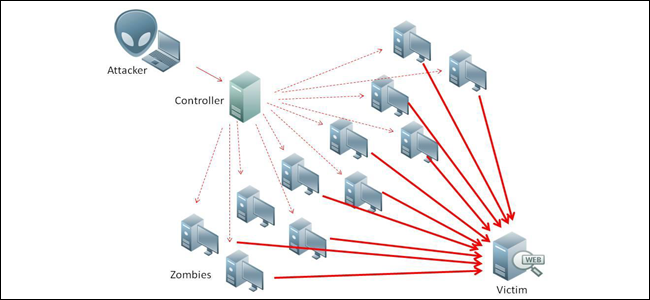
As the name suggests, denial-of-service (DoS) attacks are designed to deny legitimate users access to websites and services by overwhelming them with illegitimate connections, requests and traffic. A distributed denial-of-service attack is when the DoS attacks are being done by multiple attackers all trying to attack a source at once, be it from real hackers or from a single entity and their network of bots.
Such attacks are orchestrated by sets of networked hosts that collectively act to disrupt or deny access to information, communications, or computing capabilities, generally by exhausting targets’ critical resources such as bandwidth, processor capacity, or memory. An attacker uses a non-trivial amount of computing resources, which they either built themselves or, more commonly, by compromising vulnerable PC’s around the world, to send bogus traffic to a site. If the attacker sends enough traffic, legitimate users of a site can’t be serviced.
DDoS attacks are hard to trace, difficult to prevent, easy to carry out and increasingly affordable to acquire. This makes them one of the top methods of attack for extortionists, political activists (hacktivists) and disgruntled individuals/groups. DDOS attacks becoming more widespread, powerful, and persistent and sophisticated. Akamai recently monitored a sustained attack against a media outlet of 363 gigabits per second (Gbps)—a scale which few companies, let alone a nation, could cope with for long. Networks specialist Verisign reports a shocking 111% increase in DDoS attacks per year, almost half of them over 10 Gbps in scale—much more powerful than previously. The top sources are Vietnam, Brazil and Colombia.
For the Defense Department, the stakes are higher. DDoS attacks can disrupt critical command and control networks, interfere with situational awareness, jeopardize missions, and put lives at risk. The starting point in serious cyber warfare may well be to trip the power stations which power the data centres involved with the core routing elements of the network. DDoS attack on the national grid could make it easier for hackers to neutralize the backup power and trip the system.
William Cohen, the former U.S. secretary of defense, recently predicted such a major outage would cause large-scale economic damage and civil unrest throughout a country. In a war situation, this could be enough to bring about defeat. Janet Napolitano, a former secretary at the U.S. Department of Homeland Security, believes the American system is not well enough protected to avoid this.
The international terrorist organizations can use the DDoS to target the web sites or Internet systems of U.S. government and military, the results and losses will be disastrous and unimaginable. Therefore, for guarding both American national security and commercial security, it is really important to detecting, preventing and mitigating the DDoS attacks.
DARPA’s XD3 program looks to develop technologies that: Thwart DDos attacks by dispersing cyber assets (physically and/or logically) to complicate adversarial targeting, disguise the characteristics and behaviors of those assets to confuse or deceive the adversary, blunt the effects of attacks that succeed in penetrating other defensive measures by using adaptive mitigation techniques on endpoints such as mission-critical servers.