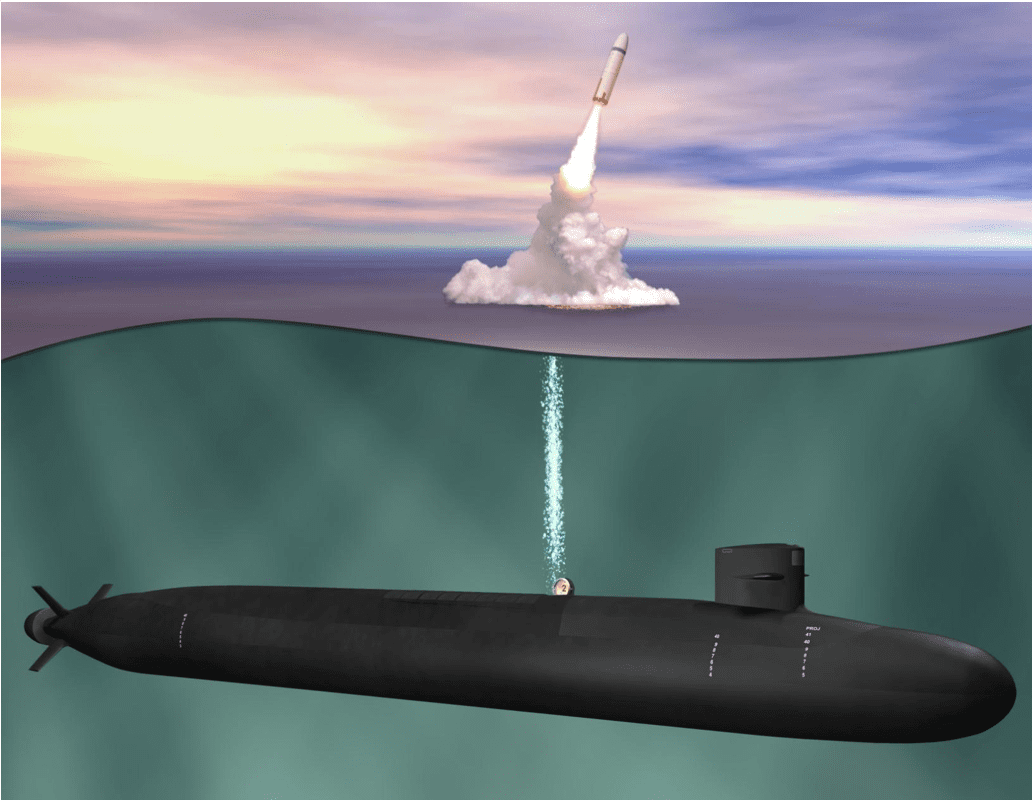
Internet of Nano Things (IoNT) shall impact from Telecom & IT to homeland security to military

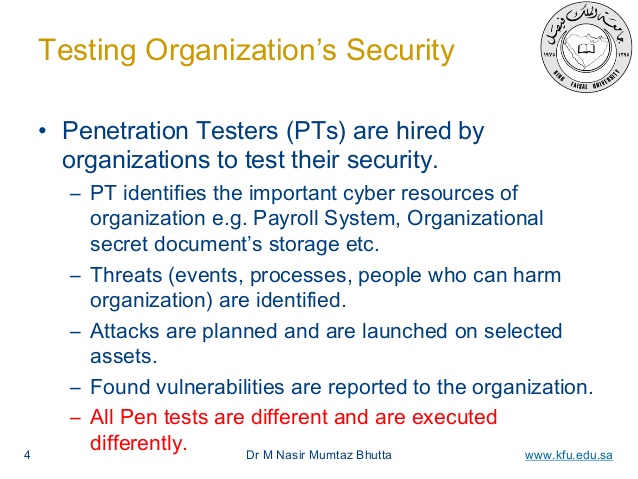
By 2025, it is predicted that there can be as many as 100 billion connected IoT devices or network of everyday objects as well as sensors that will be infused with intelligence and computing capability. These devices shall comprise of…...