Artificial intelligence and data-driven systems are reshaping how decisions are made, risks are assessed, and operations are coordinated across defense, security, and strategic industries. Their power lies not in autonomy alone, but in how information is processed, trusted, and acted upon under pressure.
Rather than replacing human judgment, AI increasingly acts as a force multiplier—compressing decision cycles, revealing hidden patterns, and enabling coordination at scales no human organization can manage unaided.
IDST Intelligence Briefings
Our intelligence briefings examine how AI is integrated into real systems and workflows, including:
- AI-enabled intelligence, surveillance, and reconnaissance (ISR)
- Decision-support and command systems
- Predictive analytics and risk modeling
- Autonomous and semi-autonomous operations
- Human-machine teaming and cognitive augmentation
Each briefing places algorithms within institutional, operational, and ethical contexts.
Why This Magazine Exists
AI is often framed either as a silver bullet that guarantees dominance or as an existential threat that escapes human control. This sub-magazine exists to move beyond both extremes.
Its purpose is to analyze how AI actually works in practice—where it delivers advantage, where it fails, and how organizational design, data quality, trust, and governance determine real outcomes.
What We Track
- Military and intelligence AI applications
- Data pipelines, training regimes, and model reliability
- Human-AI interaction and decision authority
- AI safety, robustness, and adversarial risks
- Institutional adoption, regulation, and ethics
Latest Analysis & Intelligence
-
The Quantum Financial System (QFS): Hype, Reality, and the Future of Quantum-Enabled Finance (2026 Update)
Introduction: Quantum Technology Meets the Future of Global Finance The global financial system is entering one of its most consequential technological transitions since the advent of electronic banking and the internet. Between 2024 and 2026, rapid advances in quantum computing, quantum communications, artificial intelligence, post-quantum cryptography (PQC), digital currencies, and secure distributed infrastructure have fundamentally…
-

Satellite Ground Segment as a Service (GSaaS): The Technology Revolutionizing the Space Economy
From Dedicated Hardware to Cloud-Native, Multi-Orbit Ground Infrastructure Executive Summary The rapid expansion of the space economy—driven by mega-constellations, real-time data applications, and global connectivity demands—is fundamentally reshaping satellite infrastructure. While advances in launch systems and spacecraft often dominate headlines, the true enabler of this transformation lies on the ground. The satellite ground segment, historically…
-

The Algorithmic Assault on Dirty Money: How AI Is Redrawing the Front Lines of Global Financial Defense
Introduction: The Algorithmic Battlespace of Illicit Finance In the contemporary global order, financial systems no longer function merely as economic infrastructure—they have become a primary domain of strategic competition. Capital flows now move at machine speed across jurisdictions, digital platforms, and regulatory boundaries, enabling unprecedented efficiency in legitimate commerce. Yet this same velocity has fundamentally…
-
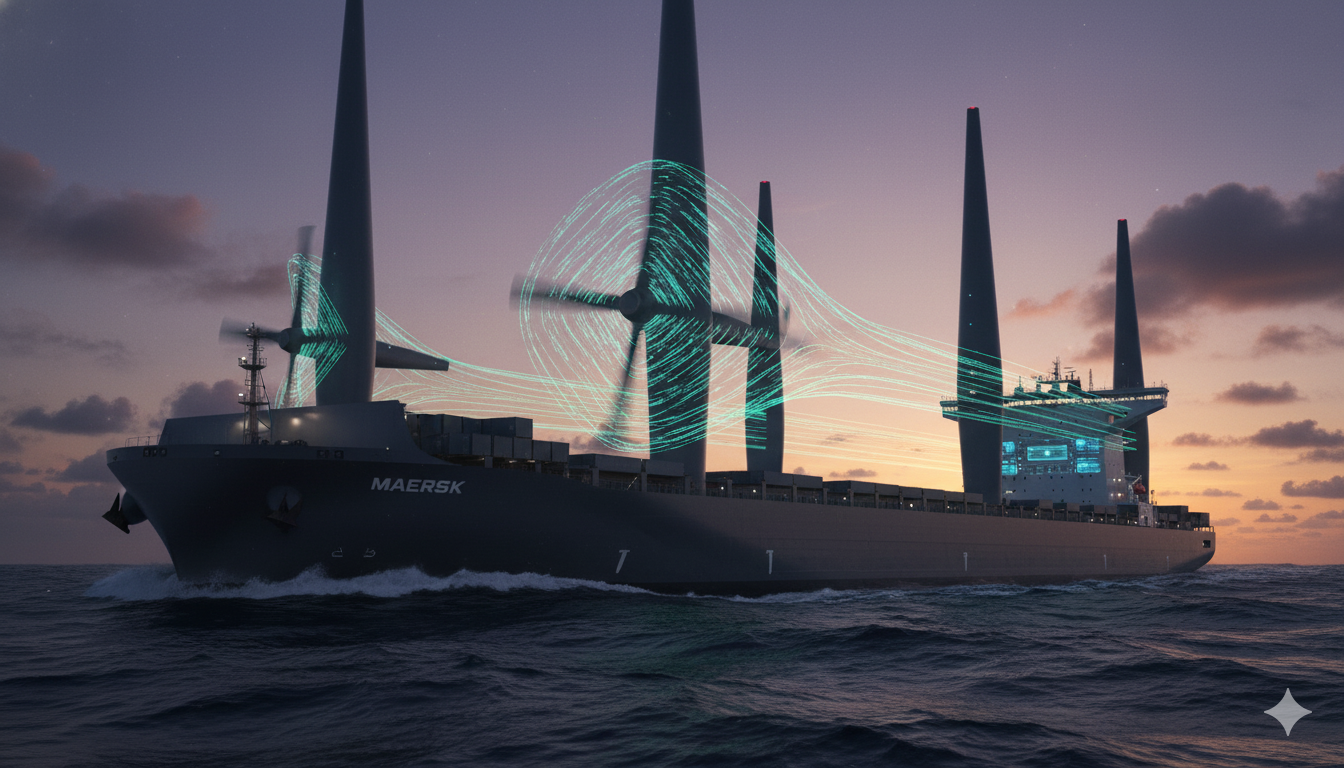
The Flettner Rotor Reborn: Wind, Intelligence, and the Strategic Rewiring of Global Shipping
Introduction: Wind Power as Strategic Infrastructure in a Contested Maritime System At a moment when global shipping sits at the intersection of climate urgency, economic competition, and geopolitical risk, an overlooked truth is re-emerging: control over energy at sea is inseparable from control over trade, resilience, and strategic autonomy. Maritime transport moves more than 80…
-

Weaponized Intelligence: How Terrorist Organizations Are Adapting Artificial Intelligence
Introduction: Terrorism in the Era of Weaponized Intelligence The relationship between terrorism and technology has always been defined by rapid, asymmetric adaptation—but artificial intelligence marks a decisive break from previous cycles of innovation. Unlike earlier tools that enhanced specific functions—communication, financing, or weaponization—AI operates as a meta-capability: it accelerates learning, compresses decision cycles, and enables…
-

The New Digital Battlefield: How Wearable Technology and the Metaverse Are Reshaping Terrorism and Security
Introduction: When the Digital-Physical Boundary Becomes a Battlespace The convergence of wearable technology, immersive digital environments, and artificial intelligence is redefining the architecture of modern security risk. What began as a wave of consumer innovation—smart glasses, fitness wearables, augmented reality platforms, and immersive digital ecosystems—is rapidly evolving into a dual-use infrastructure with direct security implications.…
-

The Digital Proving Grounds: Engineering Trust in an AI-Dominated Battlespace
Introduction: Trust as the Decisive Layer in Algorithmic Warfare The character of warfare is undergoing a structural transformation in which the speed, scale, and complexity of decision-making are increasingly defined by machines rather than humans. Across contested environments—from drone-saturated land battlespaces to sensor-dense maritime theaters and electronically degraded air domains—modern militaries are confronted with an…
Related Domains & Cross-Cutting Themes
Emerging technologies rarely operate in isolation. Their real impact is shaped by integration, governance, and human-system interaction. Cyber security and information warfare, electronic and sensor systems, command and control, autonomous platforms, governance and ethics, and long-term strategic competition
Ethics, governance, and technology control
Industrial scaling and supply-chain constraints
Human–machine teaming and trust
Interoperability across platforms and institutions
Export controls and technological rivalry
Explore the Critical & Emerging Technologies Magazine →
Explore the Industry, Markets & Supply Chains Magazine →
Explore the Space Technology, Defense & Exploration Magazine →
