Countries race to employ Blockchain, the virtual currencies technology, for tamper-proof military systems and cybersecurity
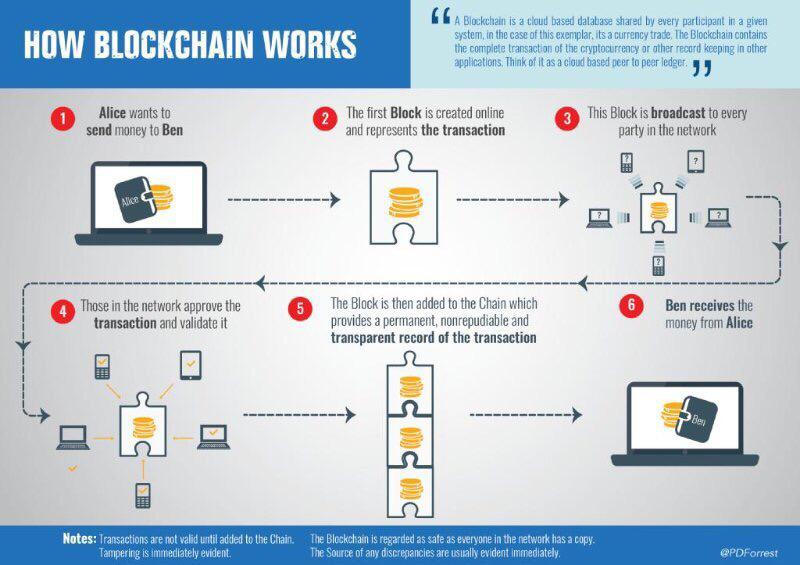
Blockchain is a transformative technology for the two billion people in the world currently underserved by financial institutions. The technology has the potential to enhance privacy, security and freedom of conveyance of data. Blockchain is based on open, global infrastructure,…...