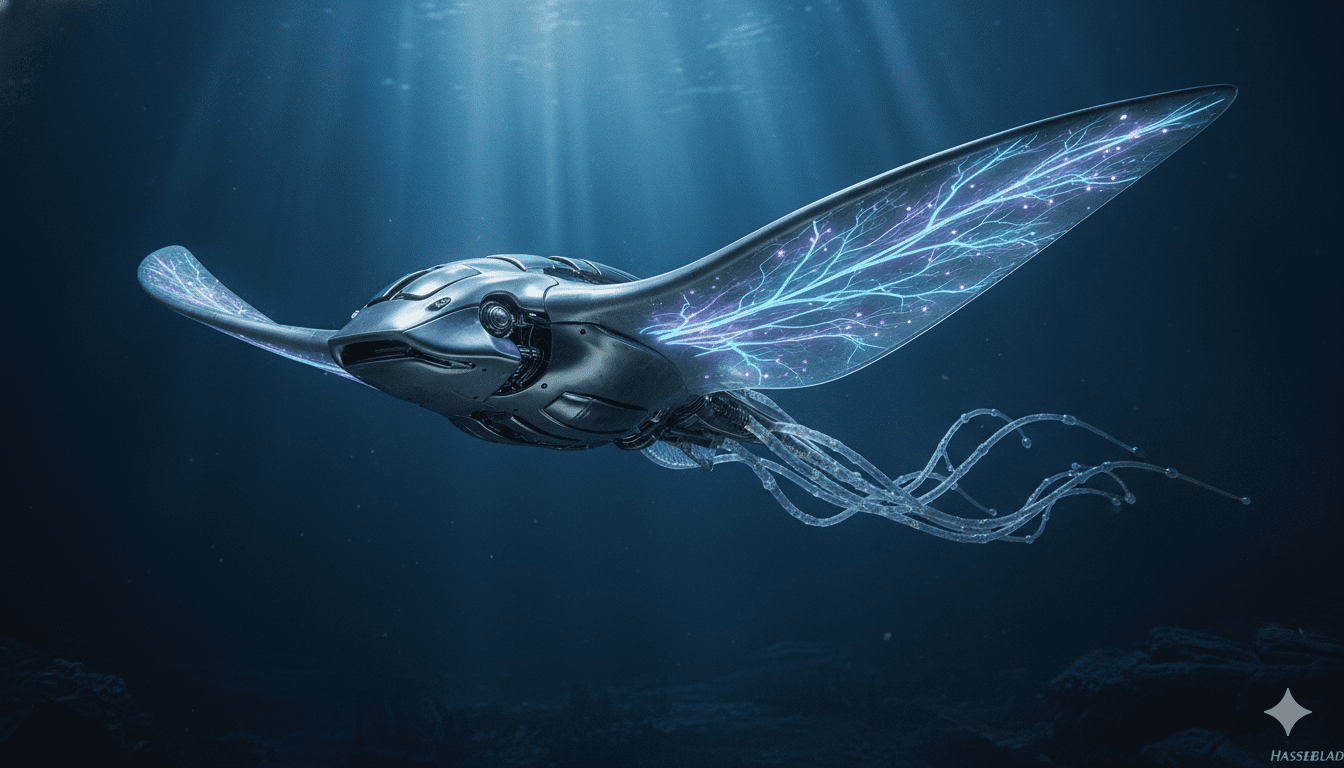
Beyond Metal: Biohybrid Robotics and the Strategic Reengineering of Machines
By IDST | Strategic Technology Analysis Introduction: Biohybrid Robotics and the Redefinition of Machine Capability In an era marked by systemic instability—where climate volatility, urban density, contested domains, and great-power competition are converging—the limitations of conventional robotics are becoming strategically visible. Autonomous systems are now deeply embedded across defense, infrastructure, and intelligence operations, yet their…
-

Beams of Light: Laser Communication and the Strategic Rewiring of the Global Internet
Introduction: Why Light-Based Connectivity Has Become Strategic Infrastructure In an era defined by systemic rivalry, infrastructure vulnerability, and the compression of decision-making timelines, the question of how information moves has become inseparable from the question of who holds power. The global internet—long perceived as a resilient, borderless system—is increasingly exposed as a layered construct dependent…
-
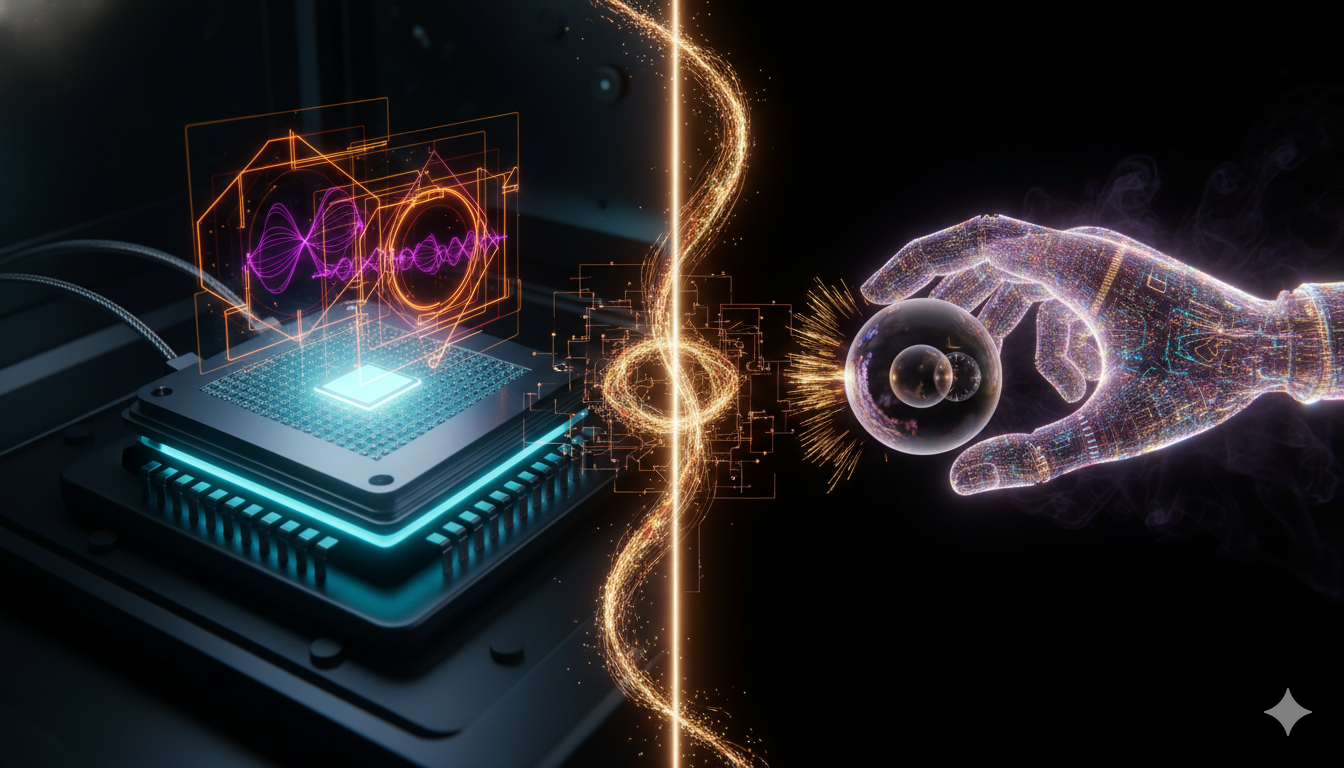
Quantum Control: Unlocking the Power of the Quantum Realm (2026 Update)
Introduction: Quantum Control Becomes the Operating System of the Quantum Age The global quantum technology ecosystem is entering a decisive transition phase. As quantum computing, quantum networking, quantum sensing, and quantum-secure communications move from laboratory experimentation toward early operational deployment, one enabling discipline has emerged as the critical bottleneck separating theoretical promise from scalable reality:…
STRATEGIC SUB-MAGAZINES
Modern military power emerges from the interaction of platforms, people, doctrine, and integration across domains. The Defense & Military Systems magazine is structured into focused sub-magazines that examine how combat capability is built, sustained, and employed across air, land, sea, weapons, and human systems.
Cyber & Information Warfare
Industrial outcomes are shaped as much by incentives, policy, and market structure as by engineering. Price signals, investment cycles, and regulatory frameworks quietly determine which technologies scale, stagnate, or fail.
This sub-magazine examines how markets behave under strategic pressure—where capital flows, how demand signals distort decisions, and why some industries adapt faster than others.
Explore the Cyber & Information Warfare Sub-Magazine →
Security & Threat Management
Modern security is defined by persistence, coordination, and anticipation. This sub-magazine focuses on how threats are identified, mitigated, and managed across institutions, infrastructures, and societies.
Explore the Security & Threat Management Sub-Magazine →
