Blockchain technology of decentralized digital currency to enhance security of additive manufacturing in Internet of Things to Military 3D printing

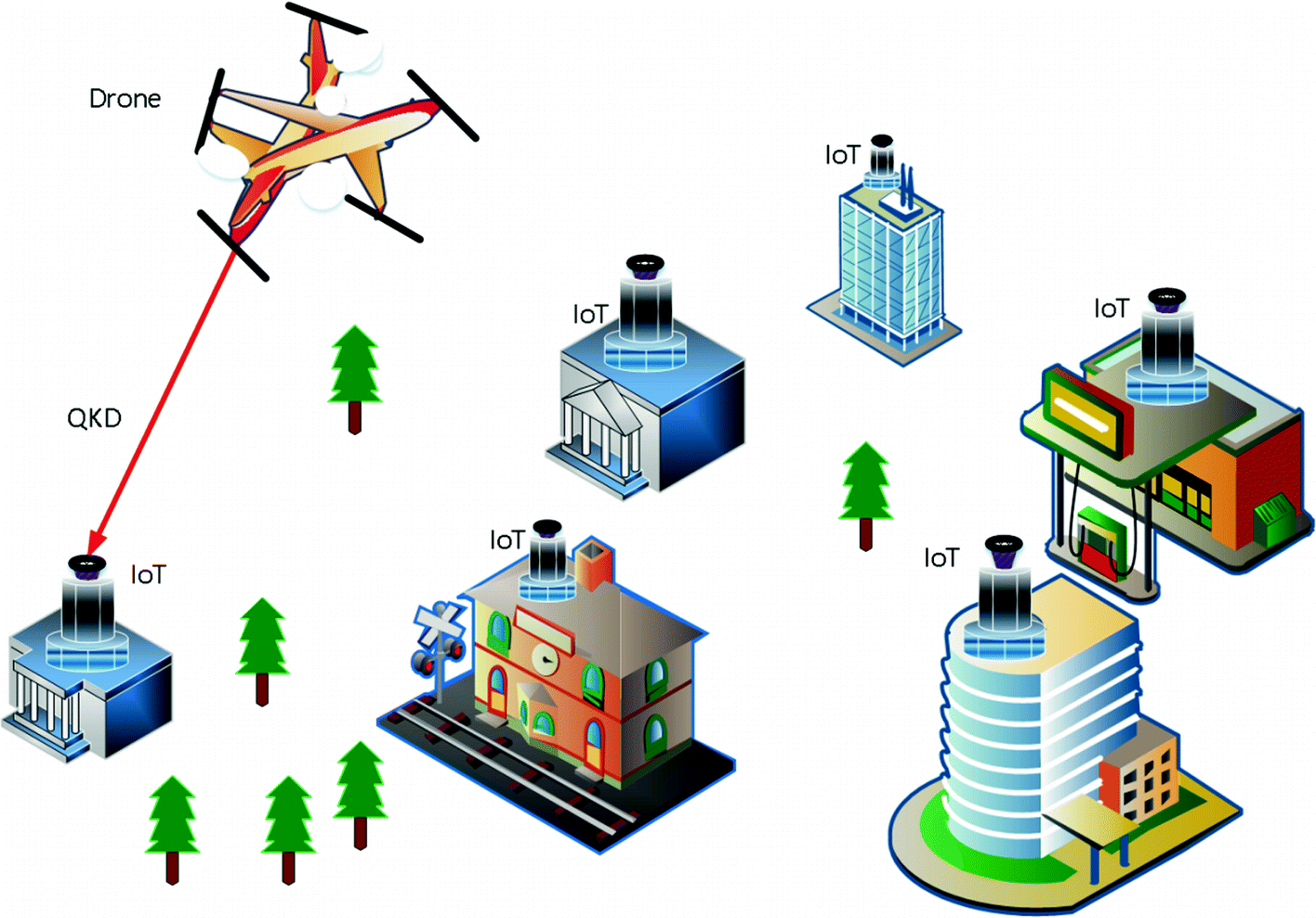
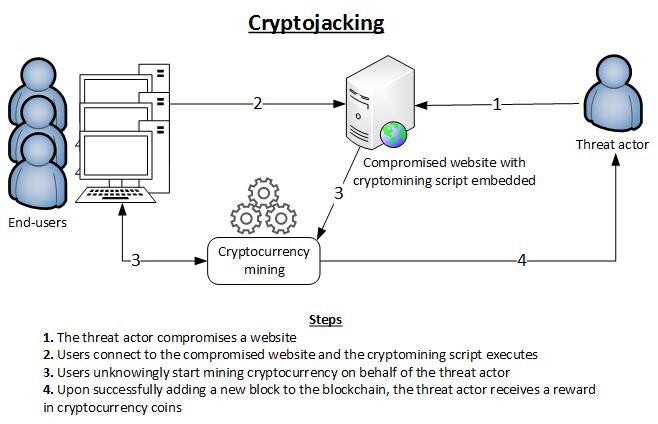
Blockchain is based on open, global infrastructure, decentralized public ledger of transactions that no one person or company owns or controls, ensures security of transfer of funds through public and private cryptology and third parties to verify that they shook,…...