Tungsten, the wonder military material used in armor-piercers, armored tanks, to Hypervelocity projectiles is controlled by China
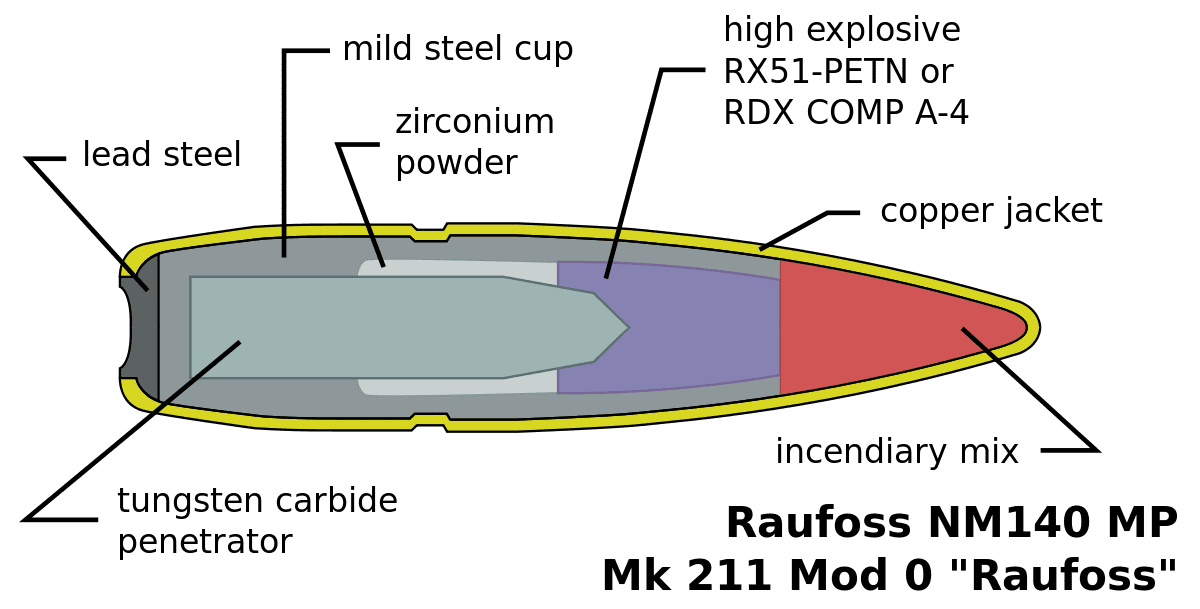
Tungsten is one of the hardest metals on the earth, and many scientists compare it to diamond. Tungsten is a dull silver-colored metal with the highest melting point of any pure metal. Pure tungsten melts at a whopping 6,192 degrees…...