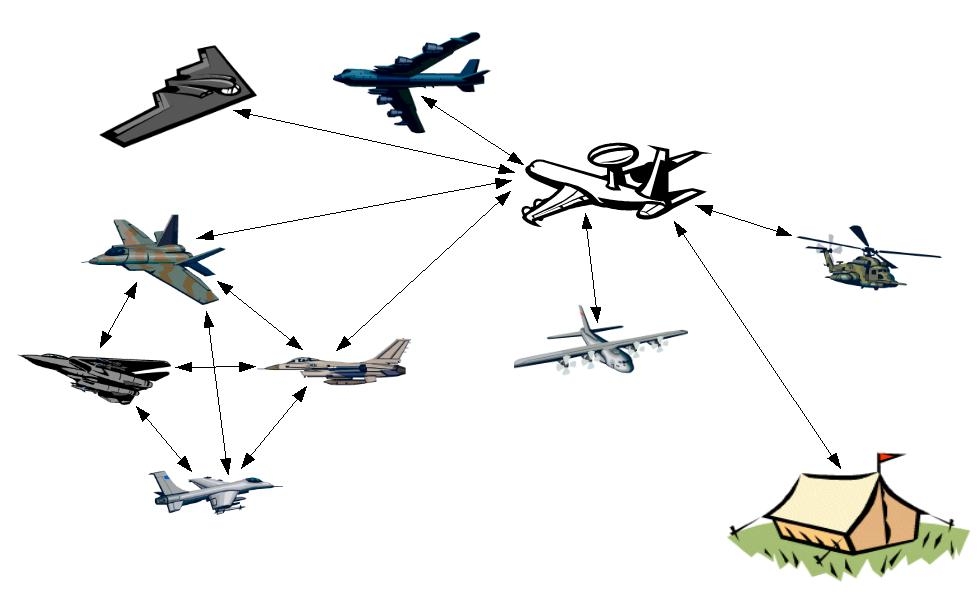
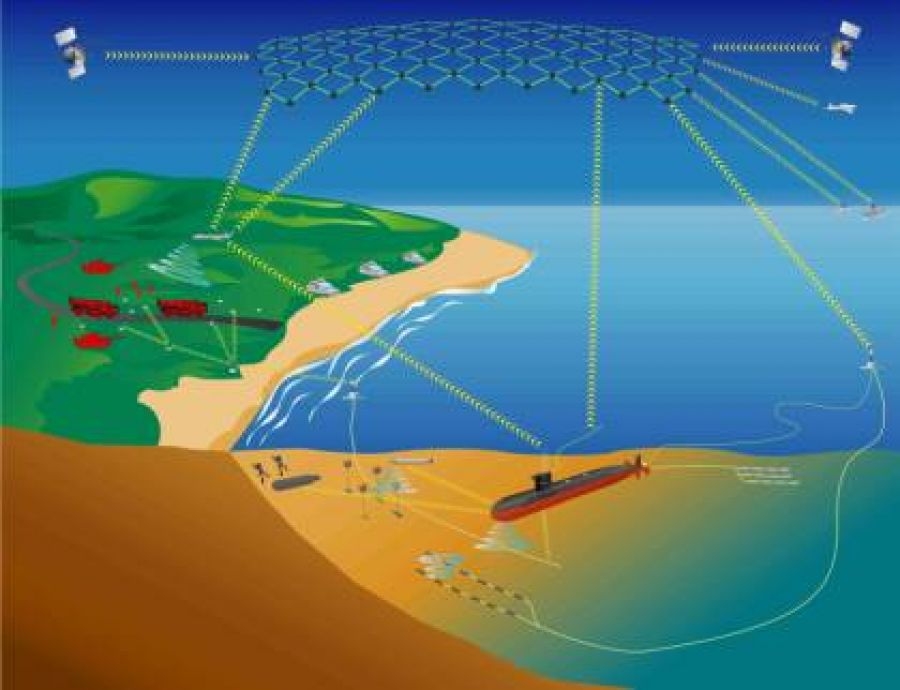
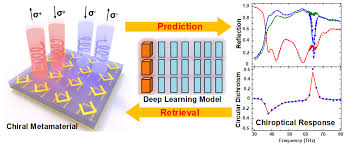
Next generation Military Communications technologies enabling high-throughput mobile, secure, survivable, seamless, in congested and contested environments

Communications is vital for War fighters to exchange voice and data, command and control and situational awareness data and video. The vision of Communications area is to provide reliable communication from anywhere to everywhere from war fighters to supreme commander…...