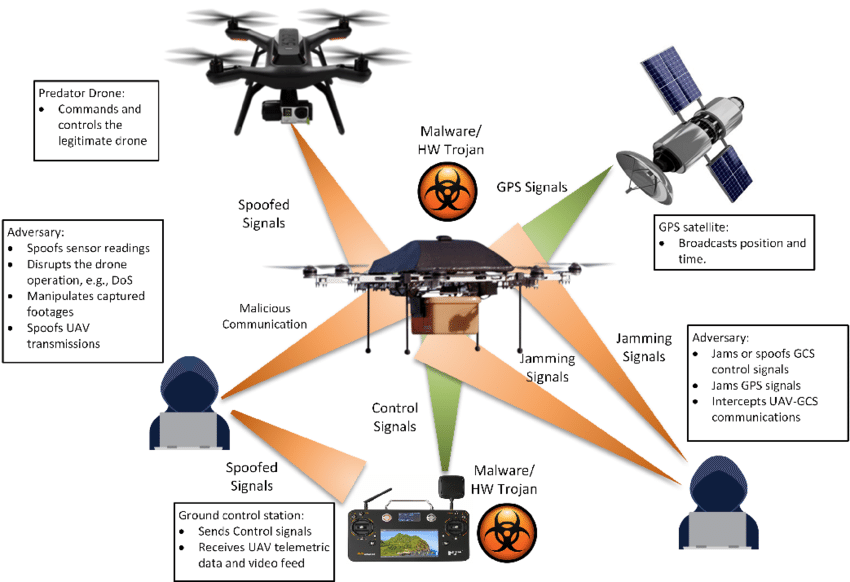
Software is becoming more vulnerable to cyber attacks, CVE identifies common vulnerabilities exploited by state and nonstate actors
In computer security, a vulnerability is a flaw or weakness in a system or network that could be exploited by a threat actor, such as an attacker, to manipulate or cause damage to the system in some way. To exploit a…...