New technologies enable Very Long Range Air-to-Air missiles to reach targets at longer ranges, with heavier payloads and with greater precision
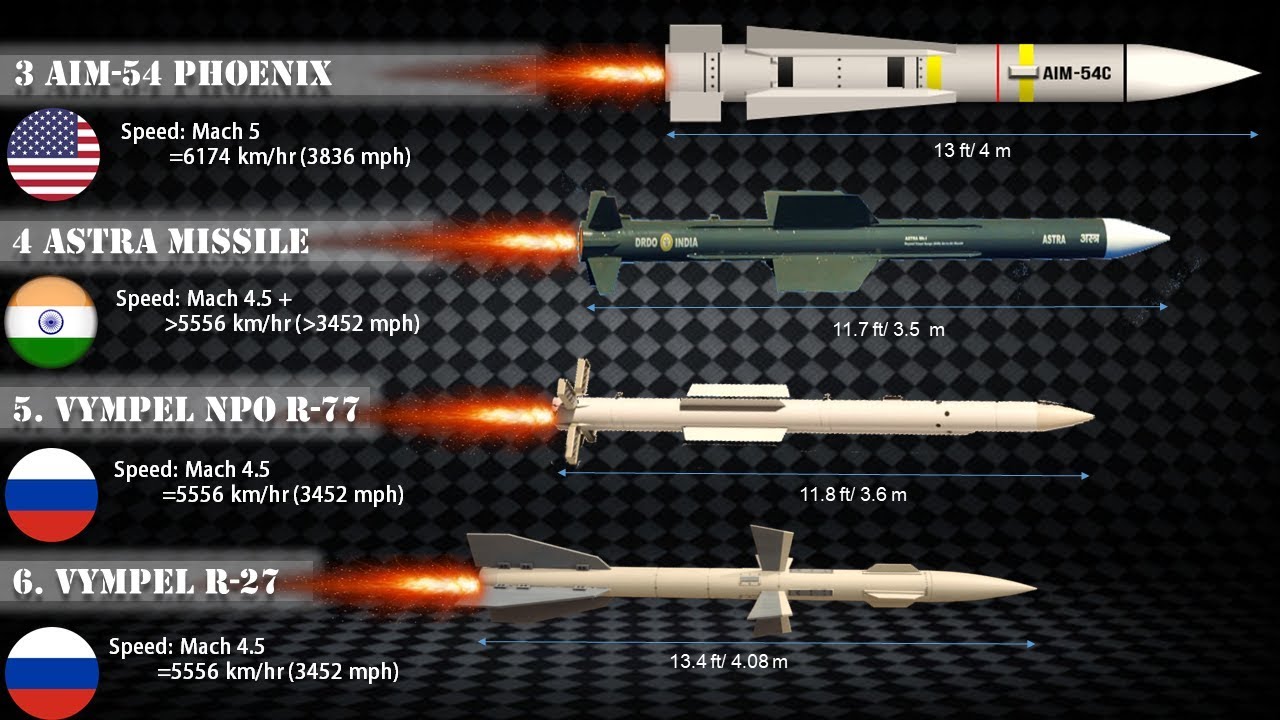
The Air-to-Air Missile (AAM) is a potent guided missile that changed the shape of aerial combat forever. Capable of destroying fast and maneuverable jet fighters at ranges sometimes exceeding 100 kilometers, these high-tech weapons dominate the skies. The probability of…...