Quantum-Shielded Networks: The Future of IoT Security in a Connected World

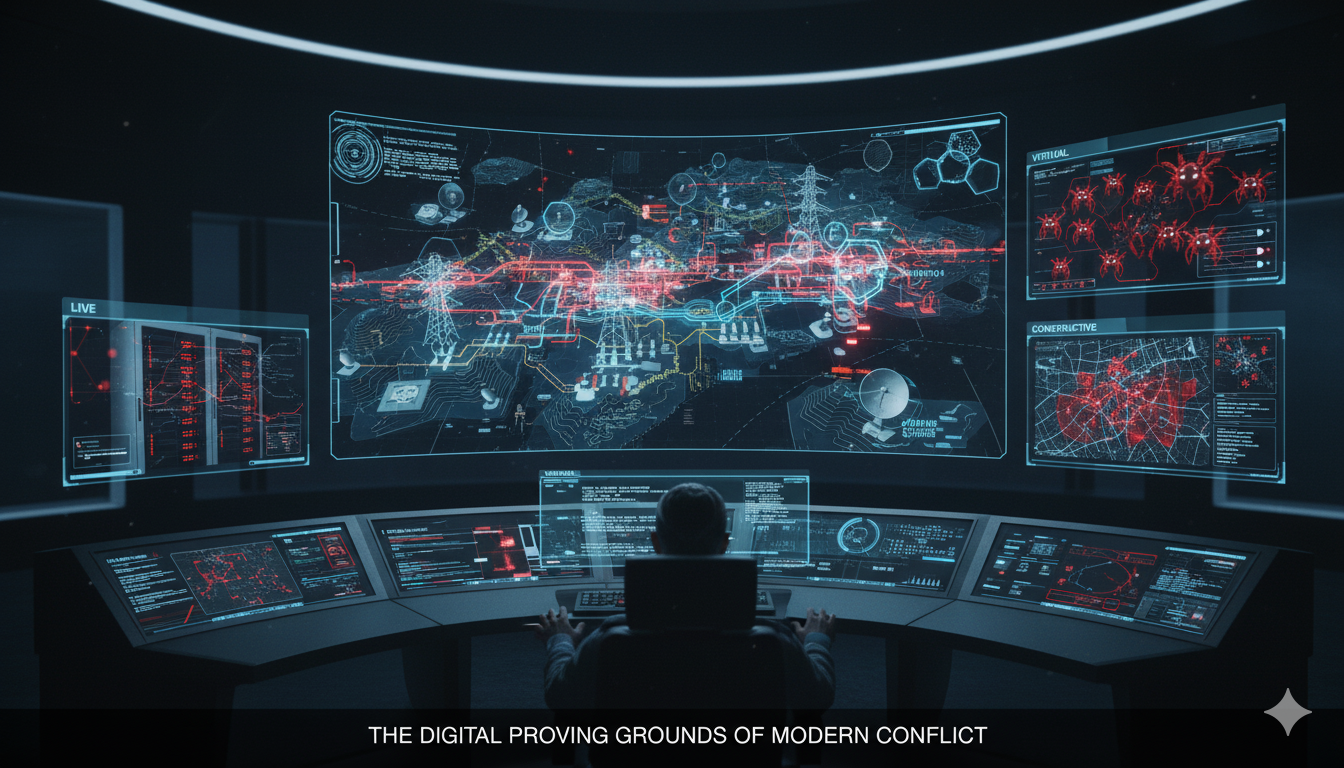
Introduction: The IoT Security Paradox In September 2024, the cybersecurity world was shaken when thousands of pagers and walkie-talkies used by Hezbollah operatives were remotely detonated in a sophisticated cyber-physical attack. Beyond the immediate tactical implications, the incident served as…...