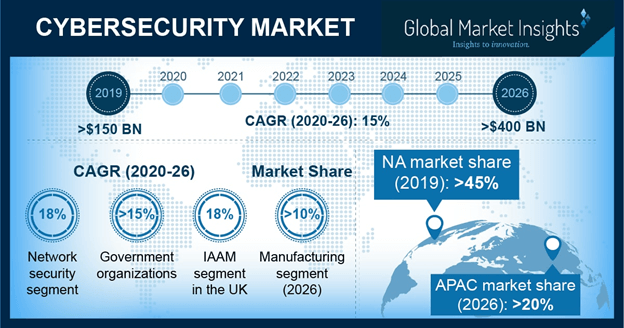
European Union (EU) cyber security and EDA cyber defence strategy calls for proactive and reactive cyber defence technology and Cyber Situation Awareness (CySA) operational capability.

The pandemic, which moved citizens’ lives into the digital sphere, saw a rise in security breaches within European businesses and institutions. Cyber attacks against key European sectors doubled in 2020. Significant malicious attacks against key sectors doubled in Europe –…...