Introduction: In the age of digital media, video content reigns supreme, captivating audiences across platforms and reshaping the way we communicate. Yet, the process of creating compelling videos has traditionally been labor-intensive, requiring specialized skills and resources. Enter AI-powered video generation—a revolutionary technology that is democratizing content creation and unleashing …
Read More »TimeLine Layout
July, 2024
-
8 July
Revolutionizing Energy Distribution: DARPA’s POWER Initiative to Beam Electricity Across Military Theaters
Energy is a critical resource for military operations, particularly in remote and isolated areas where supply lines are precarious. The need for fuel convoys in such regions not only incurs high costs but also exposes troops to improvised bomb attacks, leading to unnecessary casualties. To address this challenge, the Defense …
Read More » -
7 July
Unleashing the Power of 6G BRAINS: Revolutionizing Intelligent Wireless Connectivity
Introduction: In a world where connectivity reigns supreme, envisioning a future where machines communicate effortlessly, factories operate autonomously, and cities thrive on seamless data exchange is no longer a distant dream—it’s the ambitious mission of the 6G BRAINS project. Spearheaded by innovative minds at the forefront of wireless communication research, …
Read More » -
7 July
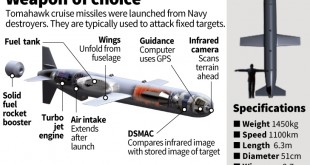
The Evolution of Cruise Missiles: From Precision Strikes to Hypersonic, AI-Enabled Powerhouses
Introduction: In recent years, the landscape of military technology has been undergoing a rapid transformation, with cruise missiles emerging as one of the most formidable and versatile weapons in modern warfare. Once confined to relatively short ranges and limited capabilities, cruise missiles have evolved into long-range, hypersonic, nuclear-powered, and AI-enabled …
Read More » -
6 July
Revolutionizing Military Operations: The Neurotech Race for Brain-Computer Interfaces to Control Multiple Robots with the Speed of Thought
The concept of controlling machines with our minds has been the stuff of science fiction for decades, but thanks to advances in neurotechnology, it is becoming a reality. Brain-Computer Interface (BCI) technology has been developing rapidly in recent years, with a growing number of researchers and companies working on developing …
Read More » -
6 July
Navigating the Landscape: Exploring the Global Artificial Intelligence in Military Market
In recent years, the integration of artificial intelligence (AI) into military operations has emerged as a transformative force, reshaping the landscape of modern warfare. From enhancing battlefield decision-making to revolutionizing defense systems, AI technologies are driving unprecedented advancements in military capabilities worldwide. As nations seek to gain strategic advantages and …
Read More » -
5 July
Touch Redefined: Exploring Tactile Sensor Systems Emulating Human Fingertip Sensitivity
Introduction: In the rapidly evolving landscape of robotics and artificial intelligence, scientists and engineers are continually striving to bridge the gap between human capabilities and machine functionalities. A notable breakthrough in this quest is the development of tactile sensor systems that meticulously mimic the sensitivity and dexterity of the human …
Read More » -
4 July
Improving Arctic Communication Infrastructure Amidst Growing Geostrategic Importance
Introduction: The Arctic region, once a remote and frozen expanse, is now emerging as a pivotal arena for geopolitical competition and militarization. In this evolving landscape, secure satellite communications play a critical role in enabling military operations, ensuring situational awareness, and facilitating information sharing. However, the extreme environmental conditions and …
Read More » -
4 July
Securing the Spectrum: Unveiling the Advanced Dynamic Spectrum Reconnaissance (ADSR) in AI-Driven Electronic Warfare
Introduction: U.S. soldiers in Europe have recently conducted field tests of the Advanced Dynamic Spectrum Reconnaissance (ADSR), an artificial intelligence (AI) system designed to enhance wireless network security in contested areas, as reported by the 7th Army Training Command. The ADSR, developed in collaboration with the Pathfinder program and researchers …
Read More » -
3 July
Unleashing the Power of Multimode Optical Fiber Lasers: A Defense Against Low-Cost Drones and Beyond
In the evolving landscape of laser technology, multimode optical fiber lasers emerge as key players, promising to enhance the power of fiber lasers while maintaining beam quality. This innovation not only holds significance for applications in defense against low-cost drones but also extends its reach to areas like remote sensing. …
Read More »
 International Defense Security & Technology Your trusted Source for News, Research and Analysis
International Defense Security & Technology Your trusted Source for News, Research and Analysis