Cyber Red teaming or penetration testing uncovers the vulnerabilities of an organisation, NEC develops automated tool
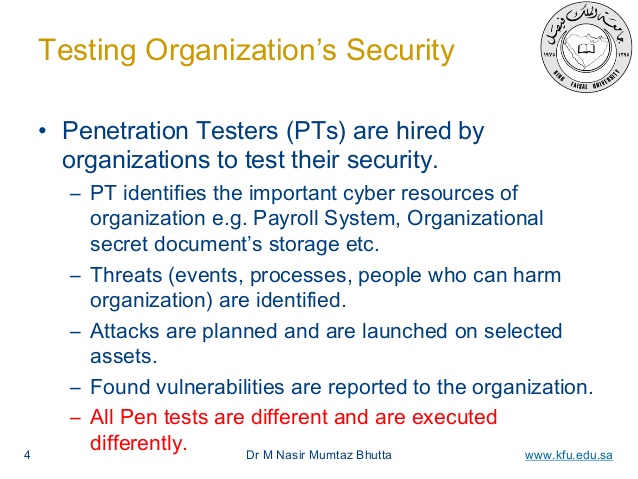
Cyberattacks are being conducted daily on any type of target, and any notion that a state of full cyber security can be reached is a mere illusion. Cybersecurity is about managing risks and to ascertain that, to a certain extent,…...