DARPA’s INTERCEPT developing adaptive medical countermeasures to protect soldiers from viral diseases like Zika & Ebola.
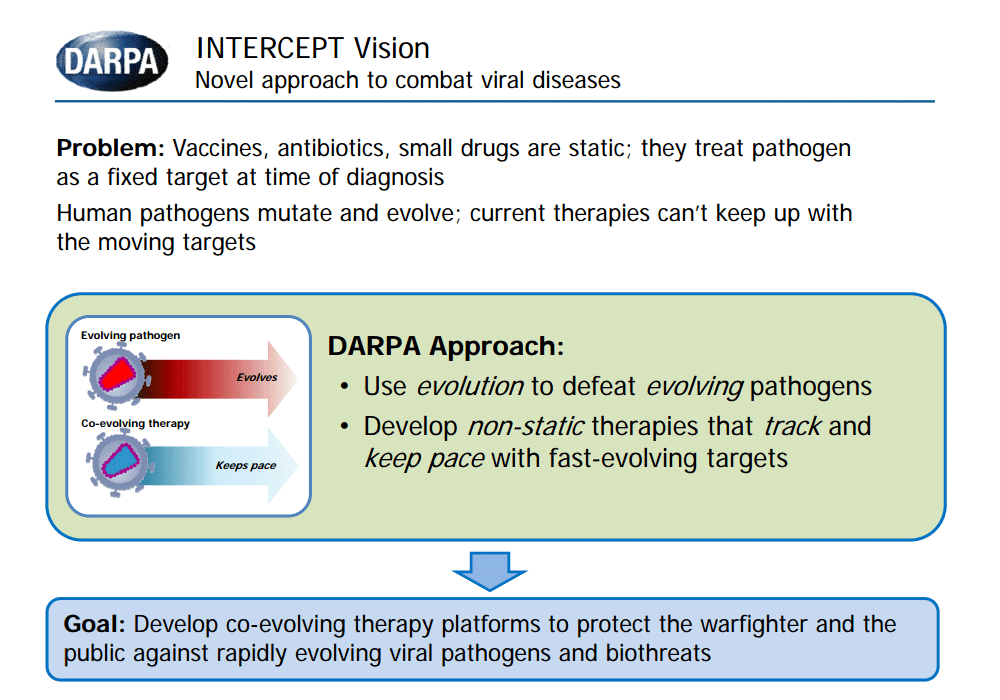
The viral diseases like Zika. Ebola. Dengue. Influenza. Chikungunya pose serious health threats to U.S. troops, as well as to civilian populations in the United States and around the world, says DARPA. Vaccines exist for but a few of these…...