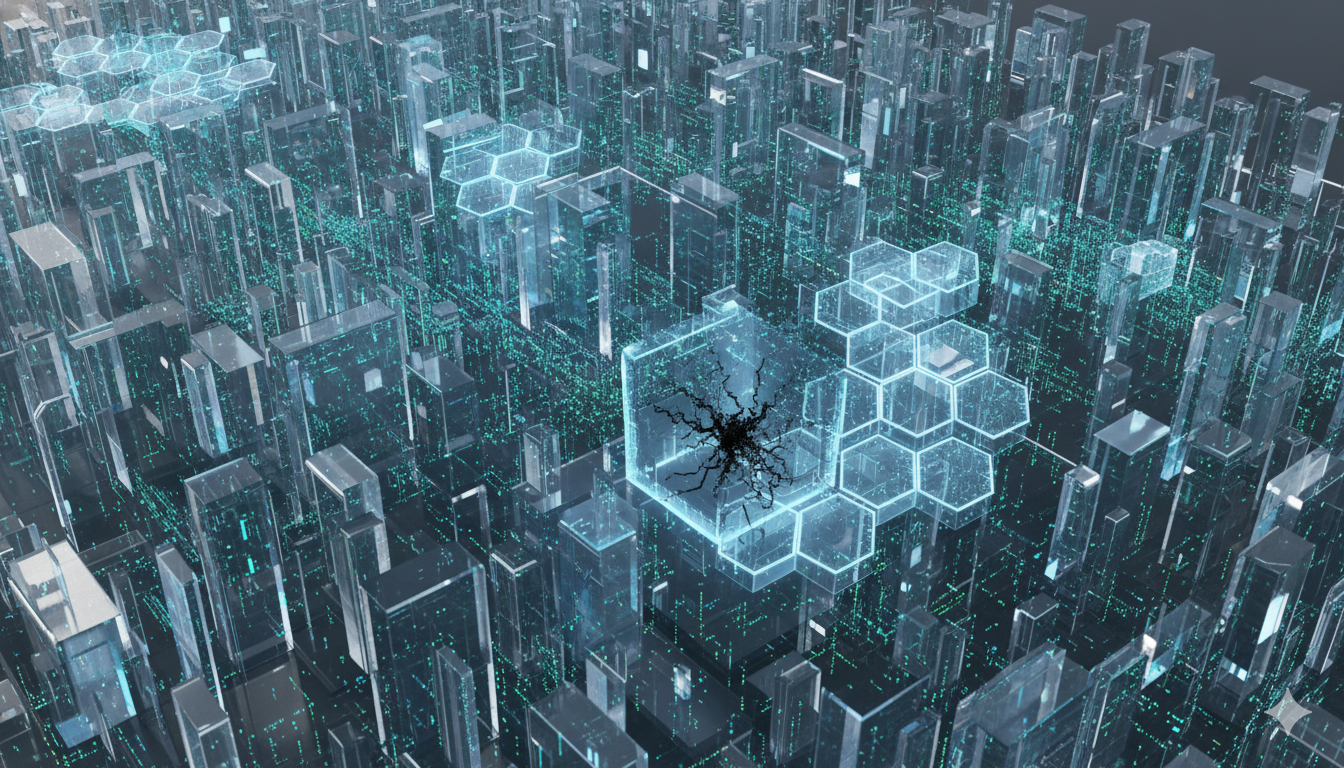
In the relentless cat-and-mouse contest between cyber attackers and defenders, a fundamental asymmetry has long shaped the battlefield. An attacker needs to discover only a single vulnerability to gain entry into a system, while defenders must secure every possible entry point. This imbalance has produced a steady stream of major cyber incidents that have disrupted…