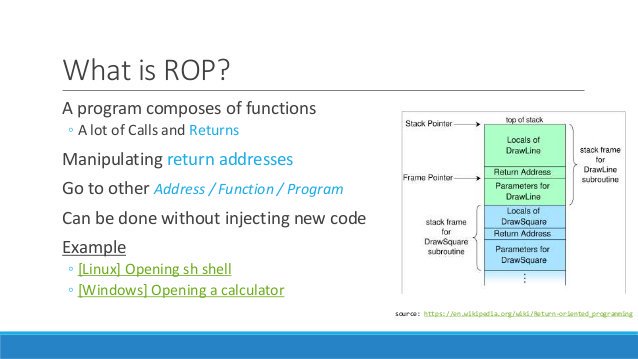
Today’s cybersecurity playing field is fundamentally asymmetric. Attackers are easily able to identify weaknesses in a target system once they have access to its code and configuration. As a result, defenders are perpetually playing a game of catch-up to secure their systems post-attack. ROP attacks are particularly insidious in that they harness software components…