Understanding the Cyber Kill Chain: A Strategic Framework to Combat Cyber Threats

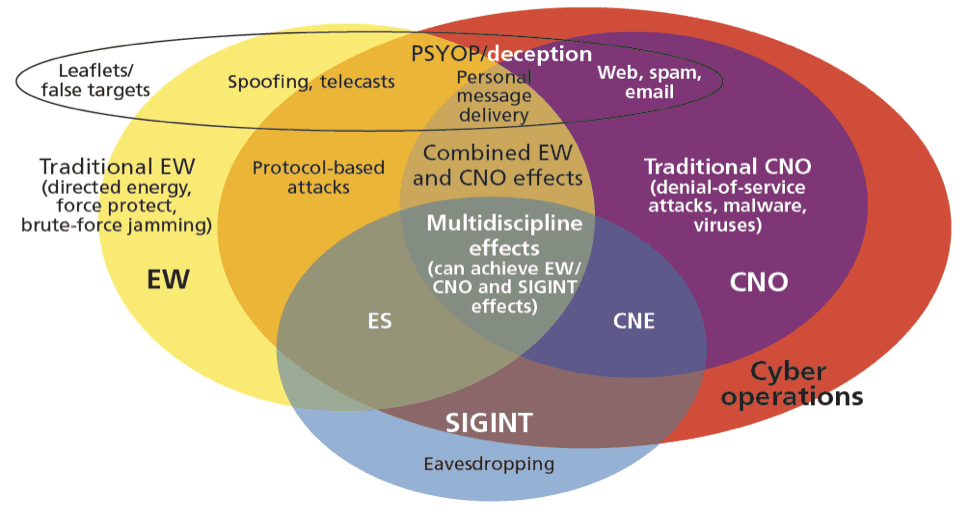
Cyber warfare refers to the strategic use of technology to attack nations, governments, or individuals, causing disruption and damage comparable to traditional warfare. Over the years, it has evolved into a complex battleground where both state and non-state actors deploy…...