Artificial Intelligence and Machine Learning are enabling the future of fully automated Cyber Security
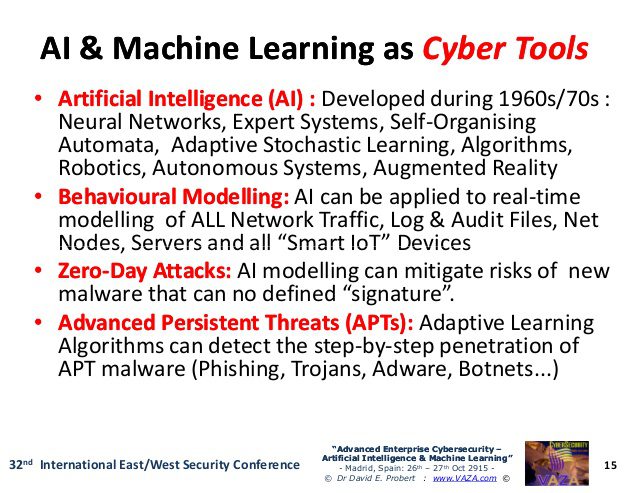
AI emulates human cognition – i.e. learning based on experience and patterns, rather than by inference (cause and effect). Artificial intelligence covers everything from machine learning to business intelligence. Machine learning is a branch of artificial intelligence (AI) that refers…...